Inline CASB
The inline CASB security profile enables the FortiGate to perform granular control over SaaS applications directly on firewall policies. The supported controls include:
|
Control |
Description |
|---|---|
|
Privilege control |
Specify the action to apply to user activities per application such as upload, download, share, delete, log in, and so on. |
|
Safe search |
On SaaS applications that support searching, enable and select the level of safe search. |
|
Tenant control |
Allow only users belonging to specific domains to access the SaaS application. |
|
UTM bypass |
For each user activity, bypass further UTM scanning any of the following security profiles:
|
Administrators can customize their own SaaS applications, matching conditions, and custom controls and actions.
A firewall policy must use proxy-based inspection with a deep inspection SSL profile to apply the inline CASB profile and scan the traffic payload.
Inline CASB can be applied to a firewall policy or a proxy policy.
|
|
The Inline-CASB Application Definitions entitlement is licensed under the basic firmware and updates contract. To view the entitlement information, go to System > FortiGuard and expand the Firmware & General Updates section in the License Information table. |
To enable inline CASB security profiles in the GUI:
-
Go to System > Feature Visibility.
-
Enable Inline-CASB in the Security Features section.
-
Click Apply.
Example 1: privilege control
In this example, logging in to Microsoft Outlook is blocked by the privilege control settings in the inline CASB profile.
To configure an inline CASB profile with privilege control in the GUI:
-
Configure the inline CASB profile:
-
Go to Security Profiles > Inline-CASB and click Create new.
-
Enter a Name, such as outlook_test.
-
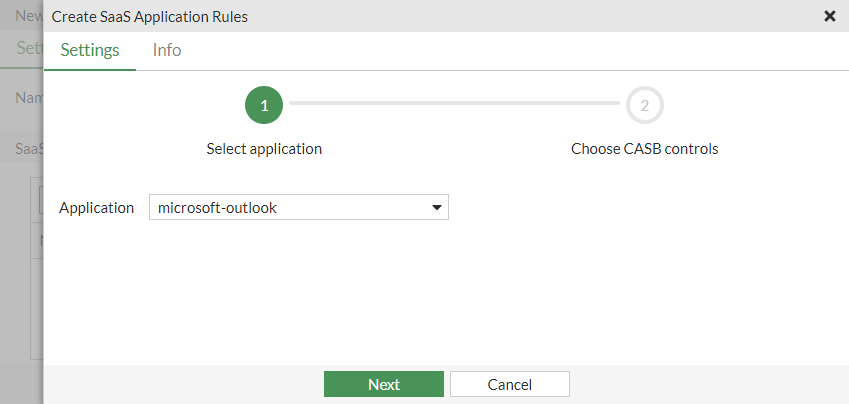
In the SaaS Applications table, click Create new. The Create SaaS Application Rules pane opens.
-
Set the Application to microsoft-outlook, then click Next.
-
Enable Logging.
-
In the Privilege Control table, select login and from the Set Action dropdown, select Block.
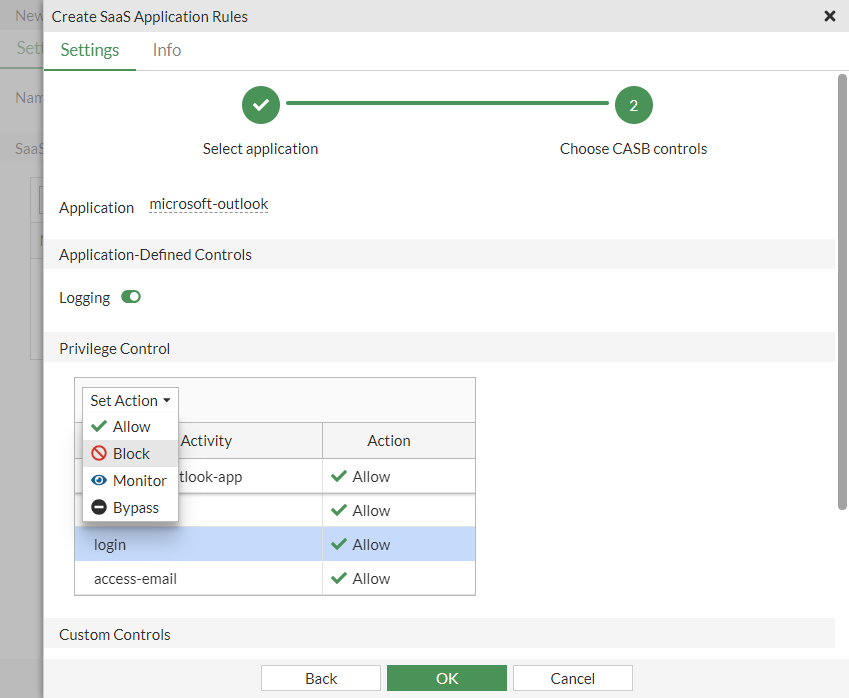
-
Click OK.
