Basic ZTNA configuration
To deploy full ZTNA, configure the following components on the FortiGate:
|
|
To configure ZTNA in the GUI, go to System > Feature Visibility and enable Zero Trust Network Access. |
Configure a FortiClient EMS connector
To add an on-premise FortiClient EMS server in the GUI:
-
Go to Security Fabric > Fabric Connectors.
-
Click Create New and click FortiClient EMS.
-
Enter a name for the connector and the IP address or FQDN of the EMS.
-
Click OK.
-
A window appears to verify the EMS server certificate. Click Accept.
See FortiClient EMS for more information.
To add an on-premise FortiClient EMS server in the CLI:
config endpoint-control fctems
edit <name>
set server <server IP or domain>
next
end
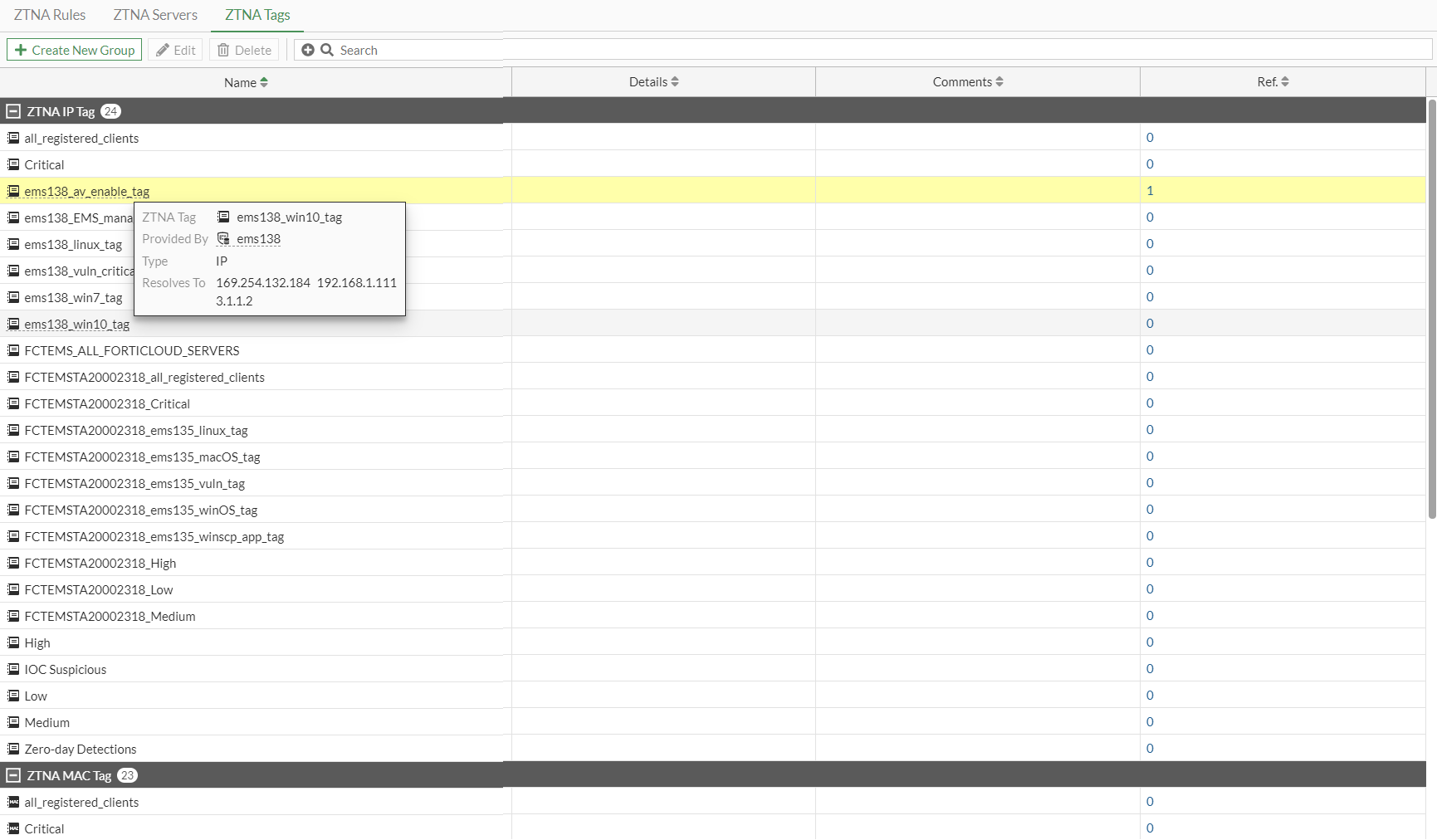
ZTNA tags
After the FortiGate connects to the FortiClient EMS, it automatically synchronizes ZTNA tags.
