ZTNA traffic forwarding proxy
For security-sensitive network services running on a host in cloud, partner site, or internal network, the host does not have any open ports to be detected by a network scanner or DDOS attacker. Instead, the host relies on a ZTNA service connector to facilitate outbounding connection to a ZTNA access proxy and connect to the network service. Below is the process for a client to access the network service:
-
The client makes a connection to the ZTNA edge and requests to access the registered network service.
-
The ZTNA edge performs ZTNA check and enforces ZTNA policy. If the request is allowed, it signals the intention through control connection.
-
The ZTNA service connector triggers a connection to the ZTNA edge and another connection to the server.
-
The ZTNA edge forwards the request through ZTNA service connector to the server.
FortiProxy as a forward proxy
This applies when a FortiProxy is directly between a client and a server.
To configure FortiProxy as the ZTNA traffic forwarding proxy:
config firewall policy
edit 15
set type ztna-proxy
set uuid c7207330-bc99-51ef-6ab2-be36a0752438
set srcintf "any"
set dstintf "any"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set ztna-proxy "ztfp"
set logtraffic all
set logtraffic-start enable
set log-http-transaction enable
set extended-log enable
set ssl-ssh-profile "deep-inspection"
next
end
config ztna traffic-forward-proxy
edit "ztfp"
set vip "vip1"
next
end
config firewall vip
edit "vip1"
set uuid 526803fa-bca3-51ef-6362-2d8a9bb7b6e4
set type access-proxy
set server-type https
set extip 10.121.1.209
set extintf "any"
set extport 8443
set ssl-certificate "Fortinet_SSL"
next
end
Example ZTNA log the FortiProxy:
date=2024-12-17 time=11:04:32 eventtime=1734462272753347831 tz="-0800" logid="0005000024" type="traffic" subtype="ztna" level="notice" vd="root" srcip=10.121.1.27 srcport=55783 srcintf="port5" srcintfrole="undefined" dstcountry="Reserved" srccountry="Reserved" dstip=172.18.20.80 dstport=22 dstintf="port1" dstintfrole="undefined" sessionid=1392251262 service="SSH" proxyapptype="http" proto=6 action="accept" policyid=15 policytype="proxy-policy" poluuid="c7207330-bc99-51ef-6ab2-be36a0752438" policyname="test1" clientip=10.121.1.27 appcat="unscanned" duration=25 gatewayid=1 vip="vip1" clientdevicemanageable="unknown" clientcert="no" wanin=4738 rcvdbyte=4738 wanout=3540 lanin=4417 sentbyte=4417 lanout=6662 fctuid="70A5C5FABBE64A9B98B6DDA3FE8AC794" unauthuser="guodong" unauthusersource="forticlient" srcremote=207.102.138.19
Example forward traffic log on the FortiProxy:
