IPv6 quick start
This section provides an introduction to setting up a few basic IPv6 settings on the FortiGate. See Basic administration for more information about basic FortiGate administration.
|
|
This chapter provides instructions for basic IPv6 configuration that should work in most cases, regardless of whether the device has an existing IPv4 configuration or is a new FortiGate device. |
The topics covered in this section include:
Before starting, make sure to enable the IPv6 feature.
To enable IPv6 in the GUI:
-
Go to System > Feature Visibility.
-
Under Core Features, enable IPv6.
-
Click Apply.
Configuring an interface
To configure an interface in the GUI:
-
Go to Network > Interfaces.
-
Select an interface and click Edit.
-
In the Address section, enter the IPv6 Address/Prefix.
-
In the Administrative Access section, select the IPv6 access options as needed (such as PING, HTTPS, and SSH).
-
Click OK.
To configure an interface in the CLI:
config system interface
edit <interface name>
config ipv6
set ip6-address <IPv6 prefix>
set ip6-allowaccess{ping | https | ssh | snmp | http | telnet | fgfm | fabric}
end
next
end
Configuring the default route
Setting the default route enables basic routing to allow the FortiGate to return traffic to sources that are not directly connected. The gateway address should be your existing router or L3 switch that the FortiGate is connected to. Set the interface to be the interface the gateway is connected to.
To configure the default route in the GUI:
-
Go to Network > Static Routes.
-
Click Create New > IPv6 Static Route.
-
Leave the Destination prefix as ::/0. This is known as a default route, since it would match any IPv6 address.
-
Enter the Gateway Address.
-
Select an Interface.
-
Click OK.
To configure the default route in the CLI:
config router static6
edit 0
set gateway <IPv6 address>
set device <interface name>
next
end
Configuring the DNS
To configure a DNS domain list in the GUI:
-
Go to Network > DNS.
-
Under IPv6 DNS Settings, configure the primary and secondary DNS servers as needed.
-
Click Apply.
To configure a DNS domain list in the CLI:
config system dns
set ip6-primary <IPv6 address>
set ip6-secondary <IPv6 address>
end
Configuring the address object
Addresses define sources and destinations of network traffic and can be used in many functions such as firewall policies, ZTNA, and so on. When creating an IPv6 address object, several different types of addresses can be specified similar to IPv4 addresses. See Address Types for more information.
To configure an IPv6 address in the GUI:
-
Go to Policy & Objects > Addresses.
-
Select Create New > Address.
-
In the Category field, select IPv6 Address.
-
Enter a Name for the address object.
-
In the Type field, select one of the types from the dropdown menu.
-
Configure the rest of the settings as required.
-
Click OK.
To configure an IPv6 address in the CLI:
config firewall address6
edit <name>
set type {ipprefix | iprange | fqdn | geography | dynamic | template | mac}
next
end
Configuring the address group
Address groups are designed for ease of use in the administration of the device. See Address group for more information.
To create an address group:
-
Go to Policy & Objects > Addresses.
-
Go to Create New > Address Group.
-
In the Category field, select IPv6 Group.
-
Enter a Group name for the address object.
-
Select the + in the Members field. The Select Entries pane opens.
-
Select members of the group. It is possible to select more than one entry. Select the x icon in the field to remove an entry.
-
Enter any additional information in the Comments field.
-
Click OK.
To configure an address group in the CLI:
config firewall addrgrp6
edit <name>
set member <name>
next
end
Configuration example
In this example, a host belonging to a specific range on the internal IPv6 network can communicate exclusively with the web server and FTP server.
Additionally, all internal clients can access the Internet.
Prerequisites
Before you begin to configure IPv6, go through the following steps:
-
Obtain an IPv6 /48 global routing prefix, commonly known as a site prefix. To procure a 48-bit IPv6 site prefix for your organization simply liaise with your ISP.
-
Design a subnetting plan for your organization's IPv6 network using a 16-bit subnet ID, allowing for up to 65 535 subnets. The specific scheme will depend on the network's size, structure, and the organization's needs.
At this stage, the following installation and configuration conditions are assumed:
-
You have administrative access to the GUI or CLI.
