Managing referrer logs
FortiRecon analyzes web referrer logs to identify potential phishing attacks. Web referrer logs provide valuable insights into the links that direct traffic to your website. In a typical phishing attack, threat actors redirect victims to the legitimate site after capturing sensitive information. By analyzing these logs, FortiRecon can detect suspicious referrer patterns indicative of phishing activity.
To enable this analysis, you must configure a periodic cron job to upload your web referrer logs to FortiRecon via Amazon Web Services Command Line Interface (AWS CLI).
Before uploading log files, ensure that AWS CLI is installed and configured on the server where the logs are stored. Perform the following steps to setup referrer logs.
-
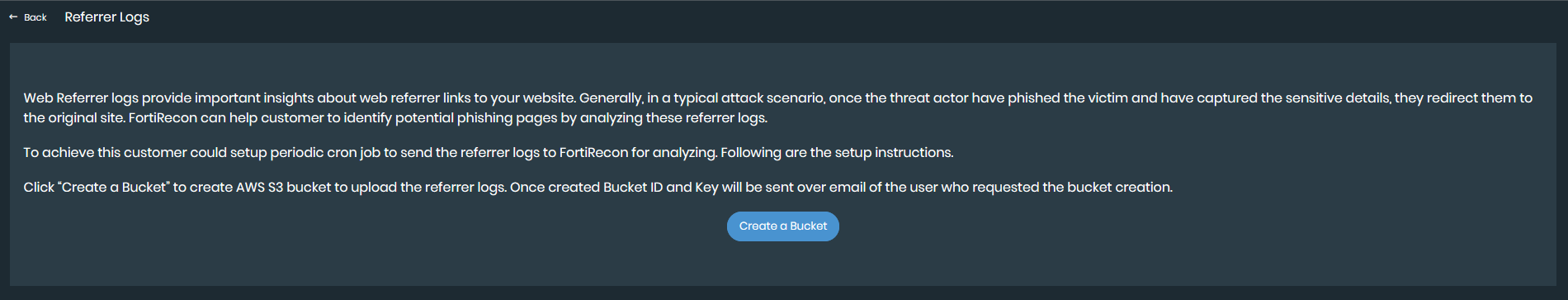
Create AWS Bucket. You need to create a new S3 bucket once, for the initial setup.
-
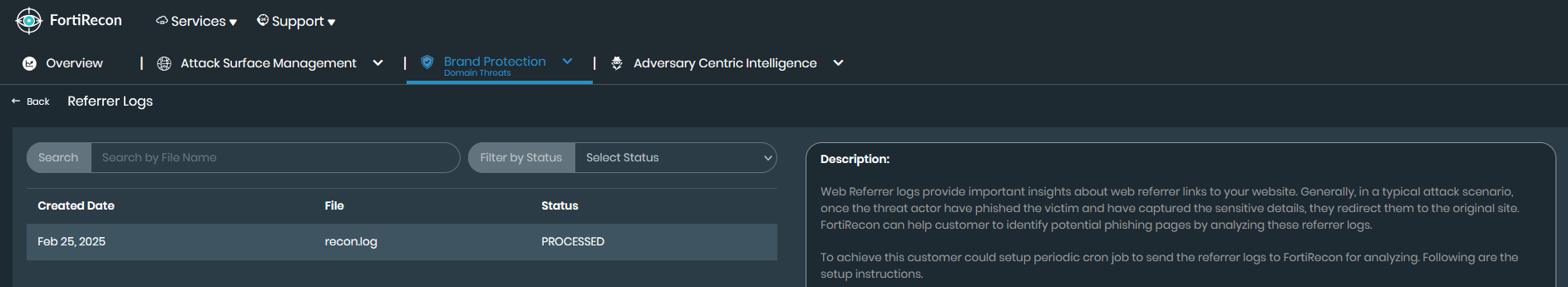
In FortiRecon, navigate to Brand Protection > Domain Threats > Manage Referrer Logs.
-
Click Create a Bucket.
-
Upon successful bucket creation, the necessary access information will be shared with you via email.
-
-
Download and Install AWS CLI. Install AWS CLI on your system using the appropriate commands for your operating system:
-
Windows: Download the installer from the AWS CLI Installation page.
-
macOS: Run the command
brew install awscliin your terminal. -
Linux: Run the following command in your terminal.
-
For Debian-based systems, run the command
sudo apt-get install awscli. -
For Red Hat-based systems, execute the command
sudo yum install aws-cli.
-
-
-
Configure AWS CLI. After installing AWS CLI, configure it with your AWS access key and secret key shared via email.
-
Open your terminal or command prompt.
-
Run the command
aws configure. -
Enter your credentials when prompted.
-
AWS Access Key ID: Enter your access key.
-
AWS Secret Access Key: Enter your secret key.
-
Default region name: Enter your preferred AWS region (e.g., us-east-1).
-
Default output format: Press Enter to accept the default (usually json).
-
-
-
Upload Log Files. Upload your log files to the designated S3 bucket using the following command.
aws s3 cp /path/to/local/file s3://your-bucket-name/Replace /path/to/local/file with the actual path to your log file.
Replace your-bucket-name with the name of your S3 bucket.
Example:
aws s3 cp /home/user/documents/apache.log s3://cddf82s42-22sced-e6nws4c436-referal-logs-testing/Co531lMJyOQXBJI9741ifVwgNPSGaNCJ1F0qqGlUNECTHbfMHiBvbg5tnsoJRAw3/
|
|
|

