DLP fingerprinting
DLP fingerprinting employs Indexed Document Matching (IDM) to detect sensitive data. See Indexed Document Matching (IDM) for more information. The file that the DLP profile filters is uploaded and the FortiGate generates and stores a checksum fingerprint. The FortiGate generates a fingerprint for all the files that are detected in network traffic, and compares all the checksums stored in its database. If a match is found, the configured action is taken. Any type of file can be detected by DLP fingerprinting, and fingerprints can be saved for each revision of a file as it is updated.
Using fingerprinting requires:
-
Adding the profiles to firewall policies that accept traffic that the fingerprinting will be applied on.
See Fingerprinting example for a sample configuration.
|
|
The document fingerprint feature requires a FortiGate that has internal storage. |
To configure a DLP fingerprint document:
config dlp fp-doc-source
edit <name>
set server <string>
set username <string>
set password <password>
set file-path <string>
set sensitivity <Critical | Private | Warning>
next
end
|
Command |
Description |
|---|---|
|
server <string> |
Enter the IPv4 or IPv6 address of the file server. |
|
username <string> |
Enter the user name required to log into the file server. |
|
password <password> |
Enter the password required to log into the file server. |
|
file-path <string> |
Enter the path on the server to the fingerprint files. |
|
sensitivity <Critical | Private | Warning> |
Set the sensitivity or threat level for matches with this fingerprint database. |
See config dlp fp-doc-source in the FortiOS CLI Reference for a comprehensive list of commands and supported FortiGate models.
|
|
A file server is required for the user to upload files. Each uploaded file will have a fingerprint generated by FortiGate, and will be stored locally as a checksum. Currently, only servers that are using the Samba (SMB) protocol are compatible. |
To configure a DLP fingerprint profile:
config dlp profile
edit <name>
set feature-set proxy
config rule
edit <id>
set proto {smtp | pop3 | imap | http-get | http-post | ftp | nntp | mapi | ssh | cifs}
set filter-by fingerprint
set sensitivity {Critical | Private | Warning}
set match-percentage <integer>
set action {allow | log-only | block | quarantine-ip}
next
end
next
end
|
Command |
Description |
|---|---|
|
proto {smtp | pop3 | imap | http-get | http-post | ftp | nntp | mapi | ssh | cifs} |
Set the protocol to inspect. |
|
filter-by fingerprint |
Set to match against a fingerprint sensitivity. |
|
sensitivity {Critical | Private | Warning} |
Set the DLP file pattern sensitivity to match. |
|
match-percentage <integer> |
Set the percentage of the checksum required to match before the profile is triggered. |
|
action {allow | log-only | block | ban | quarantine‑ip} |
Set the action to take with content that matches the DLP profile. |
Fingerprinting example
This configuration will block HTTPS download traffic that matches the checksums that are stored in the FortiGate fingerprint database.
|
|
When utilizing commonly-used SSL-encrypted protocols, such as HTTPS, SMTPS, POP3S, IMAPS, and FTPS, SSL inspection must be set to Deep Inspection. See Deep inspection for more information. The client machine must also have the corresponding deep inspection Certificate Authority (CA) certificate installed. |
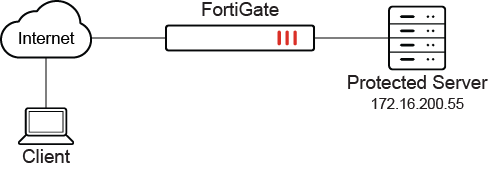
In this example, a text document with sensitive data is being downloaded by the client using the HTTP GET method. The term Protected Server refers to the Samba file server that stores the fingerprint files. It is assumed that you already have a configured Samba file server.
The FortiGate intercepts the traffic using deep inspection and blocks the traffic as it matches the DLP profile configured on this FortiGate. See Sample log for a log sample.