To view the synchronized ZTNA tags in the GUI:
-
Go to Policy & Objects > ZTNA and select the ZTNA Tags tab.
-
Hover the cursor over a tag name to view more information about the tag, such as its resolved addresses.
To create a ZTNA tag group in the GUI:
-
Go to Policy & Objects > ZTNA and select the ZTNA Tags tab.
-
Click Create New Group.
-
Enter a name for the group and select the group members.
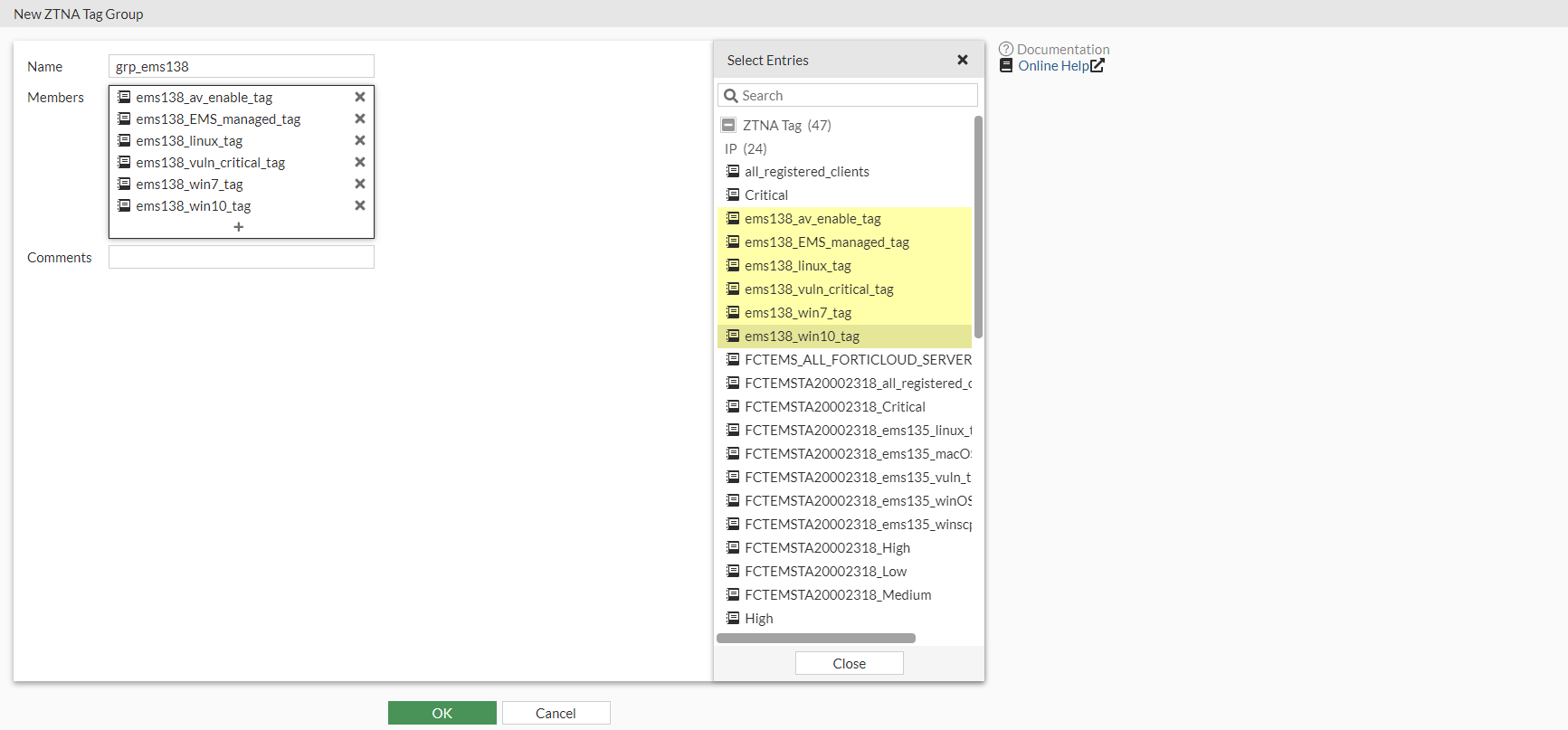
-
Click OK.
