SD-WAN cloud on-ramp
In this example, you configure a connection to a new cloud deployment that has some remote servers. SD-WAN is used to steer traffic through the required overlay tunnel.
The on-premise FortiGate has two internet connections, each with a single VPN connection. The two VPN gateways are configured on the cloud for redundancy, one terminating at the FortiGate-VM, and the other at the native AWS VPN Gateway.
This example uses AWS as the Infrastructure as a Service (IaaS) provider, but the same configuration can also apply to other services. A full mesh VPN setup is not shown, but can be added later if required.
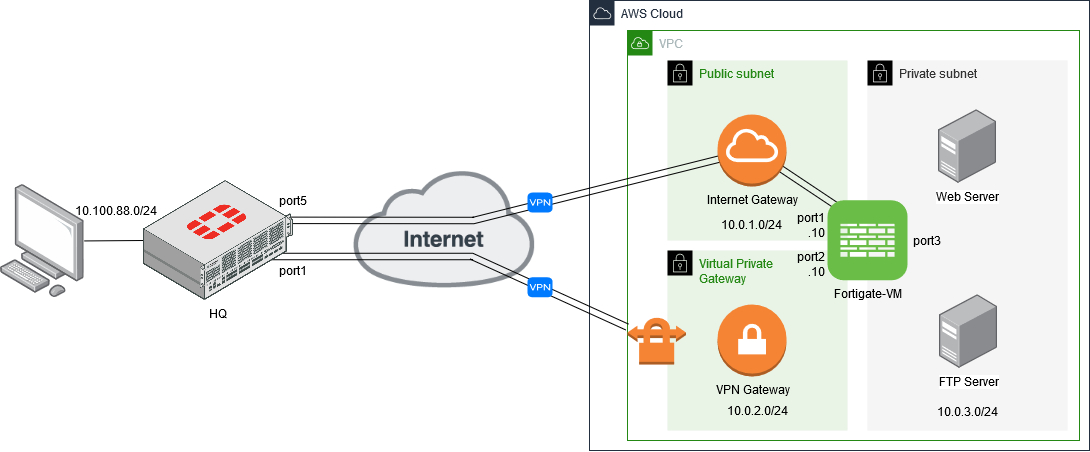
To connect to the servers that are behind the cloud FortiGate-VM, virtual IP addresses (VIPs) are configured on port2 to map to the servers:
- VPN traffic terminating on port1 is routed to the VIP on port2 to access the web servers.
- VPN traffic terminating on the VPN gateway accesses the VIPs on port2 directly.
There are four major steps to configure this setup:
- Configuring the VPN overlay between the HQ FortiGate and cloud FortiGate-VM
- Configuring the VPN overlay between the HQ FortiGate and AWS native VPN gateway
- Configuring the VIP to access the remote servers
- Configuring the SD-WAN to steer traffic between the overlays
After the configuration is complete, verify the traffic to ensure that the configuration is working as expected, see Verifying the traffic.