-
-
Configure the firewall policy:
-
Go to Policy & Objects > Firewall Policy. Edit an existing policy, or create a new one.
-
Set the Inspection Mode to Proxy-based.
-
In the Security Profiles section, enable Inline-CASB and select the outlook_test profile.
-
Set the SSL Inspection profile to one that uses deep inspection.
-
Configure the other settings as needed.
-
Click OK.
-
To configure an inline CASB profile with privilege control in the CLI:
-
Configure the inline CASB profile:
config casb profile edit "outlook_test" config saas-application edit "microsoft-outlook" config access-rule edit "microsoft-outlook-login" set action block next end next end next end -
Configure the firewall policy:
config firewall policy edit 6 set name "casb_test" set srcintf "port1" set dstintf "port3" set action accept set srcaddr "all" set dstaddr "all" set schedule "always" set service "ALL" set utm-status enable set inspection-mode proxy set ssl-ssh-profile "ssl" set casb-profile "outlook_test" set nat enable next end
To test the configuration:
-
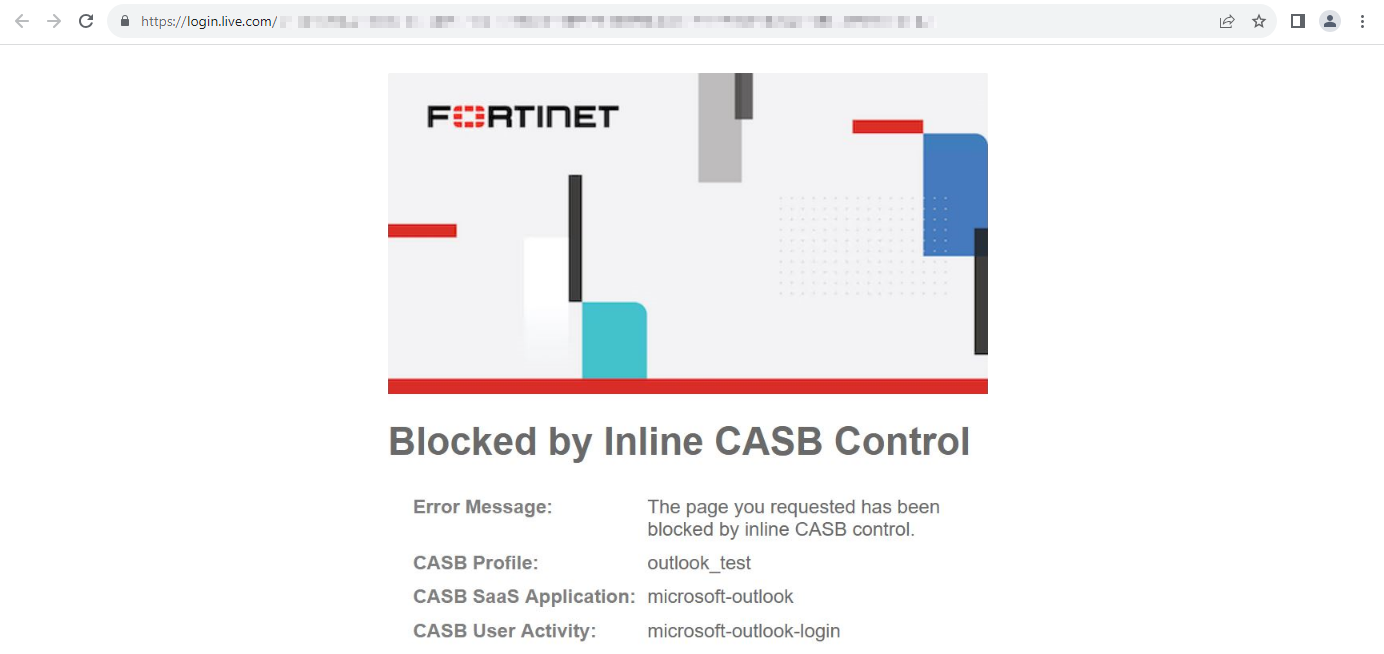
Open a browser and attempt to access the Outlook login page.
-
The traffic is blocked by the firewall policy. The browser displays a replacement message: Blocked by Inline CASB Control.