To view the synchronized ZTNA tags in the CLI:
# diagnose firewall dynamic address # diagnose firewall dynamic list
To create a ZTNA tag group in the CLI:
config firewall addrgrp
edit <group name>
set category ztna-ems-tag
set member <members>
next
end
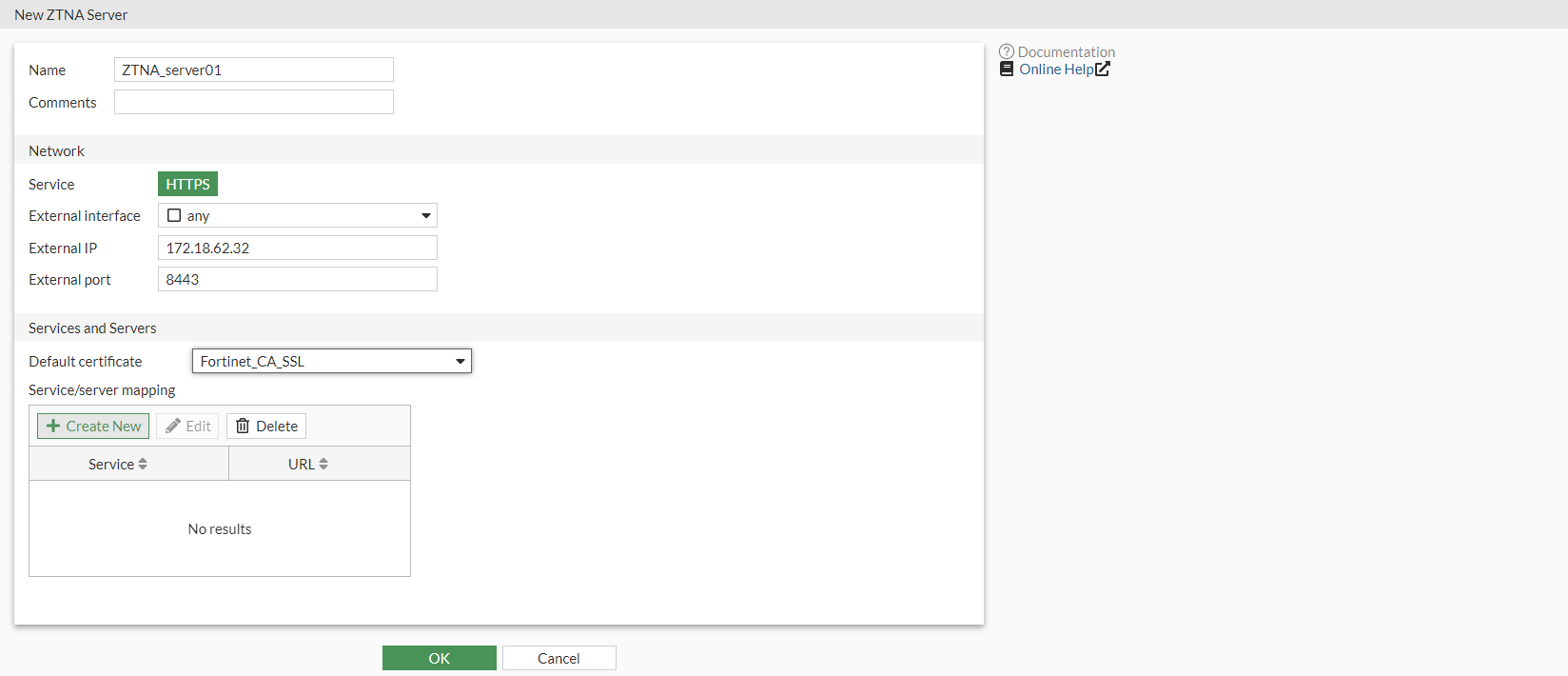
Configure a ZTNA server
To configure a ZTNA server, define the access proxy VIP and the real servers that clients will connect to. The access proxy VIP is the FortiGate ZTNA gateway that clients make HTTPS connections to. The service/server mappings define the virtual host matching rules and the real server mappings of the HTTPS requests.
To create a ZTNA server and access proxy VIP in the GUI:
-
Go to Policy & Objects > ZTNA and select the ZTNA Servers tab.
-
Click Create New.
-
Enter a name for the server.
-
Select an external interface, enter the external IP address, and select the external port that the clients will connect to.
-
Select the Default certificate. Clients will be presented with this certificate when they connect to the access proxy VIP.
-
Add server mapping:
-
In the Service/server mapping table, click Create New.
-
Set Virtual Host to Any Host or Specify.
-
Any Host: Any request that resolves to the access proxy VIP will be mapped to your real servers. For example, if both www.example1.com and www.example2.com resolve to the VIP, then both requests are mapped to your real servers.