-
The FortiGate unit is incorporated into your WAN or other networks, but for simplicity, only the standalone ForiGate configuration is displayed.
Topology
The following topology is used for this example:
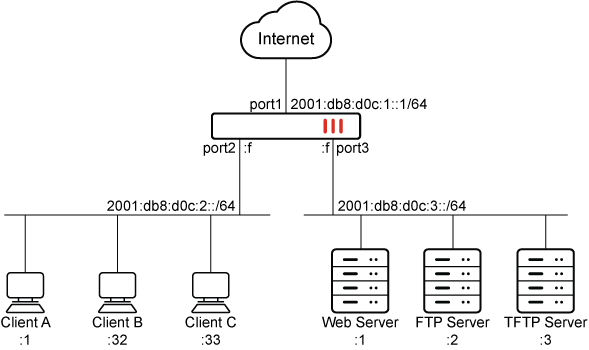
-
The company is assigned the site prefix of 2001:db8:d0c::/48 by their ISP.
-
The IPv6 address for the Web Server is 2001:db8:d0c:3::1/64.
-
The IPv6 address for the FTP Server is 2001:db8:d0c:3::2/64.
-
The IPv6 address for the TFTP Server is 2001:db8:d0c:3::3/64.
-
The range on the internal IPv6 network that can access both servers is from 2001:db8:d0c:2::1 to 2001:db8:d0c:2::32.
-
The IPv6 address of port1 is 2001:db8:d0c:1::1/64.
-
The IPv6 address of port2 is 2001:db8:d0c:2::f/64.
-
The IPv6 address of port3 is 2001:db8:d0c:3::f/64.
-
The IPv6 address of the default gateway is 2001:db8:d0c:1::f/64.
|
|
Please note that the IPv6 addresses used in this example are for illustrative purposes only and should not be used in your environment. The 2001:db8::/32 prefix is a special IPv6 prefix designated for use in documentation examples. See RFC 3849 for more information. |
To configure the example in the GUI:
-
Configure the IPv6 address on port1, port2 and port3:
-
Go to Network > Interfaces and edit port1.
-
For IPv6 addressing Mode, select manual and enter the IPv6 Address/Prefix.
IPv6 Address/Prefix 2001:db8:d0c:1::1/64 -
Click OK.
-
Repeat steps a and b for port2.
IPv6 Address/Prefix 2001:db8:d0c:2::f/64 -
Repeat steps a and b for port3.
IPv6 Address/Prefix 2001:db8:d0c:3::f/64
-
-
Configure the default route:
-
Go to Network > Static Routes.
-
Click Create New > IPv6 Static Route.
-
Configure the following settings:
Destination ::/0 Gateway Address 2001:db8:d0c:1::f Interface port1 -
Select OK.
-
-
Configure the IPv6 firewall address for the Web Server:
-
Go to Policy & Objects > Addresses.
-
Select Create New > Address.
-
Select IPv6 Address and fill out the fields with the following information:
Name Web_Server Type IPv6 Subnet IPv6 Address 2001:db8:d0c:3::1/128 -
Select OK.
-
-
Configure the IPv6 firewall address for the FTP Server:
-
Go to Policy & Objects > Addresses.
-
Select Create New > Address.
-
Select IPv6 Address and fill out the fields with the following information:
Name FTP_Server Type IPv6 Subnet IPv6 Address 2001:db8:d0c:3::2/128 -
Select OK.
-
-
Configure the IPv6 address group, which includes both the Web and FTP servers:
-
Go to Policy & Objects > Addresses.
-
Select Create New > Address Group.
-
Select IPv6 Group and fill out the fields with the following information:
Group name Custom_Server Members Web_Server, FTP_Server -
Select OK.
-
-
Configure the IPv6 firewall address for the Internal IPv6 network range which can access both the Web and FTP server:
-
Go to Policy & Objects > Addresses.
-
Select Create New > Address.
-
Select IPv6 Address and fill out the fields with the following information:
Name Internal_Custom_Range Type IPv6 Range IP Range 2001:db8:d0c:2::1 - 2001:db8:d0c:2::32 -
Select OK.