Sample log:
1: date=2023-08-18 time=16:59:32 eventtime=1692403171962221884 tz="-0700" logid="2500010000" type="utm" subtype="casb" eventtype="casb" level="warning" vd="vdom1" msg="CASB access was blocked because it contained banned activity." policyid=6 sessionid=63635 srcip=10.1.100.195 dstip=20.190.190.130 srcport=61013 dstport=443 srcintf="port1" srcintfrole="undefined" dstintf="port3" dstintfrole="undefined" proto=6 action="block" profile="outlook_test" saasapp="microsoft-outlook" useractivity="microsoft-outlook-login" activitycategory="activity-control"
Example 2: safe search
In this example, safe search is configured for Google in the inline CASB profile.
To configure an inline CASB profile with safe search in the GUI:
-
Configure the inline CASB profile:
-
Go to Security Profiles > Inline-CASB and click Create new.
-
Enter a Name, such as google_test.
-
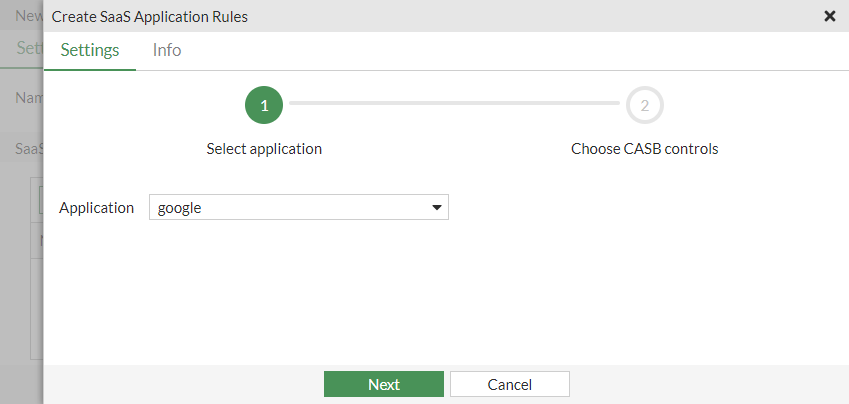
In the SaaS Applications table, click Create new. The Create SaaS Application Rules pane opens.
-
Set the Application to google, then click Next.
-
Enable Safe search.
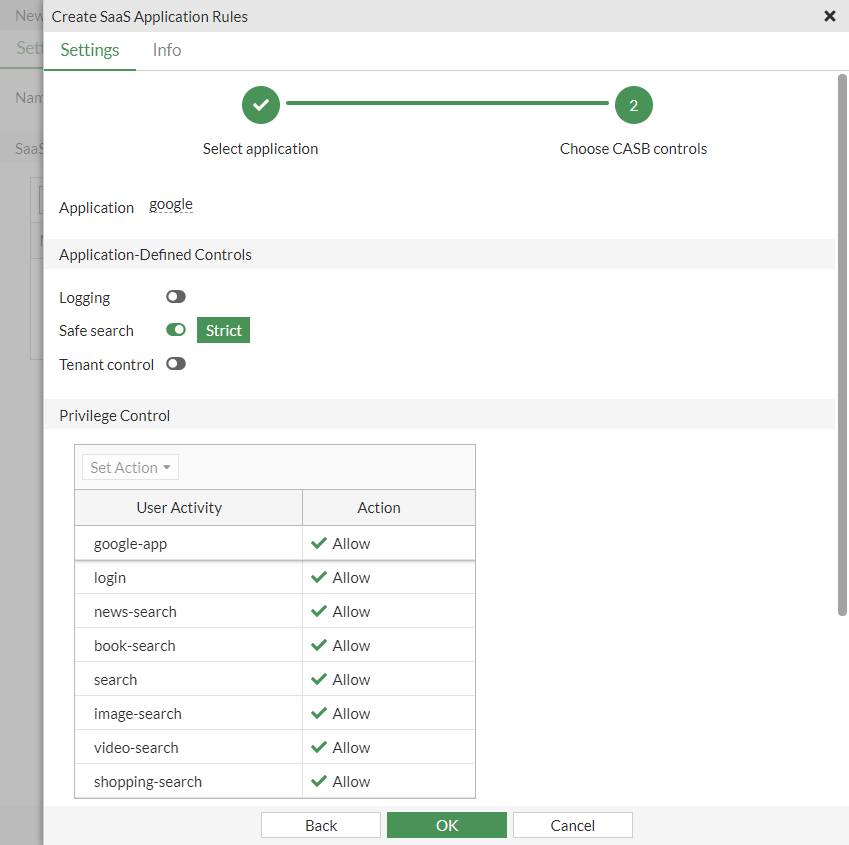
-
Click OK.
-
-
Configure the firewall policy:
-
Go to Policy & Objects > Firewall Policy. Edit an existing policy, or create a new one.