-
Specify: Enter the name or IP address of the host that the request must match. For example, if www.example1.com is entered as the host, then only requests to www.example1.com will match.
-
-
Configure the path as needed.
The path can be matched by substring, wildcard, or regular expression. For example, if the virtual host is specified as www.example1.com, and the path substring is map1, then www.example1.com/map1 will be matched.
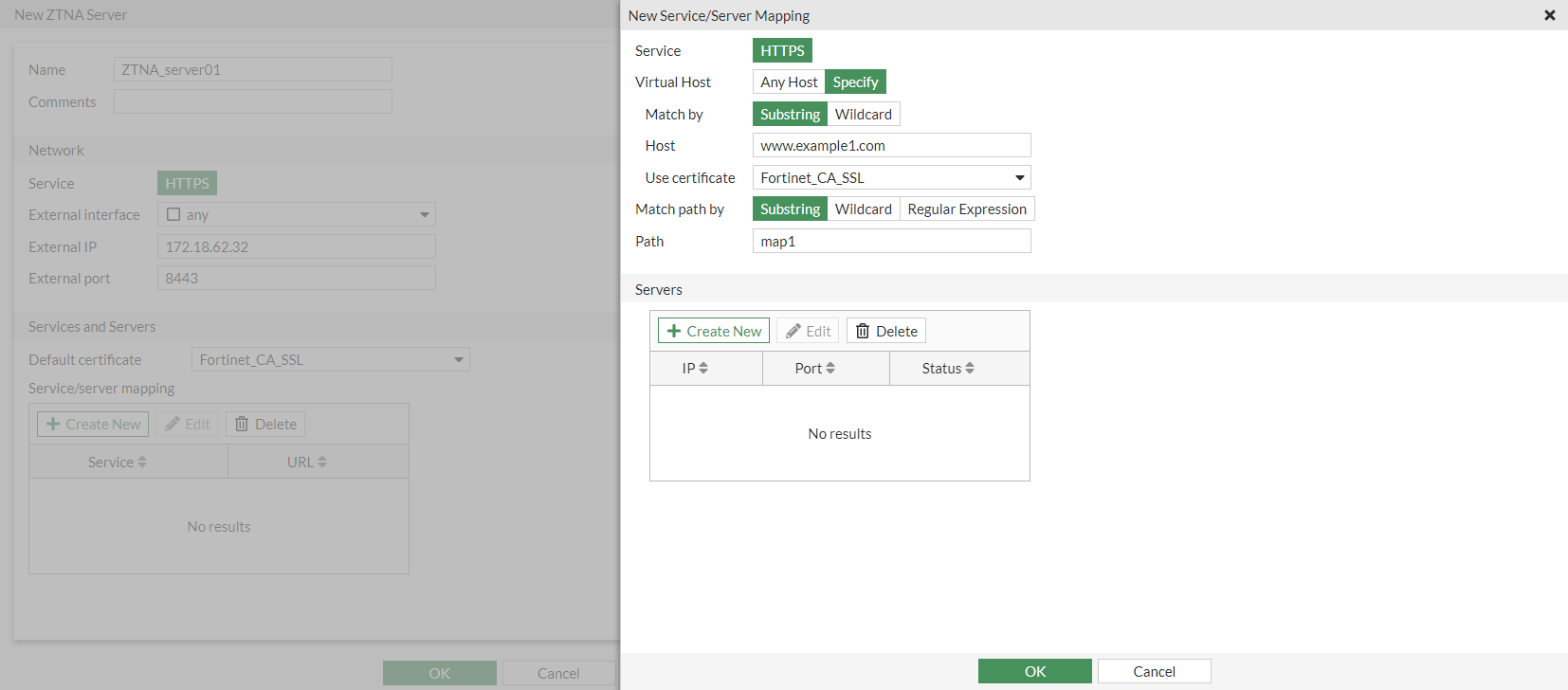
-
Add a server:
-
In the Servers table, click Create New.
-
Enter the server IP address and port number.
-
Set the server status.
-
Click OK.
-
Add more servers as needed.
-
-
Click OK.
-
Add more server mappings as needed.
-
-
Click OK.
To create a ZTNA server and access proxy VIP in the CLI:
-
Configure an access proxy VIP:
config firewall vip edit <name> set type access-proxy set extip <external IP> set extintf <external interface> set server-type { https | ssh } set extport <external port> set ssl-certificate <certificate> next end -
If the virtual host is specified, configure the virtual host:
config firewall access-proxy-virtual-host edit <auto generated when configured from GUI> set ssl-certificate <certificate> set host <host name or IP> set host-type { sub-string | wildcard } next end -
Configure the server and path mapping:
config firewall access-proxy edit <name> set vip <vip name> set client-cert { enable | disable } set empty-cert-action { accept | block } config api-gateway edit 1 set url-map <mapped path> set service { http | https | tcp-forwarding | samlsp } set virtual-host <name of virtual-host if specified> set url-map-type { sub-string | wildcard | regex } config realservers edit 1 set ip <ip of real server> set port <port> set status { active | standby | disable } set health-check { enable | disable } next end set ldb-method static set persistence none set ssl-dh-bits 2048 set ssl-algorithm high set ssl-min-version tls-1.1 set ssl-max-version tls-1.3 next end next endThe load balance method for the real servers can only be specified in the CLI.
Configure a ZTNA rule
A ZTNA rule is a proxy policy used to enforce access control. ZTNA tags or tag groups can be defined to enforce zero trust role based access. Security profiles can be configured to protect this traffic.
To configure a ZTNA rule in the GUI:
-
Go to Policy & Objects > ZTNA and select the ZTNA Rules tab.
-
Click Create New.
-
Enter a name for the rule.
-
Add the ZTNA tags or tag groups that are allowed access.
-
Select the ZTNA server.
