Synchronizing LDAP Active Directory users to FortiToken Cloud using the group filter
To synchronize Active Directory users and apply two-factor authentication using FortiToken Cloud, two-factor authentication can be enabled in the user ldap object definition in FortiOS. By default, FortiOS retrieves all Active Directory users in the LDAP server with a valid email or mobile number (mail and mobile attributes), and synchronizes the users to FortiToken Cloud. Users are then created on FortiToken Cloud and activation is sent out using email or SMS.
Group filters can be used to reduce the number of the Active Directory users returned, and only synchronize the users who meet the group filter criteria.
Two-factor authentication for LDAP group filtering can only be configured in the CLI:
config user ldap
edit <name>
set dn <string>
set two-factor {disable | fortitoken-cloud}
set group-filter <string>
next
end
|
dn <string> |
Set the distinguished name used to look up entries on the LDAP server. The search for users and groups starts here based on what is defined. |
|
two-factor {disable | fortitoken-cloud} |
Enable/disable two-factor authentication:
|
|
group-filter <string> |
Set the filter used for group matching. |
Group filter examples
In the following examples, a user ldap object is defined to connect to an Active Directory on a Windows server. The search will begin in the root of the fortinet-fsso.com directory.
To configure a default LDAP server configuration without a group filter:
config user ldap
edit "ad-ldap-auth"
set server <ip_address>
set cnid "cn"
set dn "dc=fortinet-fsso,dc=com"
set type regular
set two-factor fortitoken-cloud
set username "cn=Administrator,cn=users,dc=fortinet-fsso,dc=com"
set password **********
next
end
When a group filter is not used, all users in the Active Directory with a valid email or mobile number will be retrieved.
Example 1: specific users and email address with wildcard
With this group-filter, users under fortinet-fsso.com that have oliver* in their username and *fortinet* in their email will be matched.
config user ldap
edit "ad-ldap-auth"
set group-filter "(&(SAMAccountName=oliver*)(mail=*fortinet*))"
next
end
Example 2: all users with matching email
With this group-filter, all users under fortinet-fsso.com with *fortinet* in their email will be matched.
config user ldap
edit "ad-ldap-auth"
set group-filter "(&(SAMAccountName=*)(mail=*fortinet*))"
next
end
Example 3: all users in a group
With this group-filter, all users within the group fortinet-fsso.com > Testing > ftc-users will be matched.
config user ldap
edit "ad-ldap-auth"
set group-filter "(&(objectCategory=Person)(sAMAccountName=*)( memberOf=cn=ftc-users,ou=Testing,dc=fortinet-fsso,DC=com))"
next
end
Example configuration
In this example, Active Directory users are configured to be synchronized to FortiToken Cloud. The same group filter is used from example 1 and searches the Active Directory for users named oliver* with email *fortinet*.
Before configuring the FortiGate:
-
Gather the information to connect to the Active Directory server through LDAP. Include all necessary fields, such as the server IP, port, CN name identifier, DN for the start of the search, bind type, and username associated with a regular bind.
-
Consider the users or groups that require two-factor authentication and should be synchronized. If necessary, group the users under the same group in the Active Directory.
-
If using a group filter, formulate the
group-filterstring to limit the match. For this example,(&(SAMAccountName=oliver*)(mail=*fortinet*)). -
Test the filter by using the FortiOS CLI to perform a quick LDAP search:
# diagnose test authserver ldap-search <server_ip> 389 "ou=Testing,dc=fortinet-fsso,DC=com" cn Administrator@fortinet-fsso.com PASSWORD 0 '(&(SAMAccountName=oliver*)(mail=*fortinet*))' 2 searching 'ou=Testing,dc=fortinet-fsso,DC=com, cn=cn' on 10.1.100.131:389 for (Administrator@fortinet-fsso.com, PASSWORD), secure(0), filter((&(SAMAccountName=oliver*)(mail=*fortinet*))), flag(0x2), page_no(0)... CN=oliver2022,OU=Testing,DC=Fortinet-FSSO,DC=COM (oliver2022, 0 entries)
The user,
oliver2022, was found. -
Estimate how many users will be retrieved, and ensure that the FortiToken Cloud account has enough user licenses to support the number of users.
To configure Active Directory users to be synchronized to FortiToken Cloud:
-
Configure the user LDAP settings:
config user ldap edit "ad-ldap-auth" set server "10.1.100.131" set cnid "cn" set dn "dc=fortinet-fsso,dc=com" set type regular set two-factor fortitoken-cloud set username "cn=Administrator,cn=users,dc=fortinet-fsso,dc=com" set password ********** set group-filter "(&(SAMAccountName=oliver*)(mail=*fortinet*))" next end -
In the background, the FortiGate FAS daemon scans the LDAP server for users to be synchronized based on the group filter pattern, but will not send them to the FortiToken Cloud server yet. Optionally, verify the users that are retrieved from the Active Directory based on the filter:
# diagnose fortitoken-cloud debug enable # diagnose debug enable # diagnose fortitoken-cloud sync ... fas_sync_ftc[2788]: Sending packet to FTC server: "IP-of-FTC-server" Port: 8686(length:444) fas_sync_ftc[2792]: FTC User Sync Packet(length:444): POST /api/v1/user_sync HTTP/1.1 Host: ftc.fortinet.com Connection: keep-alive User-Agent: FortiGate-401E v7.0.6,build**** Content-Type: application/json Content-Length: 246 {"users":[{"username":"oliver2022","vdom":"vdom1","email":"o****@fortinet.com","mobile_number":"XXXXXXXXXXX","user_data":1,"action":"create"}],"sn":"FG4H1E5819900000","cluster_members":[ "FG4H1E5819900000" ],"group_name":"FGT400D","group_id":"0"} Reminder: User sync packet not actually sent out because of diagnose purpose!As expected, only the user that matches the current filter is returned.