-
-
Configure the IPv6 firewall policy to allow IPv6 traffic from Internal_Custom_Range to Custom_Server:
-
Go to Policy & Objects > Firewall Policy.
-
Click Create New.
-
Name the policy and configure the following parameters:
Incoming Interface port2 Outgoing Interface port3 Source Internal_Custom_Range Destination Custom_Server Schedule always Service FTP, HTTPS Action ACCEPT -
Click OK.
-
-
Configure the IPv6 firewall policy to allow IPv6 traffic from internal clients to the Internet:
-
Go to Policy & Objects > Firewall Policy.
-
Click Create New.
-
Name the policy and configure the following parameters:
Incoming Interface port2 Outgoing Interface port1 Source all Destination all Schedule always Service ALL Action ACCEPT -
Click OK.
-
To configure the example in the CLI:
-
Configure the IPv6 address on port1, port2, and port3:
config system interface edit "port1" config ipv6 set ip6-address 2001:db8:d0c:1::1/64 end next edit "port2" config ipv6 set ip6-address 2001:db8:d0c:2::f/64 end next edit "port3" config ipv6 set ip6-address 2001:db8:d0c:3::f/64 end next end -
Configure the default route:
config router static6 edit 0 set gateway 2001:db8:d0c:1::f set device "port1" next end -
Configure the IPv6 firewall address for the Web Server:
config firewall address6 edit "Web_Server" set ip6 2001:db8:d0c:3::1/128 next end -
Configure the IPv6 firewall address for the FTP Server:
config firewall address6 edit "FTP_Server" set ip6 2001:db8:d0c:3::2/128 next end -
Configure the IPv6 address group, which includes for the Web and FTP Servers:
config firewall addrgrp6 edit "Custom_Server" set member "FTP_Server" "Web_Server" next end -
Configure the IPv6 firewall address for the Internal IPv6 network range which can access both the Web and FTP Server:
config firewall address6 edit "Internal_Custom_Range" set type iprange set start-ip 2001:db8:d0c:2::1 set end-ip 2001:db8:d0c:2::32 next end -
Configure the IPv6 firewall policy to allow IPv6 traffic from Internal_Custom_Range to Custom_Server:
config firewall policy edit 1 set name "IPv6_internal_to_server" set srcintf "port2" set dstintf "port3" set action accept set srcaddr6 "Internal_Custom_Range" set dstaddr6 "Custom_Server" set schedule "always" set service "FTP" "HTTPS" set utm-status enable set logtraffic all next end -
Configure the IPv6 firewall policy to allow IPv6 traffic from Internal clients to the Internet:
config firewall policy edit 1 set name "IPv6_internal_to_internet" set srcintf "port2" set dstintf "port1" set action accept set srcaddr6 "all" set dstaddr6 "all" set schedule "always" set service "ALL" set utm-status enable set logtraffic all next end
Verification
The following commands can be used to verify that IPv6 traffic is entering and leaving the FortiGate as expected. See Debugging the packet flow for more information.
diagnose debug enable diagnose debug flow trace start6 200
The output below indicates that hosts belonging to the Internal_Custom_Range can successfully reach both the Web_Server and FTP_Server defined in the Custom_Server address group.
However, they are unable to reach the TFTP server, as it is not included in the Custom_Server group. Furthermore, hosts with IPv6 addresses that do not belong to the Internal_Custom_Range are not able to access Custom_Server.
