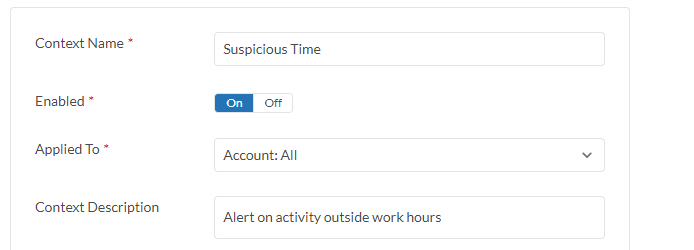
Threat Protection Example - Suspicious Time
Description
Suspicious Time policy monitors cloud account activities outside of regular working hours.
Configuration Steps
- Go to Policy > Threat Protection > Suspicious Time.
- Click on the right arrow key > next to the policy to display configuration setting.
- Click on Enabled toggle button to enable the policy.
- Click Applied To field to select target cloud account.
- In Event field, select Specify events to select event(s) to be associated with the policy or Select all events.
- In Suspicious Time field, select the day in the week and start and end time that the policy monitors the event. (You may repeat this step to add more time)
- Click Save Changes.
- Click the +Add Another to monitor Suspicious Time on a different cloud account (optional).