-
Set the Inspection Mode to Proxy-based.
-
In the Security Profiles section, enable Inline-CASB and select the google_test profile.
-
Set the SSL Inspection profile to one that uses deep inspection.
-
Configure the other settings as needed.
-
Click OK.
-
To configure an inline CASB profile with safe search in the CLI:
-
Configure the inline CASB profile:
config casb profile edit "google_test" config saas-application edit "google" set safe-search enable set safe-search-control "strict" next end next end -
Configure the firewall policy:
config firewall policy edit 7 set name "casb_test_google" set srcintf "port1" set dstintf "port3" set action accept set srcaddr "all" set dstaddr "all" set schedule "always" set service "ALL" set utm-status enable set inspection-mode proxy set ssl-ssh-profile "ssl" set casb-profile "google_test" set nat enable next end
To test the configuration:
-
Open a browser and attempt to search in Google for content that is considered mature or explicit.
-
The sensitive content is filtered out in the search results.
Sample log:
1: date=2023-08-18 time=17:01:36 eventtime=1692403295962385271 tz="-0700" logid="2500010002" type="utm" subtype="casb" eventtype="casb" level="information" vd="vdom1" msg="CASB access was monitored because it contained activity." policyid=7 sessionid=63774 srcip=10.1.100.195 dstip=142.250.217.98 srcport=61065 dstport=443 srcintf="port1" srcintfrole="undefined" dstintf="port3" dstintfrole="undefined" proto=6 action="monitor" profile="google_test" saasapp="google" useractivity="google-safe-search" activitycategory="safe-search-control"
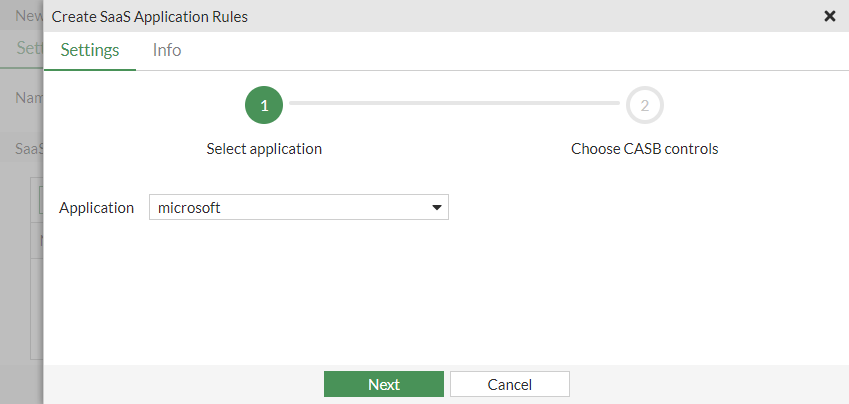
Example 3: tenant control
In this example, tenant control is configured for Microsoft in the inline CASB profile for the fortinet-us.com domain.
To configure an inline CASB profile with tenant control in the GUI:
-
Configure the inline CASB profile:
-
Go to Security Profiles > Inline-CASB and click Create new.
-
Enter a Name, such as microsoft_test.
-
In the SaaS Applications table, click Create new. The Create SaaS Application Rules pane opens.
-
Set the Application to microsoft, then click Next.
-
Enable Tenant control. Click the + and enter fortinet-us.com.
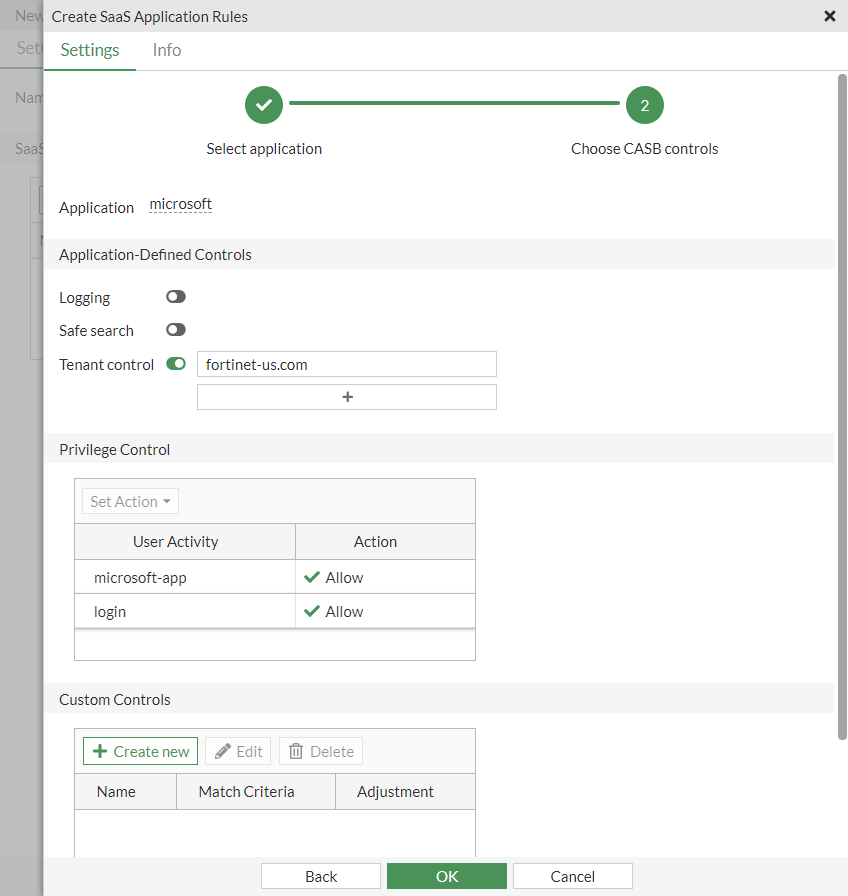
-
Click OK.
