Cloud-based threat detection
FortiClient's outbreak protection service provides another layer of protection, where FortiClient initiates a real-time cloud lookup of Fortinet's Global Threat Intelligence database so it can detect and block emerging threats and continue to provide the latest protection measures to the endpoint.
FortiClient 6.2.0's malware protection feature includes virus outbreak protection. For each new file downloaded to the endpoint, FortiClient calculates the SHA1 checksum, sends a query to FortiGuard, and temporarily blocks access to the file. If the result from the query indicates that the file is malicious, FortiClient quarantines the newly downloaded file or denies access to it.
To configure cloud-based threat detection:
- In EMS, go to Endpoint Profiles > Manage Profiles. Create a new profile or edit an existing one. Enable Cloud Based Malware Detection and save the profile.
- Create a new endpoint policy or edit an existing one to assign the profile from step 1 to a group or OU.
- In FortiClient, connect to EMS. Once FortiClient receives the profile from EMS, go to the Malware Protection tab to verify that cloud-based malware protection is enabled.

To test the configuration:
- Download a malware file using a web browser. FortiClient detects and quarantines the file using cloud-based threat detection.
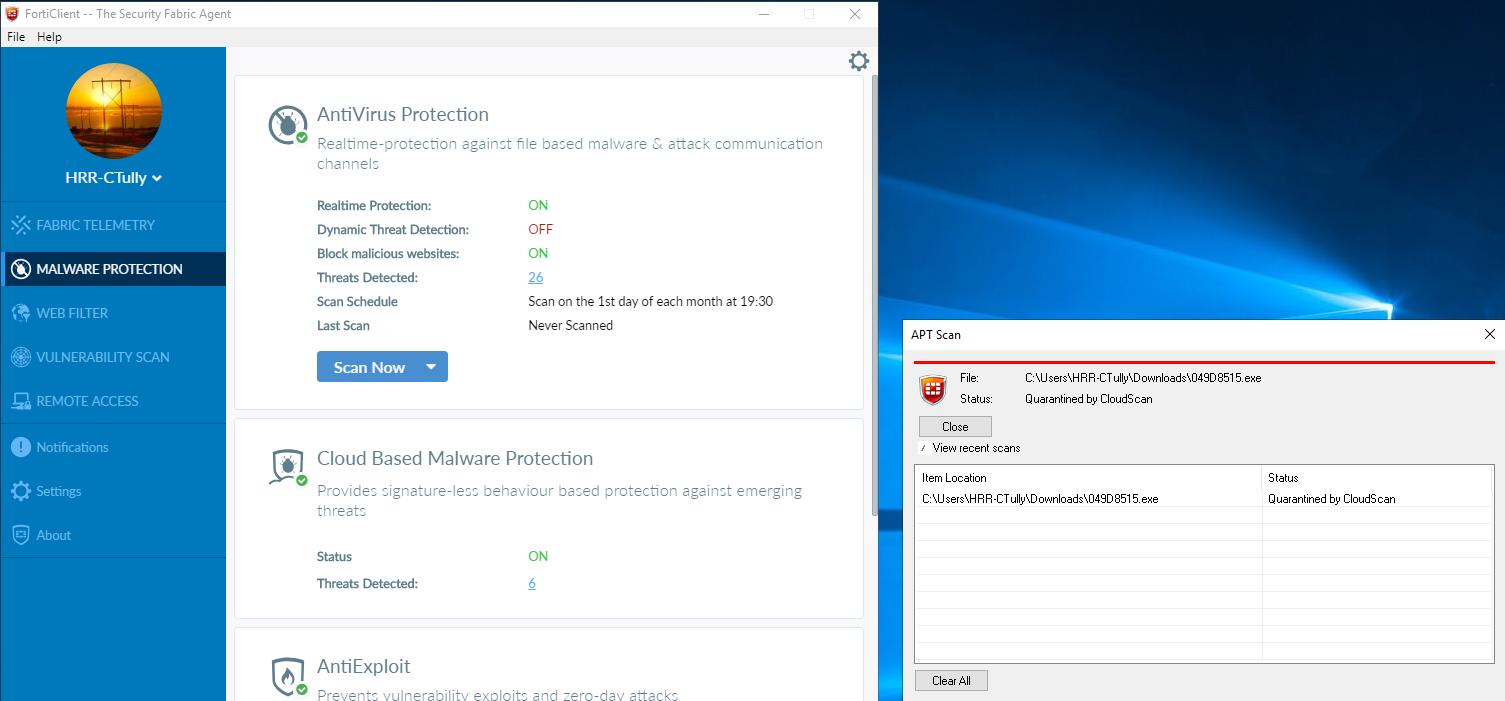
- To view more information for the quarantined file, click the number of Threats Detected on the Malware Protection tab. Click the file name to review it.
- You can also view information about the quarantined file in Quarantine Management > Files in EMS.

- If configured, you can view the event on FortiAnalyzer.