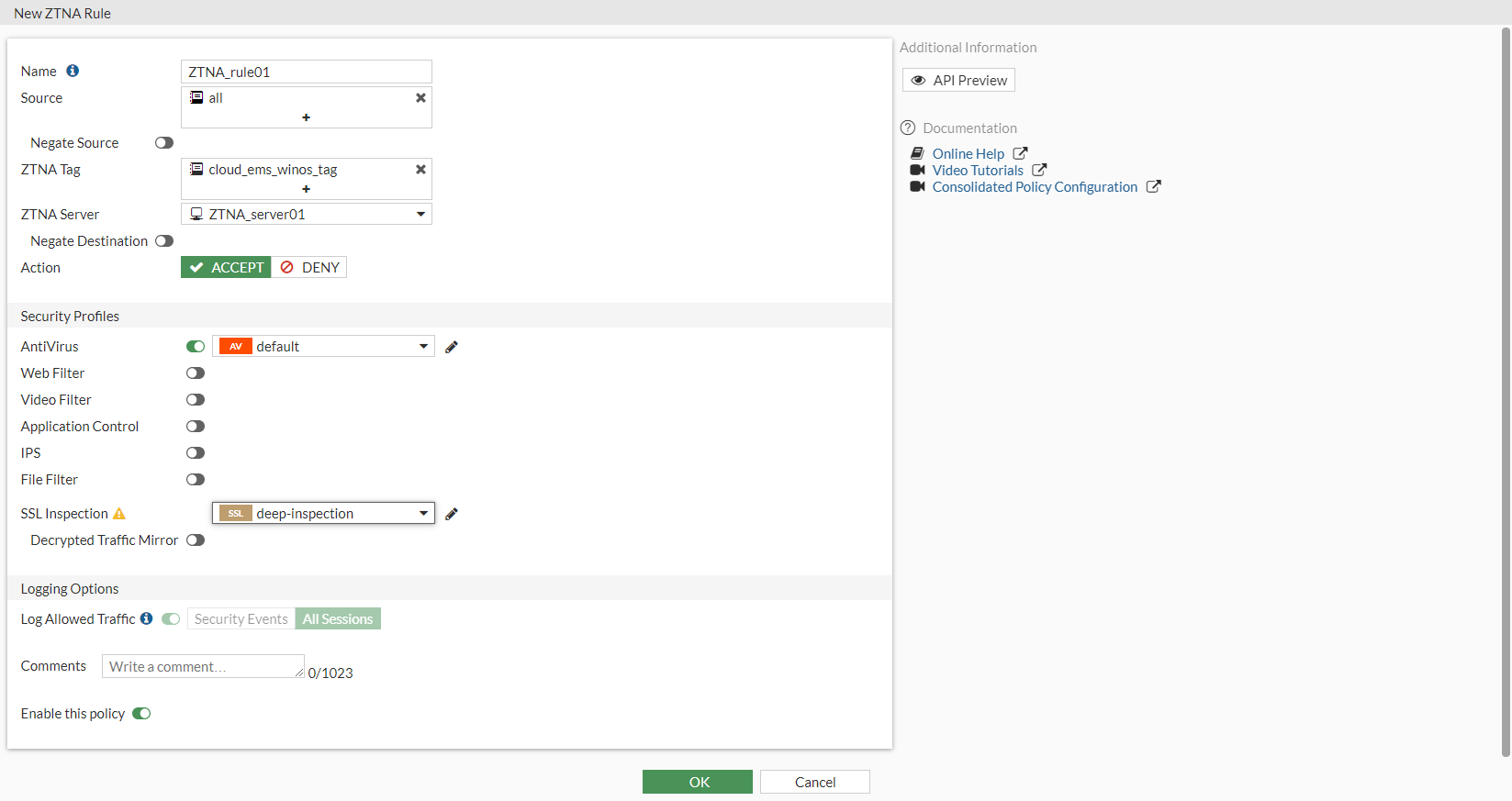
-
Configure the remaining options as needed.
-
Click OK.