-
-
Configure the firewall policy:
-
Go to Policy & Objects > Firewall Policy. Edit an existing policy, or create a new one.
-
Set the Inspection Mode to Proxy-based.
-
In the Security Profiles section, enable Inline-CASB and select the microsoft_test profile.
-
Set the SSL Inspection profile to one that uses deep inspection.
-
Configure the other settings as needed.
-
Click OK.
-
To configure an inline CASB profile with tenant control in the CLI:
-
Configure the inline CASB profile:
config casb profile edit "microsoft_test" config saas-application edit "microsoft" set tenant-control enable set tenant-control-tenants "fortinet-us.com" next end next end -
Configure the firewall policy:
config firewall policy edit 8 set name "casb_test_microsoft" set srcintf "port1" set dstintf "port3" set action accept set srcaddr "all" set dstaddr "all" set schedule "always" set service "ALL" set utm-status enable set inspection-mode proxy set ssl-ssh-profile "ssl" set casb-profile "microsoft_test" set nat enable next end
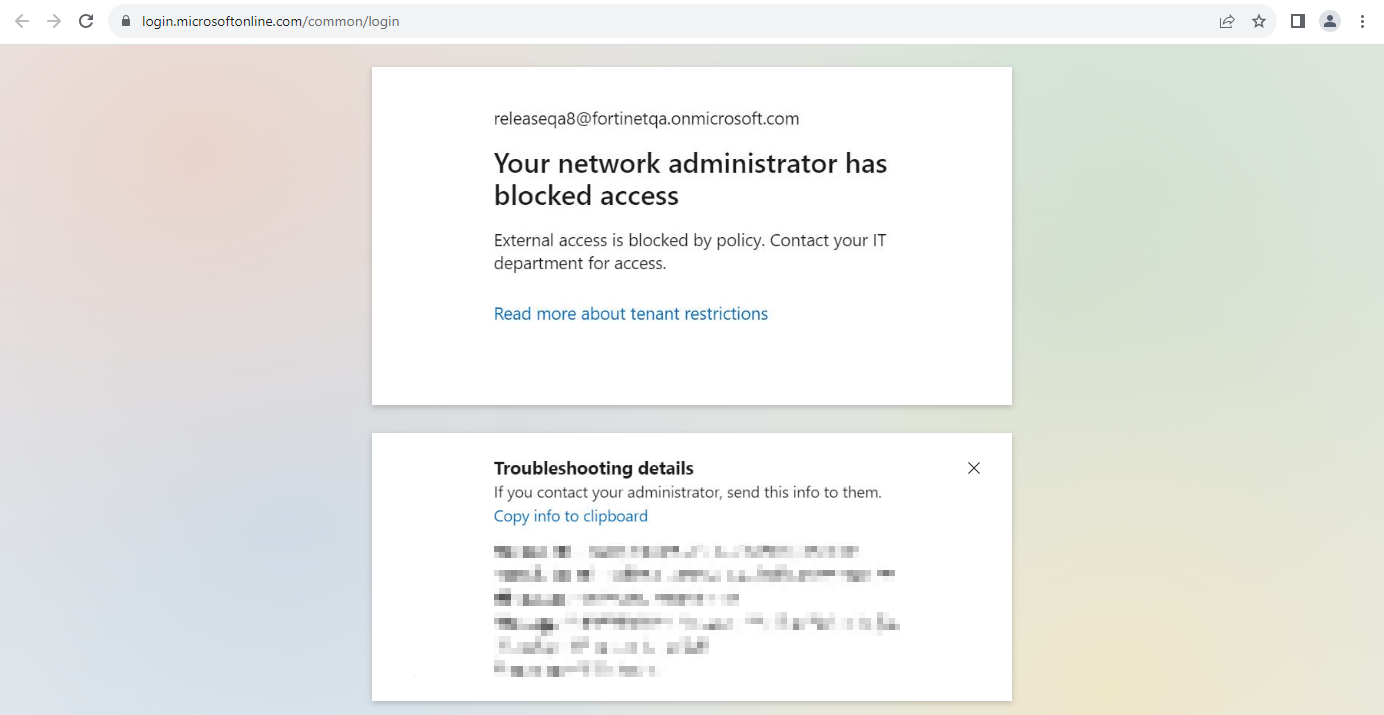
To test the configuration:
-
Open a browser and attempt to log in to Microsoft Office 365 with a fortinet-us.com account.