date=2024-12-17 time=11:04:07 eventtime=1734462247388211699 tz="-0800" logid="0000000015" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.121.1.27 srcport=55783 srcintf="port5" srcintfrole="undefined" dstip=172.18.20.80 clientip=10.121.1.27 dstport=22 dstintf="port1" dstintfrole="undefined" srccountry="Reserved" dstcountry="Reserved" sessionid=1392251262 proto=6 action="start" policyid=15 policytype="policy" poluuid="c7207330-bc99-51ef-6ab2-be36a0752438" policyname="test1" service="SSH" trandisp="noop" url="https://10.121.1.209/tcp?address=172.18.20.80&port=22&tls=1" agent="Forticlient" appcat="unscanned" duration=0 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0 fctuid="70A5C5FABBE64A9B98B6DDA3FE8AC794" unauthuser="guodong" unauthusersource="forticlient" srcremote=207.102.138.19
FortiProxy as proxy to a service connector
To configure FortiProxy as the proxy to a service connector:
-
Configure the first FortiProxy (209 in this example) as follows:
config firewall policy
edit 15
set type ztna-proxy
set name "test2"
set uuid c7207330-bc99-51ef-6ab2-be36a0752438
set srcintf "any"
set dstintf "any"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set ztna-proxy "fwdfpx208"
set logtraffic all
set logtraffic-start enable
set log-http-transaction enable
set extended-log enable
set ssl-ssh-profile "deep-inspection"
next
end
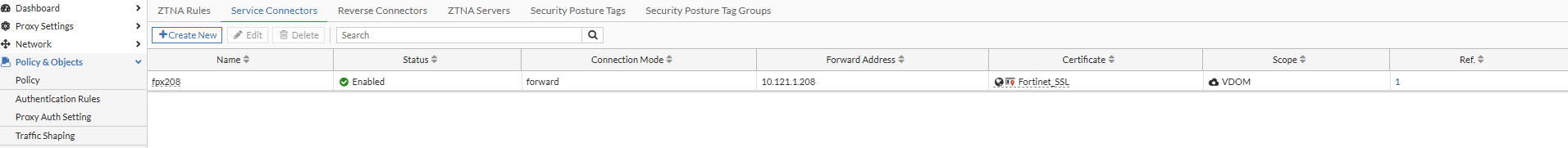
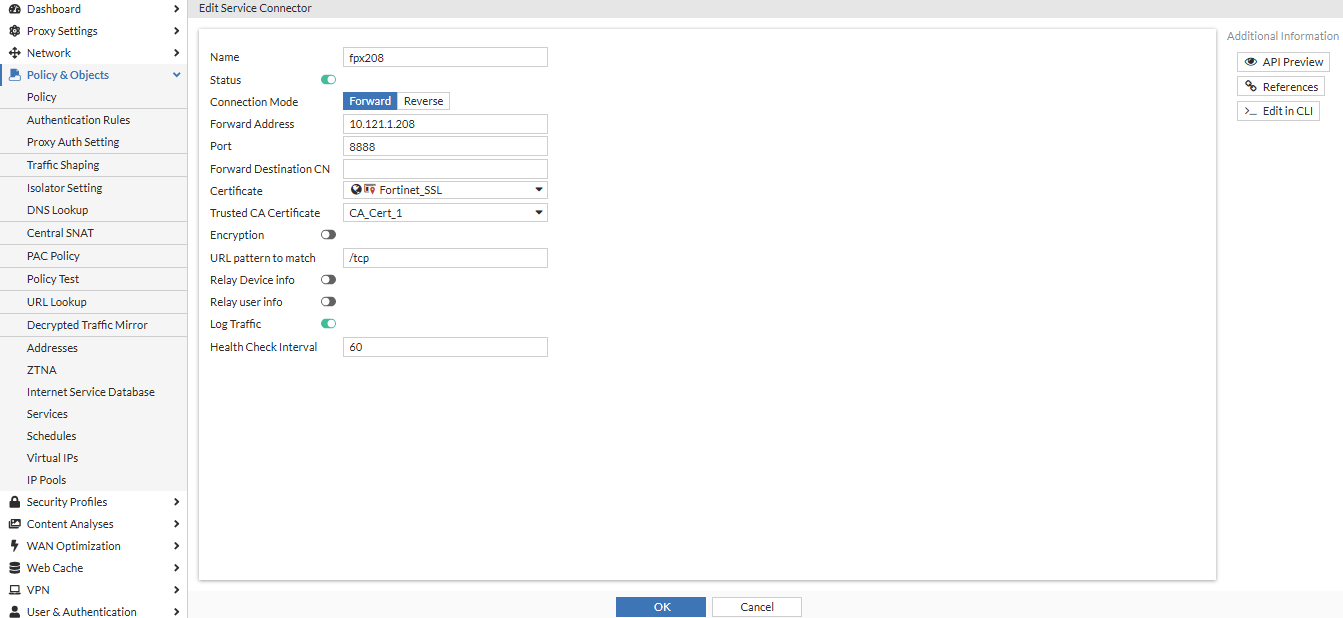
config ztna service-connector
edit "fpx208"
set connection-mode forward
set forward-address "10.121.1.208"
set forward-port 8888
set certificate "Fortinet_SSL"
set trusted-ca "CA_Cert_1"
next
end
config ztna traffic-forward-proxy
edit "fwdfpx208"
config url-route
edit "for208"
set service-connector "fpx208"
next
end
set vip "vip2"
next
end
config firewall vip
edit "vip2"
set uuid 21beb26e-bca6-51ef-f49d-42e366afdab8
set type access-proxy
set server-type https
set extip 10.121.1.209
set extintf "any"
set extport 8888
set ssl-certificate "Fortinet_SSL"
next
end
-
Configure the second FortiProxy (208 in this example) as follows:
config firewall policy
edit 4
set type ztna-proxy
set name "test2"
set uuid e7e77c9c-bca5-51ef-8cc3-275398e1d455
set dstintf "any"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set ztna-proxy "1"
set logtraffic all
set logtraffic-start enable
set log-http-transaction enable
set extended-log enable
set ssl-ssh-profile "deep-inspection"
next
end
config ztna traffic-forward-proxy
edit "1"
set vip "vip208"
next
end
config firewall vip
edit "vip208"
set uuid 869d9b74-bca5-51ef-34f6-343c7d20efe7
set type access-proxy
set server-type https
set extip 10.121.1.208
set extintf "any"
set client-cert disable
set extport 8888
set ssl-certificate "208cert"
next
end
Example forward traffic log on first FortiProxy:
date=2024-12-19 time=09:51:00 eventtime=1734630659815265080 tz="-0800" logid="0000000015" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.121.1.27 srcport=53062 srcintf="port5" srcintfrole="undefined" dstip=10.121.1.208 clientip=10.121.1.27 dstport=8888 dstintf="port5" dstintfrole="undefined" srccountry="Reserved" dstcountry="Reserved" sessionid=1679660394 proto=6 action="start" policyid=15 policytype="policy" poluuid="c7207330-bc99-51ef-6ab2-be36a0752438" policyname="test2" service="tcp/8888" trandisp="noop" url="https://10.121.1.209/tcp?address=172.18.20.84&port=22&tls=1" agent="Forticlient" appcat="unscanned" duration=0 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0 fctuid="70A5C5FABBE64A9B98B6DDA3FE8AC794" unauthuser="guodong" unauthusersource="forticlient" srcremote=207.102.138.19
Example ZTNA log on first FortiProxy:
date=2024-12-19 time=09:51:06 eventtime=1734630666432308571 tz="-0800" logid="0005000024" type="traffic" subtype="ztna" level="notice" vd="root" srcip=10.121.1.27 srcport=53062 srcintf="port5" srcintfrole="undefined" dstcountry="Reserved" srccountry="Reserved" dstip=10.121.1.208 dstport=8888 dstintf="port5" dstintfrole="undefined" sessionid=1679660394 service="tcp/8888" proxyapptype="http" proto=6 action="accept" policyid=15 policytype="proxy-policy" poluuid="c7207330-bc99-51ef-6ab2-be36a0752438" policyname="test2" clientip=10.121.1.27 appcat="unscanned" duration=7 gatewayid=1 vip="vip2" clientdevicemanageable="manageable" clientcert="yes" wanin=0 rcvdbyte=0 wanout=0 lanin=3782 sentbyte=3782 lanout=3600 fctuid="70A5C5FABBE64A9B98B6DDA3FE8AC794" unauthuser="guodong" unauthusersource="forticlient" srcremote=207.102.138.19
Example forward traffic log on second FortiProxy:
date=2024-12-19 time=09:51:00 eventtime=1734630660241936738 tz="-0800" logid="0000000015" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.121.1.209 srcport=7844 srcintf="port3" srcintfrole="undefined" dstip=172.18.20.84 clientip=10.121.1.209 dstport=22 dstintf="port1" dstintfrole="undefined" srccountry="Reserved" dstcountry="Reserved" sessionid=582239958 proto=6 action="start" policyid=4 policytype="policy" poluuid="e7e77c9c-bca5-51ef-8cc3-275398e1d455" policyname="test2" service="SSH" trandisp="noop" url="https://10.121.1.208/tcp?address=172.18.20.84&port=22&tls=1" agent="Forticlient" appcat="unscanned" duration=0 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0
Example ZTNA log on second FortiProxy:
date=2024-12-19 time=09:51:06 eventtime=1734630666285628785 tz="-0800" logid="0005000024" type="traffic" subtype="ztna" level="notice" vd="root" srcip=10.121.1.209 srcport=7844 srcintf="port3" srcintfrole="undefined" dstcountry="Reserved" srccountry="Reserved" dstip=172.18.20.84 dstport=22 dstintf="port1" dstintfrole="undefined" sessionid=582239958 service="SSH" proxyapptype="http" proto=6 action="accept" policyid=4 policytype="proxy-policy" poluuid="e7e77c9c-bca5-51ef-8cc3-275398e1d455" policyname="test2" clientip=10.121.1.209 appcat="unscanned" duration=7 gatewayid=1 vip="vip208" clientdevicemanageable="unknown" clientcert="no" wanin=1650 rcvdbyte=1650 wanout=1772 lanin=2570 sentbyte=2570 lanout=3062
FortiProxy as reverse proxy to service connector
To configure FortiProxy as the reverse proxy to a service connector:
-
Configure the first FortiProxy (209 in this example) as follows:
config firewall policy
edit 16
set type ztna-proxy
set name "test3"
set uuid c62496ca-be36-51ef-490c-4f2ee03279a9
set srcintf "any"
set dstintf "any"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set ztna-proxy "re208"
set logtraffic all
set logtraffic-start enable
set log-http-transaction enable
set extended-log enable
next
end
config ztna traffic-forward-proxy
edit "re208"
config url-route
edit "re208"
set service-connector "rs1"
next
end
set vip "vip3"
next
end
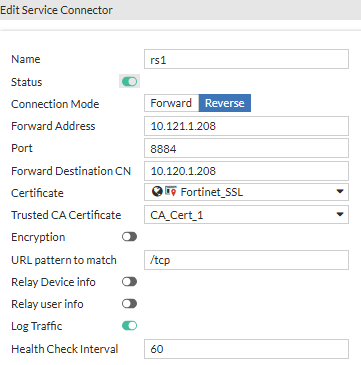
config ztna service-connector
edit "rs1"
set connection-mode reverse
set forward-address "10.121.1.208"
set forward-port 8884
set forward-destination-cn "10.120.1.208"
set certificate "Fortinet_SSL"
set trusted-ca "CA_Cert_1"
next
end
config firewall vip
edit "vip3"
set uuid 022945e0-be36-51ef-6edf-96a8bfbb880c
set type access-proxy
set server-type https
set extip 10.121.1.209
set extintf "any"
set extport 8844
set ssl-certificate "Fortinet_SSL"
next
end

config ztna connector-service-edge
set status enable
set interface "port5"
set port 8899
set server-cert "209cert"
set trusted-client-ca "CA_Cert_1"
end
-
Configure the second FortiProxy (208 in this example) as follows:
config firewall policy
edit 5
set type ztna-proxy
set name "test3"
set uuid 647928bc-be38-51ef-5ae5-b0b34c7f11df
set srcintf "any"
set dstintf "any"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set ztna-proxy "2"
set logtraffic all
set logtraffic-start enable
set log-http-transaction enable
set extended-log enable
next
end
config ztna traffic-forward-proxy
edit "2"
set vip "vip2"
next
end
config firewall vip
edit "vip2"
set uuid 992b5256-be38-51ef-56e6-a5c8c29c209e
set type access-proxy
set server-type https
set extip 10.121.1.208
set extintf "any"
set client-cert disable
set extport 8884
set ssl-certificate "208cert"
next
end
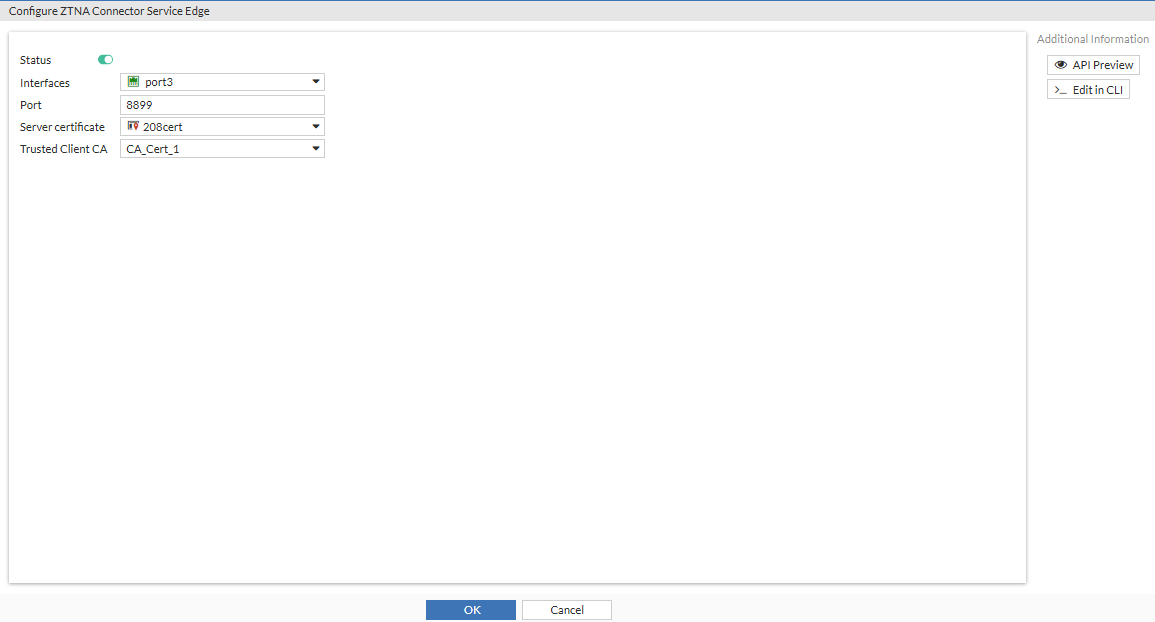
config ztna connector-service-edge
set status enable
set interface "port3"
set port 8899
set server-cert "208cert"
