Add AWS Organization: Fix No Permission Status
Background
In order for master account to be able to add the sub-account to FortiCNP, there needs to be a preconfigured account access role with adequate permission. The role acts as an agreement between the master and sub-account.
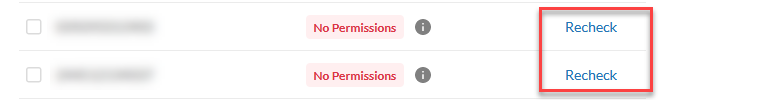
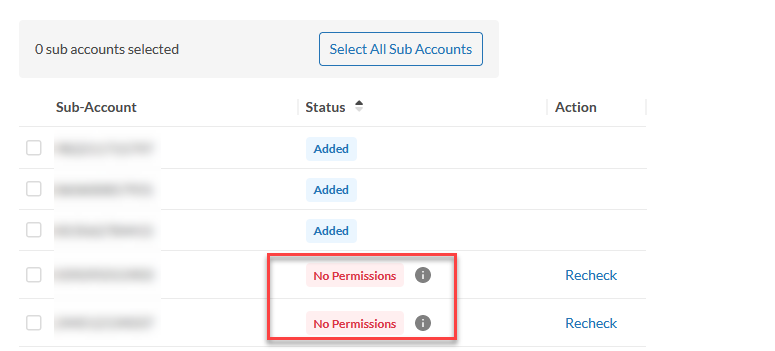
If the sub-account was not created by the master account, it does not have the role and the permission setup to connect with the master account, the sub-account status will be shown as No Permission status on FortiCNP.
Please follow the steps below to configure the role and permission for the sub-account.
First check the sub-account to see if it has the access role and permission setup. If it is not setup, then the sub-account needs to add account access role.
Check Account Access Role
- Log into AWS console with the sub-account.
- Under Services, search and click IAM.
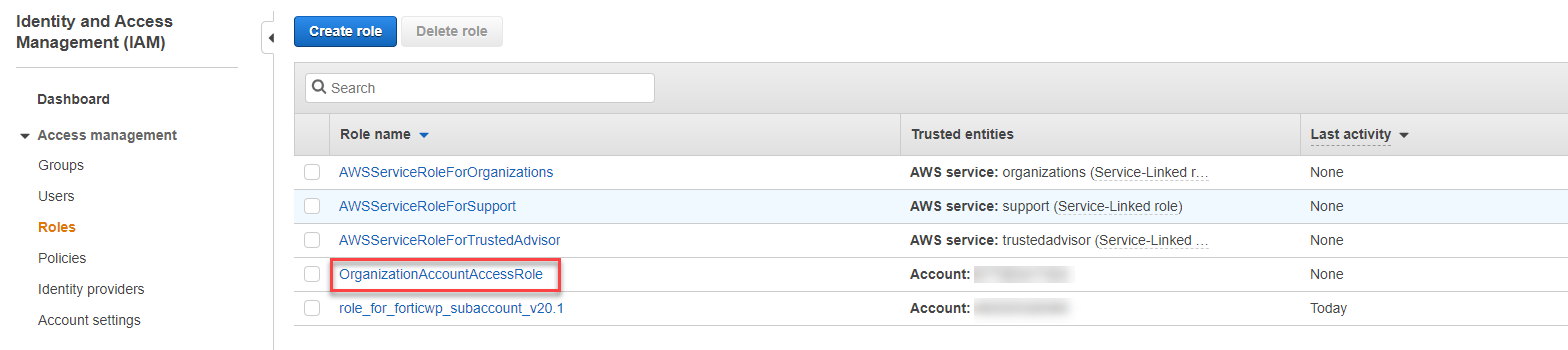
- Click Roles under Access Management,
- Search and click on "OrganizationAccountAccessRole". If it is not created, proceed to next section, Add Organization Account Access Role.
- Under Permission policies field, there should be a policy named AdministratorAccess.