-
Since the domain is valid, the user can log in successfully.
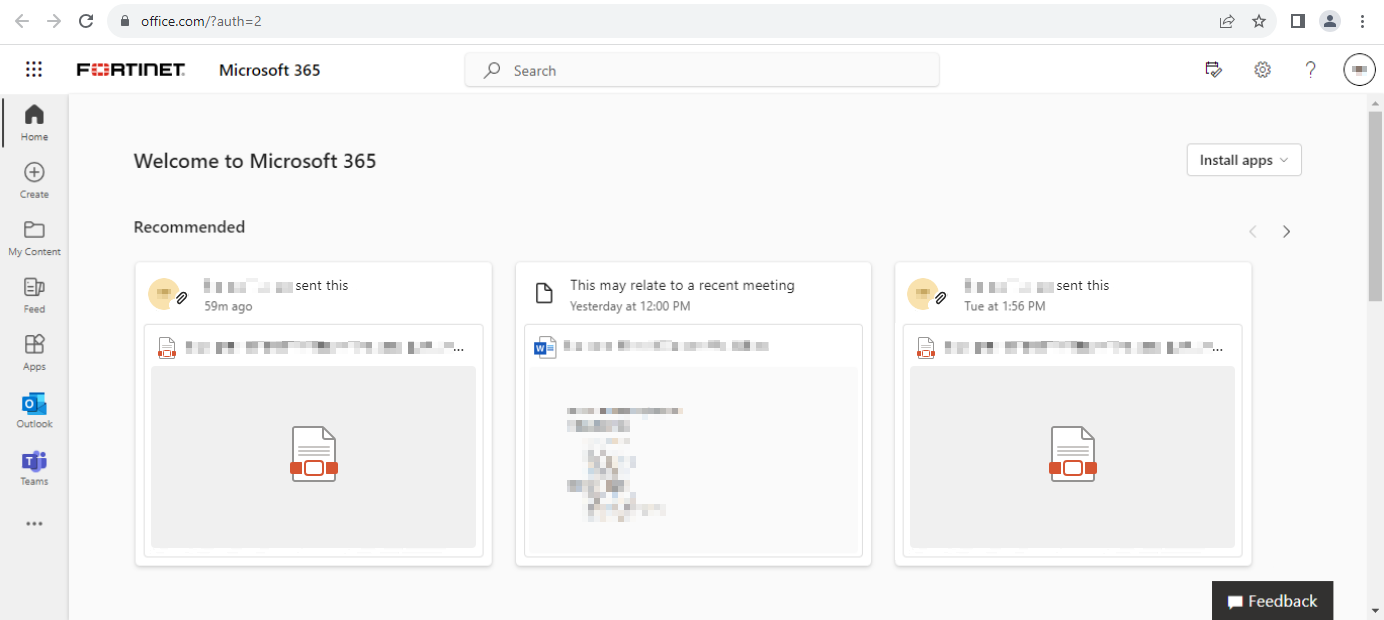
-
Attempt to log in to Microsoft Office 365 with another account with a different domain.
-
The domain is invalid. The user is unable to log in, and an error message appears: Your network administrator has blocked access.