set trusted-client-ca "CA_Cert_1"
end
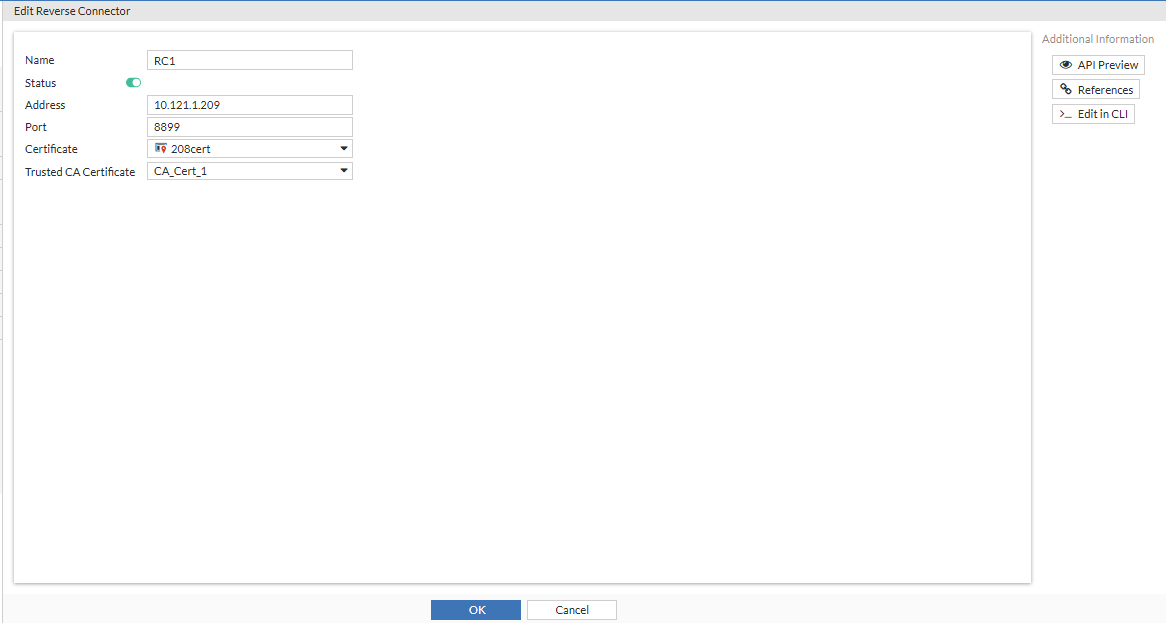
config ztna reverse-connector
edit "RC1"
set address "10.121.1.209"
set port 8899
set certificate "208cert"
set trusted-server-ca "CA_Cert_1"
next
end
Example forward traffic log on first FortiProxy:
date=2024-12-19 time=13:28:01 eventtime=1734643680738100796 tz="-0800" logid="0000000015" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.121.1.27 srcport=55399 srcintf="port5" srcintfrole="undefined" dstip=10.121.1.208 clientip=10.121.1.27 dstport=8884 dstintf="port5" dstintfrole="undefined" srccountry="Reserved" dstcountry="Reserved" sessionid=1534640176 proto=6 action="start" policyid=16 policytype="policy" poluuid="c62496ca-be36-51ef-490c-4f2ee03279a9" policyname="test3" service="tcp/8884" trandisp="noop" url="https://10.121.1.209/tcp?address=172.18.20.83&port=22&tls=1" agent="Forticlient" appcat="unscanned" duration=0 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0 fctuid="70A5C5FABBE64A9B98B6DDA3FE8AC794" unauthuser="guodong" unauthusersource="forticlient" srcremote=207.102.138.19
Example ZTNA log on first FortiProxy:
date=2024-12-19 time=12:02:14 eventtime=1734638533879306863 tz="-0800" logid="0005000024" type="traffic" subtype="ztna" level="notice" vd="root" srcip=10.121.1.27 srcport=54459 srcintf="port5" srcintfrole="undefined" dstcountry="Reserved" srccountry="Reserved" dstip=10.121.1.208 dstport=8884 dstintf="port5" dstintfrole="undefined" sessionid=1534640175 service="tcp/8884" proxyapptype="http" proto=6 action="accept" policyid=16 policytype="proxy-policy" poluuid="c62496ca-be36-51ef-490c-4f2ee03279a9" policyname="test3" clientip=10.121.1.27 appcat="unscanned" duration=121 gatewayid=1 vip="vip3" clientdevicemanageable="manageable" clientcert="yes" wanin=0 rcvdbyte=0 wanout=0 lanin=3782 sentbyte=3782 lanout=3514 fctuid="70A5C5FABBE64A9B98B6DDA3FE8AC794" unauthuser="guodong" unauthusersource="forticlient" srcremote=207.102.138.19
Example forward traffic log on second FortiProxy:
date=2024-12-19 time=13:28:01 eventtime=1734643681000410543 tz="-0800" logid="0000000015" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.121.1.208 srcport=38864 srcintf="unknown-0" srcintfrole="undefined" dstip=172.18.20.83 dstport=22 dstintf="port1" dstintfrole="undefined" srccountry="Reserved" dstcountry="Reserved" sessionid=1842818121 proto=6 action="start" policyid=5 policytype="policy" poluuid="647928bc-be38-51ef-5ae5-b0b34c7f11df" policyname="test3" service="SSH" trandisp="noop" url="https://10.121.1.208/tcp?address=172.18.20.83&port=22&tls=1" agent="Forticlient" appcat="unscanned" duration=0 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0
