Lure Resources
Use the Lure Resources page to view the current lure, upload resources such as Word and PDF files to automatically generate lures, and import a user name list from an LDAP server.

Uploading lure resources
Upload a lure resource to automatically generate lures. There are two types of lure resource:
- Documents: Word and PDF files that generate authentic directories and files over the Decoy network shares.
- Credential: Username (with password) list files that generate authentic credentials access to the network Decoys.
To upload a lure resource:
- Go to Deception > Lure Resources.
- Click Upload. The Upload New Lure Resource dialog opens.
- From the Lure Type dropdown, select the lure type.
- Credential - Fake Users (txt): Upload a list file with fake users and passwords.
- Documents - Template (docx,pdf,zip): Upload files as a template. FortiDeceptor will insert content to build honey docs.
- Documents - Fake Content (zip): Upload Zip Word Document (.docx), PDF, Excel (.xlsx,.xlsm,.xltm,.xltx) then upload .zip file directly to FortiDeceptor.
Credential – AWS Key (txt): Upload a list file with AWS users and passwords.
Requirements:
- Create AWS IAM users with no permissions. (Without real AWS user, the AWS platform will not generate a log that indicates the user access.)
- Upload a text file with the correct AWS Region, AWS Access Key ID, AWS Secret Access in the format below.
AWS Access Key ID:AWS Secret Access:AWS Region:AWSusername
For more information, see Deploying AWS deception keys.
Deception SMB Token Drives (txt): Upload a text file which includes a list of customized directory names. FortiDeceptor will use the file to generate a SMB Token.

The Credential - Fake Users (txt) and Documents - Template (doc,docx,pdf,zip) options include sample files to help you create a resource.
- Enter an optional Tag, such as any.
- In the Resource File field, click Choose a file to upload the resource, or drag and drop it onto the field.
- Click Save.
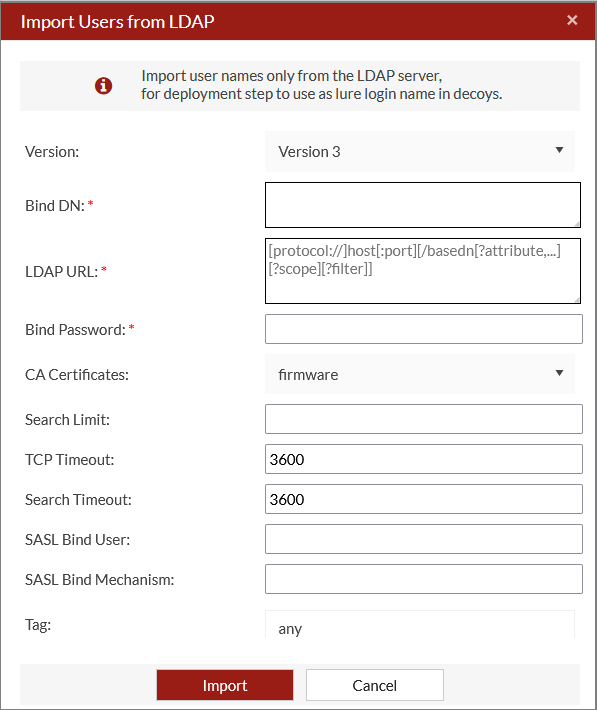
Importing users from LDAP
To import an LDAP user list:
- Go to Deception > Lure Resources.
- Click Import Users from LDAP.
- Configure the import settings.
Version Select the version from the dropdown. Bind DN Username used to connect to the LDAP service on the specified LDAP Server. LDAP URL Enter the LDAP URL using the following format:
[protocol///]host[:port][/basedn[?attribute,...][?scope][?filter]]Bind Password Enter the Bind DN's password. CA Certificates Select a certificate from the dropdown. Search Limit Search sub-tree depth. TCP Timeout Enter the TCP connection timeout in seconds. Search Timeout Enter the search timeout in seconds. SASL Bind User The username to authenticate a DN on the directory server using SASL. SASL Bind Mechanism The username and password for authentication. Tag
Enter a tag for the import.
- Click Save.
Examples: Import Users from LDAP
Open LDAP example:
"dn": "uid=test,o=org,dc=example,dc=com",
"url": "ldap://192.168.0.100/o=org,dc=example,dc=com?uid?sub?(objectclass=*)",
"password": "password"
Windows AD example:
"version": "3",
"dn": "cn=users,cn=usergroup,dc=example,dc=com",
"url": "ldap:192.168.0.100/cn=usergroup,dc=example,dc=com?sAMAccountName?sub?(objectClass=user)",
"password": "password"
Support is offered if the format of the tree can parse uid/sAMAccountName in the search results. Ensure the URL queries the proper data.

