FortiGate-VM on a Docker environment
Unlike FortiWeb-VM, you cannot deploy FortiGate-VM as a Docker container. However, FortiGate-VM can protect various resources in the Docker environment.
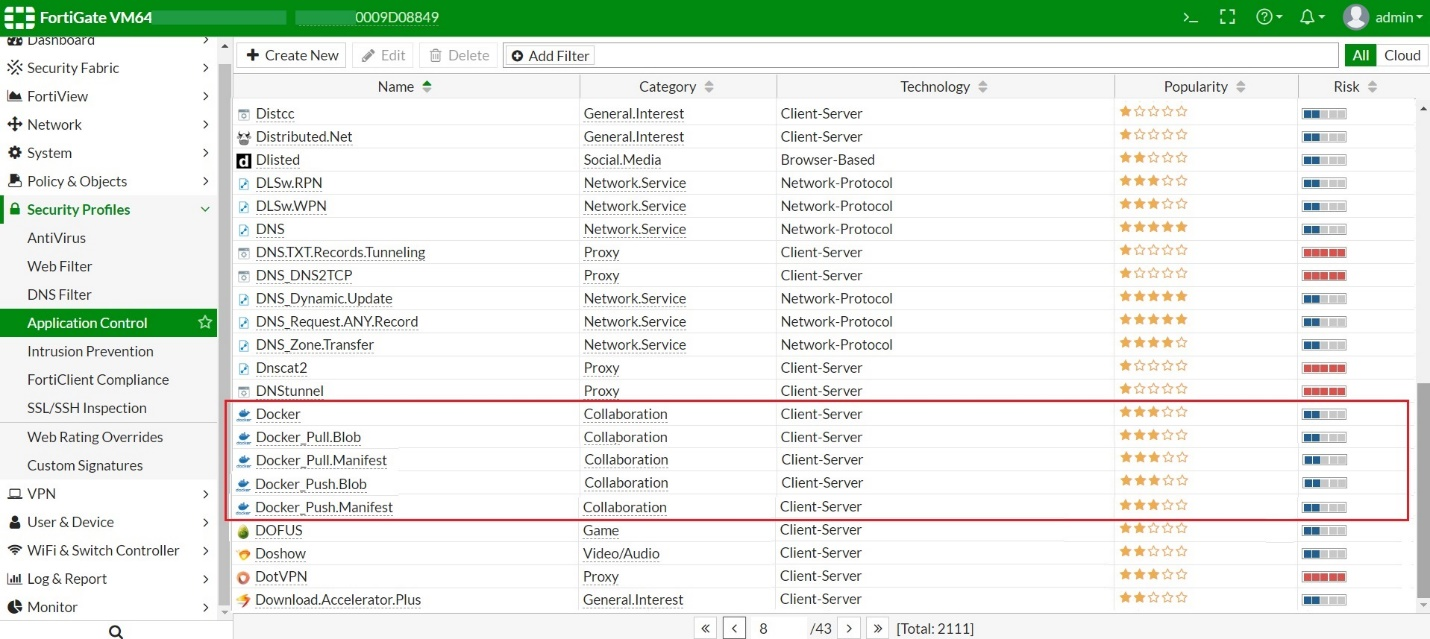
Docker's popularity has seen an increasing volume of activities of downloading and uploading Docker images and their manifests over the Internet. Since the majority of the Docker images in the public registries are vulnerable, it is important to ensure that you only download images from a source where they have already been scanned for vulnerabilities. To help enforce this policy, FortiGate application control has added signatures for Docker traffic.
|
Application control signature |
Indication of an attempt to: |
|---|---|
|
Docker |
Access Docker. |
|
Docker_Pull.Blob |
Pull a blob from Docker. |
|
Docker_Push.Blob |
Push a blob onto Docker. |
|
Docker_Pull.Manifest |
Pull a manifest from Docker. |
|
Docker_Push.Manifest |
Push a manifest onto Docker. |
By updating the signature after initial FortiGate deployment, you should see the Docker-related application controls added in Security Profiles > Application Control.
You can configure firewall policies to allow pulls and pushes with known clean private Docker registries using their IP addresses (or IP addresses except for malicious and blacklisted ones) as either sources or destinations while having awareness of Docker-related application in traffic.
Apart from application control, the FortiGate also scans all traffic in the Docker environment for vulnerabilities and file-based threats using Intrusion Prevention Service and Advanced Malware Protection.