FortiProxy as reverse proxy to service connector with relay info (authentication)
To configure FortiProxy as the reverse proxy to a service connector with authentication:
-
Configure the first FortiProxy (209 in this example) as follows:
config firewall policy
edit 17
set type ztna-proxy
set name "test4"
set uuid 4cb311a2-be51-51ef-2ca9-e44aa30538be
set srcintf "any"
set dstintf "any"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set ztna-proxy "re208"
set logtraffic all
set logtraffic-start enable
set log-http-transaction enable
set extended-log enable
set groups "ldap-grp"
next
end
config ztna service-connector
edit "rs1"
set connection-mode reverse
set forward-address "10.121.1.208"
set forward-port 8884
set forward-destination-cn "10.120.1.208"
set certificate "Fortinet_SSL"
set trusted-ca "CA_Cert_1"
set relay-user-info enable
relay-user
next
end
config ztna traffic-forward-proxy
edit "re208"
config url-route
edit "re208"
set service-connector "rs1"
next
end
set vip "vip3"
next
end
config ztna connector-service-edge
set status enable
set interface "port5"
set port 8899
set server-cert "209cert"
set trusted-client-ca "CA_Cert_1"
end
config firewall vip
edit "vip3"
set uuid 022945e0-be36-51ef-6edf-96a8bfbb880c
set type access-proxy
set server-type https
set extip 10.121.1.209
set extintf "any"
set extport 8844
set ssl-certificate "Fortinet_SSL"
next
end
config authentication scheme
edit "fac_ldap_scheme"
set method basic
set user-database "ldap"
next
end
config authentication rule
edit "ru-basic"
set srcintf "any"
set srcaddr "all"
set dstaddr "all"
set active-auth-method " fac_ldap_scheme"
next
end
-
Configure the second FortiProxy (208 in this example) as follows:
config firewall policy
edit 6
set type ztna-proxy
set name "test4"
set uuid 765dbc14-be51-51ef-c1d3-a20777201165
set srcintf "any"
set dstintf "any"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set ztna-proxy "2"
set logtraffic all
set logtraffic-start enable
set log-http-transaction enable
set extended-log enable
set groups "ldap-grp"
next
end
config ztna reverse-connector
edit "RC1"
set address "10.121.1.209"
set port 8899
set certificate "208cert"
set trusted-server-ca "CA_Cert_1"
next
end
config ztna traffic-forward-proxy
edit "2"
set vip "vip2"
next
end
config firewall vip
edit "vip2"
set uuid 992b5256-be38-51ef-56e6-a5c8c29c209e
set type access-proxy
set server-type https
set extip 10.121.1.208
set extintf "any"
set client-cert disable
set extport 8884
set ssl-certificate "208cert"
next
end
config authentication scheme
edit "ztna"
set method ztna-relay
set user-database "ldap"
next
end
config authentication rule
edit "rule-relay"
set srcintf "any"