-
Manually trigger the synchronization process with FortiToken Cloud:
# execute fortitoken-cloud sync
The user is added to FortiToken Cloud, and an activation email or SMS message is sent to the user.
-
In FortiToken Cloud, go to Users to verify that the user was added.
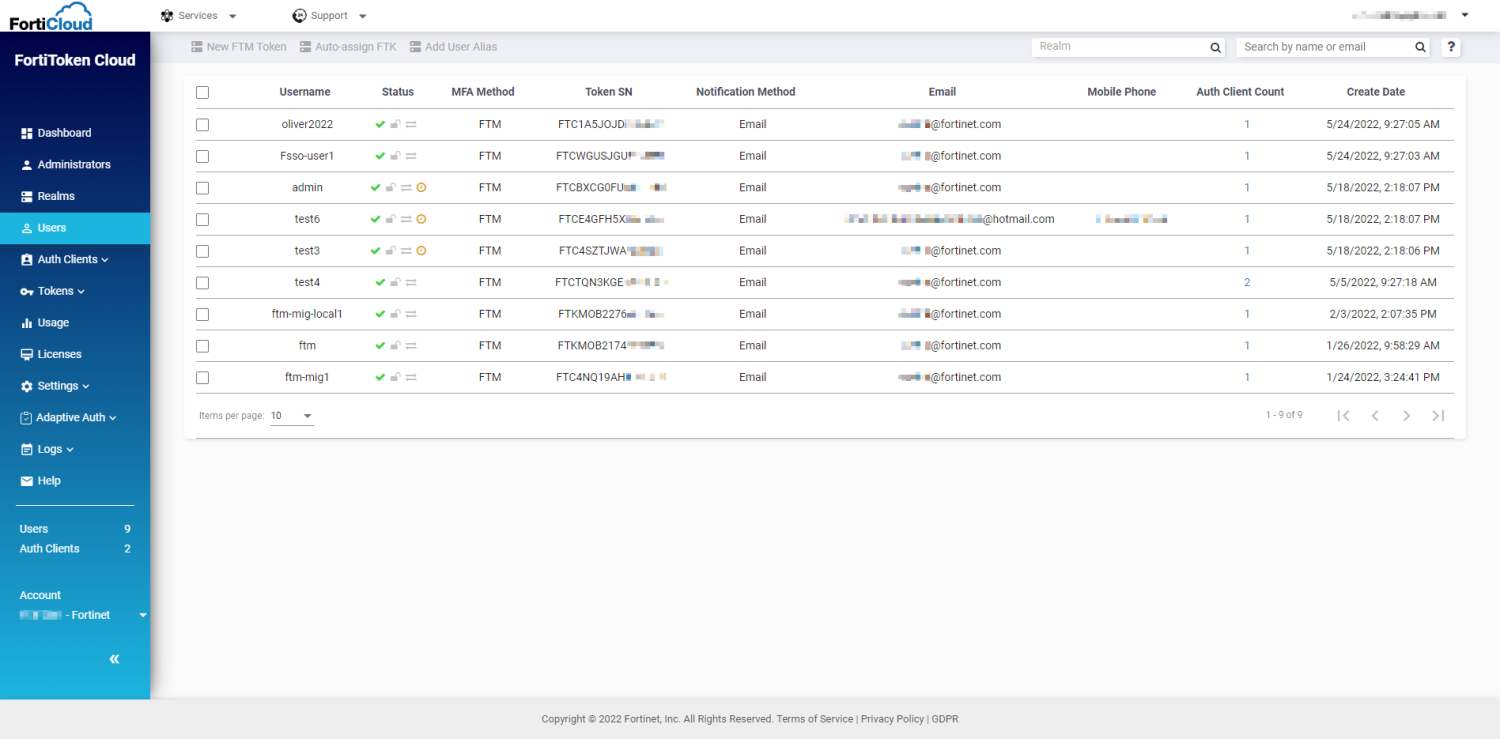
If the activation email was sent, but user has not downloaded and activated the mobile token yet, a pending symbol appears in the Status column (such as for the admin, test6, and test3 users).
-
In FortiOS, add the
ad-ldap-authobject in a user group. The user group can be used for VPN, firewall authentication, and so on.
The
ldap userobject should not be used in remote LDAP user groups that require group matching because it is not supported.