To configure a ZTNA rule in the CLI:
config firewall proxy-policy
edit 1
set name <ZTNA rule name>
set proxy access-proxy
set access-proxy <access proxy>
set srcaddr "all"
set dstaddr "all"
set ztna-ems-tag <ZTNA tag(s)>
set action accept
set schedule "always"
set logtraffic all
set utm-status enable
set ssl-ssh-profile <inspection profile>
next
end
Configure a firewall policy for full ZTNA
The firewall policy matches and redirects client requests to the access proxy VIP. The source interface and addresses that are allowed access to the VIP can be defined. By default, the destination is any interface, so once a policy is configured for full ZTNA, the policy list will be organized by sequence.
UTM processing of the traffic happens at the ZTNA rule.
To configure a firewall policy for full ZTNA in the GUI:
-
Go to Policy & Objects > Firewall Policy and click Create New.
-
Enter a name for the policy.
-
Enable ZTNA and select Full ZTNA.
-
Set ZTNA Server to the configured ZTNA server.
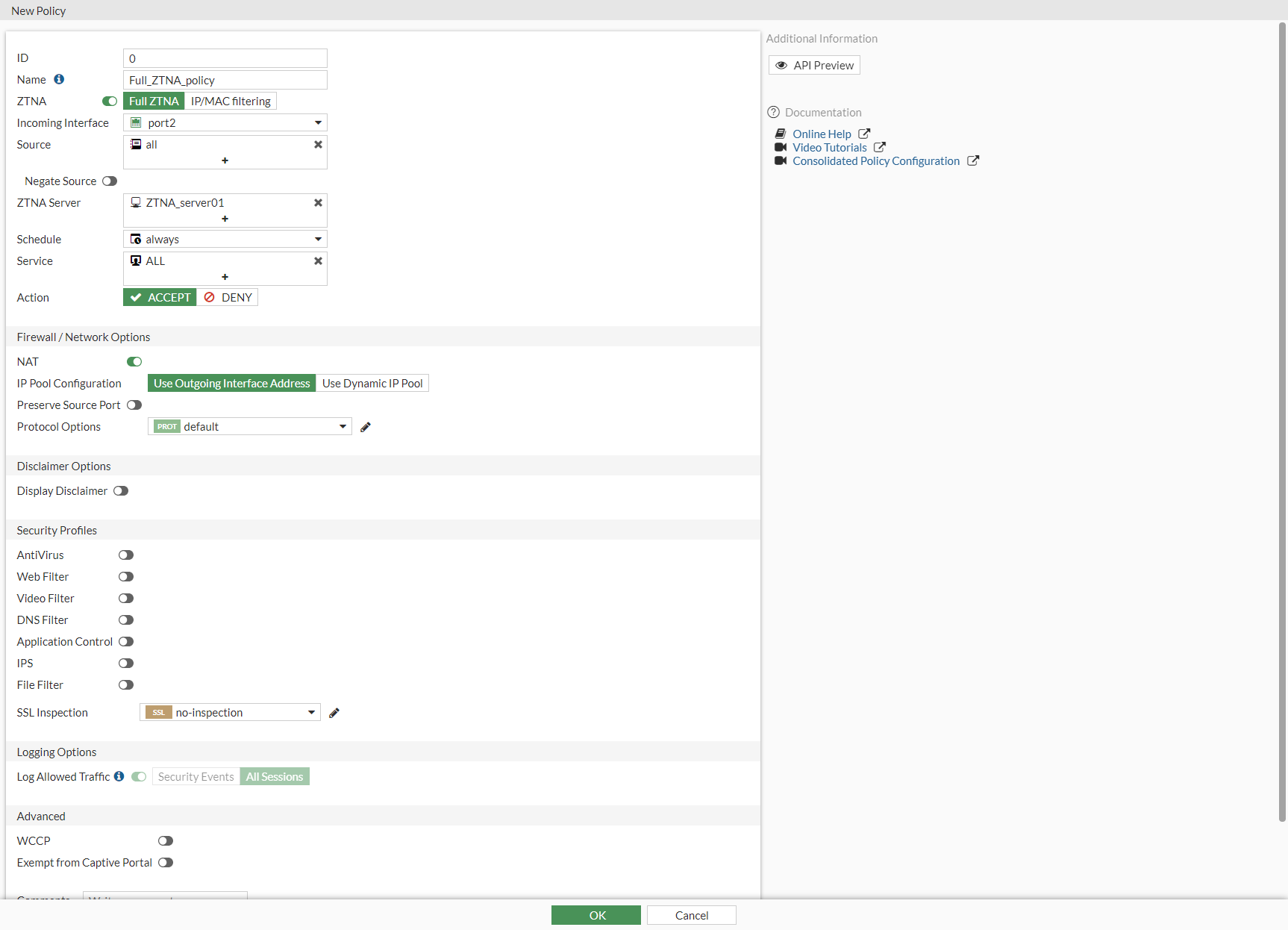
-
Configure the remaining settings as needed.