set srcaddr "all"
set dstaddr "all"
set sso-auth-method "ztna"
next
end
Example forward traffic log on first FortiProxy:
date=2025-02-12 time=14:48:02 eventtime=1739400481939063719 tz="-0800" logid="0000000015" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.121.1.27 srcport=49436 srcintf="port5" srcintfrole="undefined" dstip=10.121.1.208 clientip=10.121.1.27 dstport=8884 dstintf="port5" dstintfrole="undefined" srccountry="Reserved" dstcountry="Reserved" sessionid=1368748332 proto=6 action="start" policyid=17 policytype="policy" poluuid="4cb311a2-be51-51ef-2ca9-e44aa30538be" policyname="test4" user="usera@qa.domaintest.com" group="ldap-grp" service="tcp/8884" trandisp="noop" url="https://10.121.1.209/tcp?address=172.18.20.83&port=22&tls=1" agent="Forticlient" appcat="unscanned" duration=0 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0 fctuid="70A5C5FABBE64A9B98B6DDA3FE8AC794" unauthuser="guodong" unauthusersource="forticlient" srcremote=207.102.138.19
Example ZTNA log on first FortiProxy:
date=2025-02-12 time=14:49:56 eventtime=1739400596457255371 tz="-0800" logid="0005000024" type="traffic" subtype="ztna" level="notice" vd="root" srcip=10.121.1.27 srcport=49436 srcintf="port5" srcintfrole="undefined" dstcountry="Reserved" srccountry="Reserved" dstip=10.121.1.208 dstport=8884 dstintf="port5" dstintfrole="undefined" sessionid=1368748332 service="tcp/8884" proxyapptype="http" proto=6 action="accept" policyid=17 policytype="proxy-policy" poluuid="4cb311a2-be51-51ef-2ca9-e44aa30538be" policyname="test4" clientip=10.121.1.27 appcat="unscanned" duration=115 user="usera@qa.domaintest.com" group="ldap-grp" gatewayid=1 vip="vip3" clientdevicemanageable="manageable" clientcert="yes" wanin=0 rcvdbyte=0 wanout=0 lanin=5249 sentbyte=5249 lanout=5552 fctuid="70A5C5FABBE64A9B98B6DDA3FE8AC794" unauthuser="guodong" unauthusersource="forticlient" srcremote=207.102.138.19
Example forward traffic log on second FortiProxy:
date=2025-02-12 time=14:49:57 eventtime=1739400596385868699 tz="-0800" logid="0005000024" type="traffic" subtype="ztna" level="notice" vd="root" srcip=10.121.1.208 srcport=12170 srcintf="unknown-0" srcintfrole="undefined" dstcountry="Reserved" srccountry="Reserved" dstip=172.18.20.83 dstport=22 dstintf="port1" dstintfrole="undefined" sessionid=2131368715 service="SSH" proxyapptype="http" proto=6 action="accept" policyid=6 policytype="proxy-policy" poluuid="765dbc14-be51-51ef-c1d3-a20777201165" policyname="test4" appcat="unscanned" duration=114 user="usera@qa.domaintest.com" group="ldap-grp" gatewayid=1 vip="vip2" clientdevicemanageable="unknown" clientcert="no" wanin=3341 rcvdbyte=3341 wanout=3036 lanin=0 sentbyte=0 lanout=0