To block network traffic that matches the checksums stored in the FortiGate fingerprint database:
-
Configure the DLP fingerprint database:
config dlp fp-doc-source edit "test" set server "172.16.200.55" set username "kiki" set password ***** set file-path "/sambashare/upload/" set sensitivity "Critical" next endThis step can only be configured in the CLI.
-
Configure the DLP profile:
config dlp profile edit "fingerprint" set feature-set proxy config rule edit 1 set proto http-get set filter-by fingerprint set sensitivity "Critical" set action block next end next endDLP profiles that filter by fingerprint can only be configured in the CLI.
-
Add the DLP profile to a firewall policy:
config firewall policy edit 1 set srcintf "port2" set dstintf "port1" set action accept set srcaddr "all" set dstaddr "all" set schedule "always" set service "ALL" set utm-status enable set inspection-mode proxy set ssl-ssh-profile "deep-inspection" set dlp-profile "fingerprint" set nat enable next endThis can also be configured in the GUI. See To add the DLP profile to a firewall policy.
To verify the results:
-
Verify that the DLP fingerprint database is present on the FortiGate:
# diagnose test application dlpfingerprint 3 File DB: --------------------------------------- id, filename, vdom, archive, deleted, scanTime, docSourceSrvr, sensitivity, chunkCnt, reviseCnt, 1, /sambashare/upload/testdlp, root, 0, 0, 1706727347, test, 2, 1, 0, 2, /sambashare/upload/testdlp.txt, root, 0, 0, 1706728230, test, 2, 1, 0,
-
Verify HTTP GET traffic that matches the checksums stored in the FortiGate fingerprint database is being blocked:
A download attempt of a text file from a Windows device was made using Chrome browser. This text file is located on the protected server and its fingerprint is saved in the FortiGate fingerprint database.
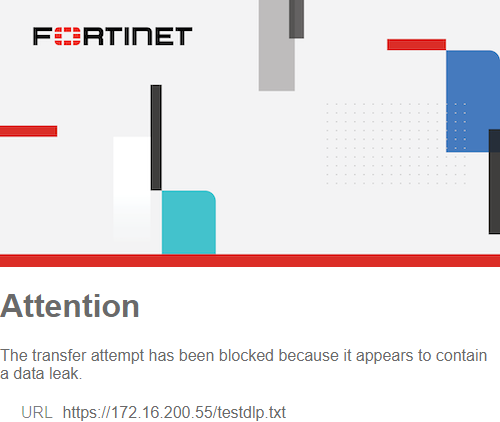
The download was unsuccessful, leading to the creation of a sample log. See Sample log.
Sample log
To view the sample log:
-
Go to Log & Report > Security Events and select AntiVirus.
-
View the log details in the GUI, or download the log file:
1: date=2024-02-01 time=08:47:25 eventtime=1706734045777192462 tz="+1200" logid="0954024576" type="utm" subtype="dlp" eventtype="dlp" level="warning" vd="root" ruleid=1 dlpextra="Critical" filtertype="fingerprint" filtercat="file" severity="medium" policyid=1 poluuid="f4fe48a4-938c-51ee-8856-3e84e3b24af4" policytype="policy" sessionid=308873 epoch=813849496 eventid=0 srcip=13.13.13.13 srcport=51058 srccountry="United States" srcintf="port2" srcintfrole="undefined" srcuuid="d2f06fda-15e7-51ee-0d22-faaf5170dad2" dstip=172.16.200.55 dstport=443 dstcountry="Reserved" dstintf="port1" dstintfrole="undefined" dstuuid="d2f06fda-15e7-51ee-0d22-faaf5170dad2" proto=6 service="HTTPS" filetype="unknown" direction="incoming" action="block" hostname="172.16.200.55" url="https://172.16.200.55/testdlp.txt" agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/121.0.0.0 Safari/537.36 Edg/121.0.0.0" httpmethod="GET" filename="testdlp.txt" filesize=20 profile="fingerprint"