-
Click OK.
To configure a firewall policy for full ZTNA in the CLI:
config firewall policy
edit <policy ID>
set name <policy name>
set srcintf <source interface>
set dstintf "any"
set srcaddr <source address>
set dstaddr <access proxy VIP>
set action accept
set schedule "always"
set service "ALL"
set inspection-mode proxy
set logtraffic all
set nat enable
next
end
Optional authentication
To configure authentication to the access proxy, you must configure an authentication scheme and authentication rule in the CLI. They are used to authenticate proxy-based policies, similar to configuring authentication for explicit and transparent proxy.
The authentication scheme defines the method of authentication that is applied. For ZTNA, basic HTTP and SAML methods are supported. Each method has additional settings to define the data source to check against. For example, with basic HTTP authentication, a user database can reference an LDAP server, RADIUS server, local database, or other supported authentication servers that the user is authenticated against.
The authentication rule defines the proxy sources and destinations that require authentication, and which authentication scheme to apply. For ZTNA, active authentication method is supported. The active authentication method references a scheme where users are actively prompted for authentication, like with basic authentication.
After the authentication rule triggers the method to authenticate the user, a successful authentication returns the groups that the user belongs to. In the ZTNA rule and proxy policy you can define a user or user group as the allowed source. Only users that match that user or group are allowed through the proxy policy.
To configure a basic authentication scheme:
config authentication scheme
edit <name>
set method basic
set user-database <auth server>
next
end
To configure an authentication rule:
config authentication rule
edit <name>
set status enable
set protocol http
set srcintf <interface>
set srcaddr <address>
set dstaddr <address>
set ip-based enable
set active-auth-method <active auth scheme>
next
end
To apply a user group to a ZTNA rule in the GUI:
-
Go to Policy & Objects > ZTNA and select the ZTNA Rules tab.
-
Edit an existing rule, or click Create New to create a new rule.
-
Click in the Source field, select the User tab, and select the users and user groups that will be allowed access.
-
Configure the remaining settings as required.
-
Click OK.
To apply a user group to a ZTNA rule in the CLI:
config firewall proxy-policy
edit <policy ID>
set name <ZTNA rule name>
set proxy access-proxy
set access-proxy <access proxy>
set srcaddr "all"
set dstaddr "all"
set ztna-ems-tag <ZTNA tags>
set action accept
set schedule "always"
set logtraffic all
set groups <user group>
set utm-status enable
set ssl-ssh-profile <inspection profile>
next
end
The authentication rule and scheme defines the method used to authenticate users. With basic HTTP authentication, a sign in prompt is shown after the client certificate prompt. After the authentication passes, the returned groups that the user is a member of are checked against the user groups that are defined in the ZTNA rule. If a group matches, then the user is allowed access after passing a posture check.
For more information, see ZTNA HTTPS access proxy with basic authentication example and ZTNA proxy access with SAML authentication example .