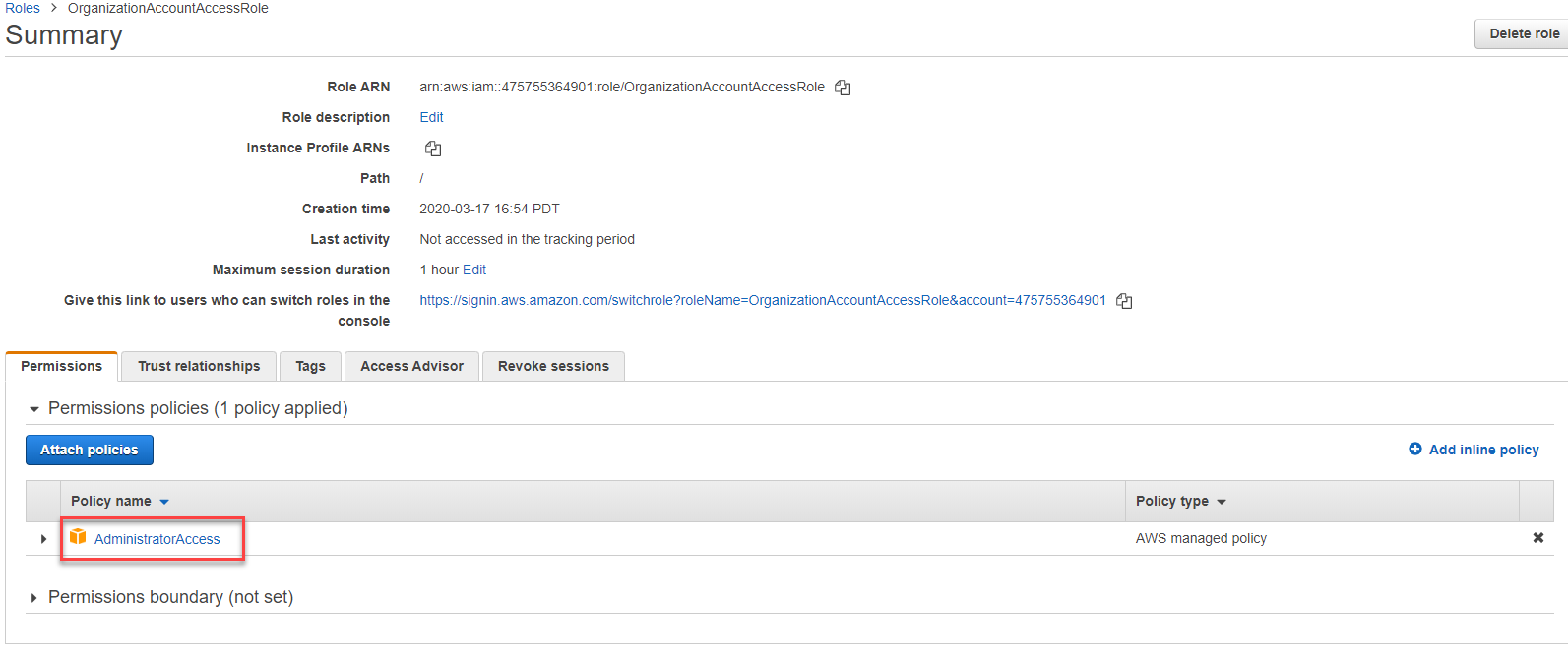
- Click on Trust relationships tab, and check the field in Trusted entities.

- The master account number should be in the trusted entities. If it is not there, delete the role, and proceed to next section to re-add "OrganizationAccountAccessRole" with the master account number.
Add Organization Account Access Role
- Log into AWS console with the sub-account.
- Under Services, search and click IAM.
- Click Roles under Access Management, and click Create role.
- Under "Select type of trusted entity", select Another AWS account, and enter the master account ID. Click Next: Permissions.
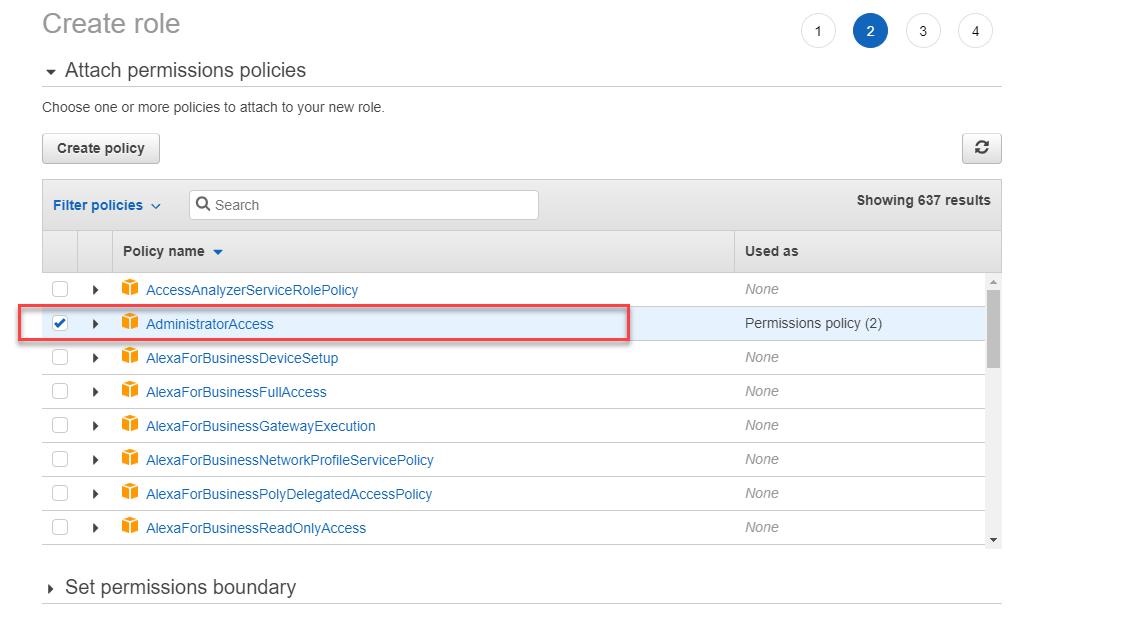
- Search and select AdministratorAccess policy then click Next:Tags.
- Click Next: Review.
- In Role Name filed, enter "OrganizationAccountAccessRole".
- Click Create role to finish.
Repeat the steps above for each of the sub-account that shows No Permission status on FortiCNP, and click Re-Check.