Basic category filters and overrides
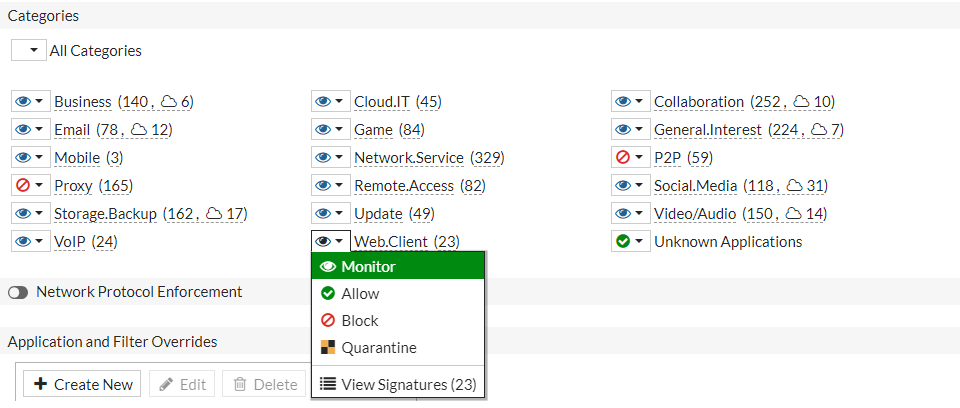
Once you have created an application sensor, you can define the applications that you want to control. You can add applications and filters using categories, application overrides, and/or filter overrides with designated actions (monitor, allow, block, or quarantine).
|
Action |
Description |
|---|---|
| Monitor | Passes the traffic and generates a log message. |
| Allow | Passes the traffic but does not generate a log message. |
| Block | Drops the detected traffic and generates a log message. |
| Quarantine | Blocks the traffic from an attacker IP address until the expiration time is reached and generates a log message. |
For more information about application control logs, see Log and Report.
To configure category filters in the GUI:
- Go to Security Profiles > Application Control and click Create New, or edit an existing sensor.
- Under Categories, click the icon next to the category name to set the action or view the application signatures.
-
If you select the Quarantine action, the Quarantine Duration pane will open. Enter the duration values and click OK.

- Click OK.
To configure category filters in the CLI:
config application list
edit <name>
config entries
edit <id>
set category <id>
set action {pass | block | reset}
set quarantine {none | attacker}
set quarantine-expiry <###d##h##m>
set log {enable | disable}
next
end
next
end
Configuring application and filter overrides
Multiple application signatures can be added for one sensor with a designated action. Filters can be added based on behavior, application category, popularity, protocol, risk, technology, or vendor subtypes.
To configure overrides in the GUI:
-
Go to Security Profiles > Application Control and click Create New, or edit an existing sensor.
-
In the Application and Filter Overrides table, click Create New.
-
Add an application:
-
For Type, select Application.
-
Select an Action from the dropdown.
-
In the Search box, enter an application name and press
Enter. -
In the search results, select desired the applications (you can select multiple applications) and click Add Selected.

-
Click OK.
-
-
Add a filter:
-
In the Application and Filter Overrides table, click Create New.
-
For Type, select Filter.
-
Select an Action from the dropdown.
-
In the Filter field, click the + . The Select Entries pane opens, and you can search based on filter subtypes. This example has excessive bandwidth (under behavior) and game (under application category).

-
Click OK.
-
-
Click OK.
To configure overrides in the CLI:
config application list
edit <name>
config entries
edit <id>
set protocols <integer>
set risk <integer>
set vendor <id>
set technology <id>
set behavior <id>
set popularity <integer>
set action {pass | block | reset}
set log {enable | disable}
next
end
next
end
|
|
Application protocol filter (0 - 47, or all). |
|
|
Risk or impact of allowing traffic from this application to occur (1 - 5; low (1), elevated (2), medium (3), high (4), and critical (5)). |
|
|
Application vendor filter (0 - 25, or all). |
|
|
Application technology filter:
|
|
|
Application behavior filter:
|
|
|
Application popularity filter (1 - 5, from least to most popular). |
|
|
Pass/block traffic or reset the connection for traffic from this application (default = block). |
|
|
Enable/disable logging for this application list (default = enable). |