Host belonging to Internal_Custom_Range accessing Web_Server:
id=65308 trace_id=21 func=resolve_ip6_tuple_fast line=4962 msg="vd-root:0 received a packet(proto=6, 2001:db8:d0c:2::1:55114->2001:db8:d0c:3::1:443) from port2." id=65308 trace_id=21 func=resolve_ip6_tuple line=5102 msg="allocate a new session-0000006b" id=65308 trace_id=21 func=ip6_route_input line=2186 msg="find a route: gw-:: via port3 err 0 flags 40000001" id=65308 trace_id=21 func=fw6_forward_handler line=501 msg="Check policy between port2 -> port3" id=65308 trace_id=21 func=fw6_forward_handler line=638 msg="Allowed by Policy-1:"
Host belonging to Internal_Custom_Range accessing FTP_Server:
id=65308 trace_id=6 func=resolve_ip6_tuple_fast line=4962 msg="vd-root:0 received a packet(proto=6, 2001:db8:d0c:2::32:50982->2001:db8:d0c:3::2:21) from port2." id=65308 trace_id=6 func=resolve_ip6_tuple line=5102 msg="allocate a new session-00000053" id=65308 trace_id=6 func=ip6_route_input line=2186 msg="find a route: gw-:: via port3 err 0 flags 40000001" id=65308 trace_id=6 func=fw6_forward_handler line=501 msg="Check policy between port2 -> port3" id=65308 trace_id=6 func=fw6_forward_handler line=638 msg="Allowed by Policy-1:"
Host belonging to Internal_Custom_Range accessing TFTP Server:
id=65308 trace_id=17 func=resolve_ip6_tuple_fast line=4962 msg="vd-root:0 received a packet(proto=17, 2001:db8:d0c:2::32:65316->2001:db8:d0c:3::3:69) from port2." id=65308 trace_id=17 func=resolve_ip6_tuple line=5102 msg="allocate a new session-00000055" id=65308 trace_id=17 func=ip6_route_input line=2186 msg="find a route: gw-:: via port3 err 0 flags 40000001" id=65308 trace_id=17 func=fw6_forward_handler line=501 msg="Check policy between port2 -> port3" id=65308 trace_id=17 func=fw6_forward_handler line=530 msg="Denied by forward policy check"
Host not belonging to Internal_Custom_Range accessing FTP_Server:
id=65308 trace_id=1 func=resolve_ip6_tuple_fast line=4962 msg="vd-root:0 received a packet(proto=6, 2001:db8:d0c:2::33:52555->2001:db8:d0c:3::2:21) from port2." id=65308 trace_id=1 func=resolve_ip6_tuple line=5102 msg="allocate a new session-0000004d" id=65308 trace_id=1 func=ip6_route_input line=2186 msg="find a route: gw-:: via port3 err 0 flags 40000001" id=65308 trace_id=1 func=fw6_forward_handler line=501 msg="Check policy between port2 -> port3" id=65308 trace_id=1 func=fw6_forward_handler line=530 msg="Denied by forward policy check"
Internal clients accessing the Internet:
The output below indicates that internal clients can successfully reach the internet.
-
Go to Log & Report > Forward Traffic.
-
View the log details in the GUI, or download the log file:
1: date=2023-05-10 time=13:22:54 eventtime=1683750174692262952 tz="-0700" logid="0000000013" type="traffic" subtype="forward" level="notice" vd="root" srcip=2001:db8:d0c:2::1 srcport=64780 srcintf="port2" srcintfrole="undefined" dstip=64:ff9b::83fd:21c8 dstport=443 dstintf="port1" dstintfrole="undefined" sessionid=15723 proto=6 action="close" policyid=2 policytype="policy" poluuid="ea8a972e-d7e9-51ed-9b29-757f04e7194c" policyname="IPv6_internal_to_internet" srccountry="Reserved" service="HTTPS" trandisp="noop" duration=3 sentbyte=47192 rcvdbyte=13199 sentpkt=49 rcvdpkt=48 appcat="unscanned" 2: date=2023-05-10 time=13:19:47 eventtime=1683749987902192921 tz="-0700" logid="0000000013" type="traffic" subtype="forward" level="notice" vd="root" srcip=2001:db8:d0c:2::33 srcport=51246 srcintf="port2" srcintfrole="undefined" dstip=64:ff9b::349f:31c7 dstport=443 dstintf="port1" dstintfrole="undefined" sessionid=15126 proto=6 action="close" policyid=2 policytype="policy" poluuid="ea8a972e-d7e9-51ed-9b29-757f04e7194c" policyname="IPv6_internal_to_internet" srccountry="Reserved" service="HTTPS" trandisp="noop" duration=59 sentbyte=5109 rcvdbyte=7726 sentpkt=13 rcvdpkt=11 appcat="unscanned"