Sample log:
1: date=2023-08-18 time=17:09:25 eventtime=1692403765238967943 tz="-0700" logid="2500010002" type="utm" subtype="casb" eventtype="casb" level="information" vd="vdom1" msg="CASB access was monitored because it contained activity." policyid=8 sessionid=65108 srcip=10.1.100.195 dstip=20.189.173.15 srcport=61912 dstport=443 srcintf="port1" srcintfrole="undefined" dstintf="port3" dstintfrole="undefined" proto=6 action="monitor" profile="microsoft_test" saasapp="microsoft" useractivity="ms-tenant-control" activitycategory="tenant-control"
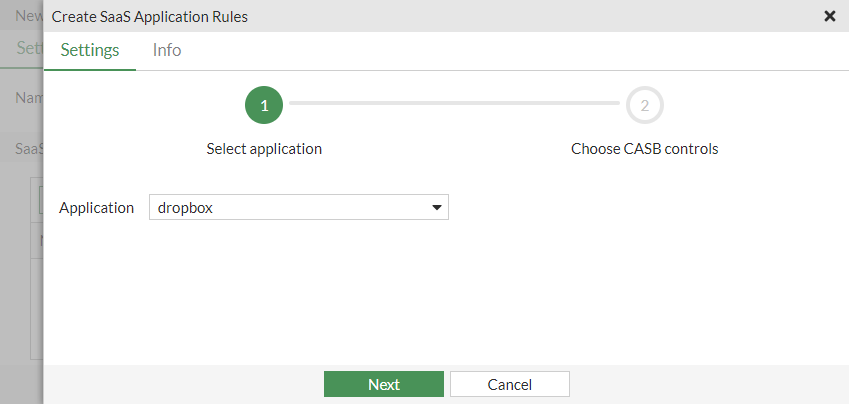
Example 4: UTM bypass
In this example, UTM bypass is configured for Dropbox file downloading in the inline CASB profile.
To configure an inline CASB profile with UTM bypass in the GUI:
-
Configure the inline CASB profile:
-
Go to Security Profiles > Inline-CASB and click Create new.
-
Enter a Name, such as dropbox_test.
-
In the SaaS Applications table, click Create new. The Create SaaS Application Rules pane opens.
-
Set the Application to dropbox, then click Next.
-
Enable Logging.
-
In the Privilege Control table, select download-file and from the Set Action dropdown, select Bypass.
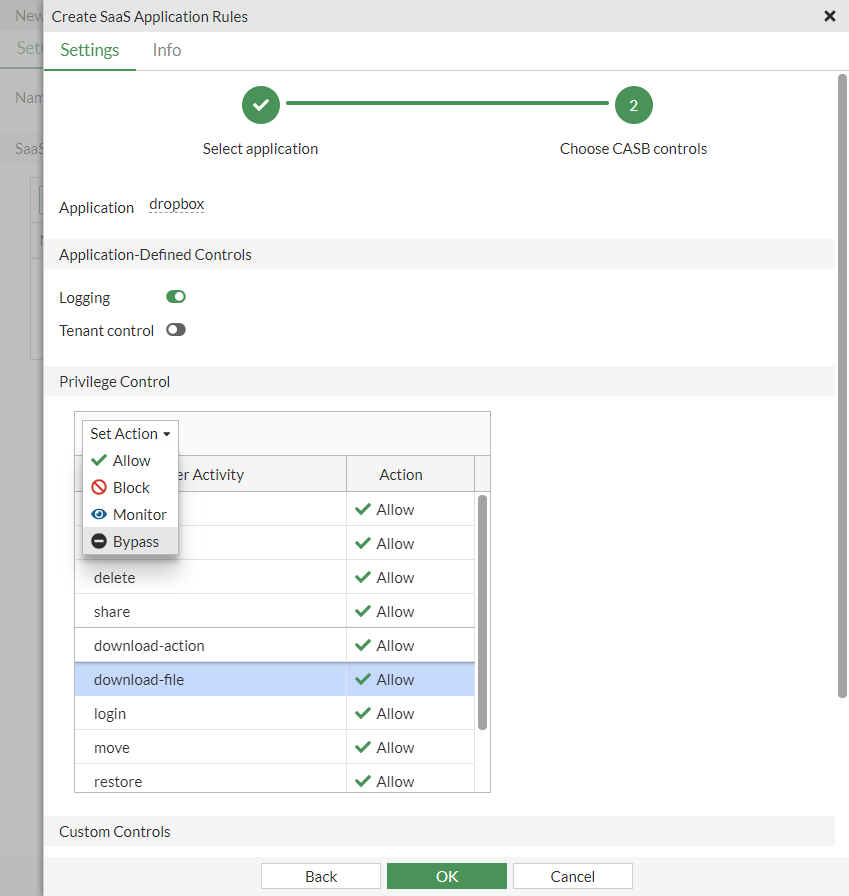
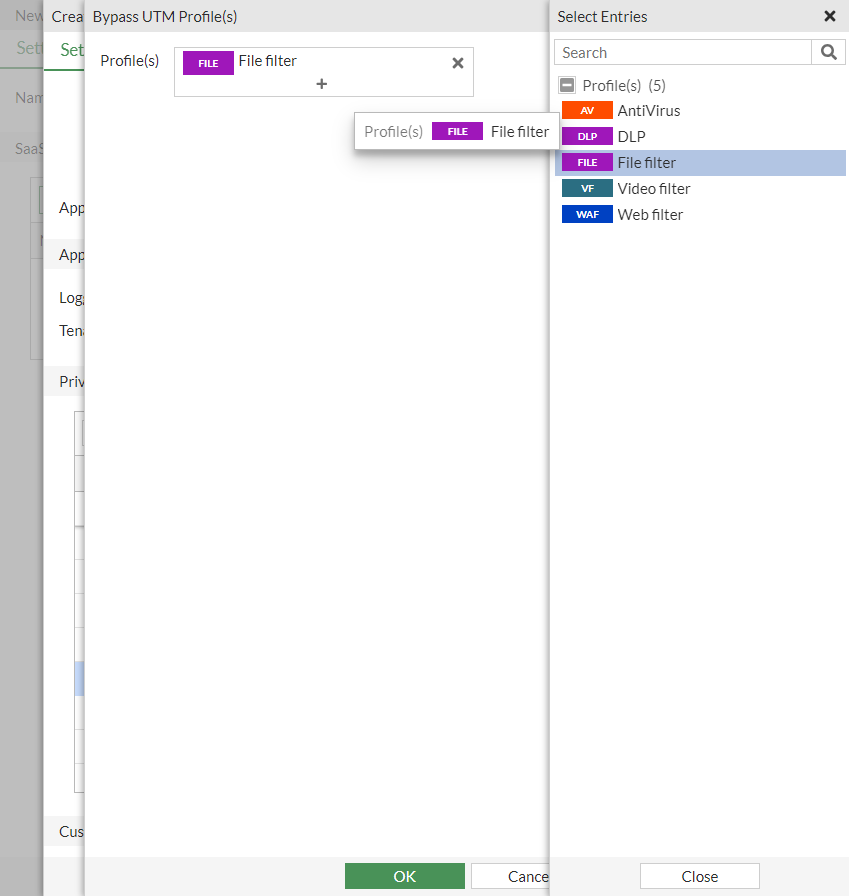
The Bypass UTM Profile(s) pane opens.
-
Click the + and set Profile(s) to File Filter.
-
Click OK to save the bypass UTM profile.
-
Click OK to save the inline CASB profile
-
-
Configure the firewall policy:
-
Go to Policy & Objects > Firewall Policy. Edit an existing policy, or create a new one.
-
Set the Inspection Mode to Proxy-based.
-
In the Security Profiles section, enable Inline-CASB and select the dropbox_test profile.
-
Set the SSL Inspection profile to one that uses deep inspection.
-
Configure the other settings as needed.
-
Click OK.
-
To configure an inline CASB profile with UTM bypass in the CLI:
-
Configure the inline CASB profile:
config casb profile edit "dropbox_test" config saas-application edit "dropbox" config access-rule edit "dropbox-download-file" set bypass file-filter set action bypass next end next end next end -
Configure the firewall policy:
config firewall policy edit 9 set name "casb_test_dropbox" set srcintf "port1" set dstintf "port3" set action accept set srcaddr "all" set dstaddr "all" set schedule "always" set service "ALL" set utm-status enable set inspection-mode proxy set ssl-ssh-profile "ssl" set casb-profile "dropbox_test" set nat enable next end
To test the configuration:
-
Open a browser and log in to Dropbox.
-
Attempt to download a file, such as a PDF. The download is successful.
Sample log:
1: date=2023-08-18 time=17:15:29 eventtime=1692404129378193492 tz="-0700" logid="2500010001" type="utm" subtype="casb" eventtype="casb" level="information" vd="vdom1" msg="CASB access was allowed although it contained activity." policyid=9 sessionid=65452 srcip=10.1.100.195 dstip=162.125.1.15 srcport=62110 dstport=443 srcintf="port1" srcintfrole="undefined" dstintf="port3" dstintfrole="undefined" proto=6 action="bypass" profile="dropbox_test" saasapp="dropbox" useractivity="dropbox-download-file" activitycategory="activity-control"
Example 5: customized SaaS application and user activity
In this example, a custom SaaS application is created (pc4) with a custom user action. When a user accesses pc4.qa.fortinet.com/virus, they are redirected to pc4.qa.fortinet.com/testweb/testweb.htm.
To configure a customized inline CASB profile in the GUI:
-
Configure the inline CASB profile:
-
Go to Security Profiles > Inline-CASB and click Create new.
-
Enter a Name, such as custom_test.
-
In the SaaS Applications table, click Create new. The Create SaaS Application Rules pane opens.
-
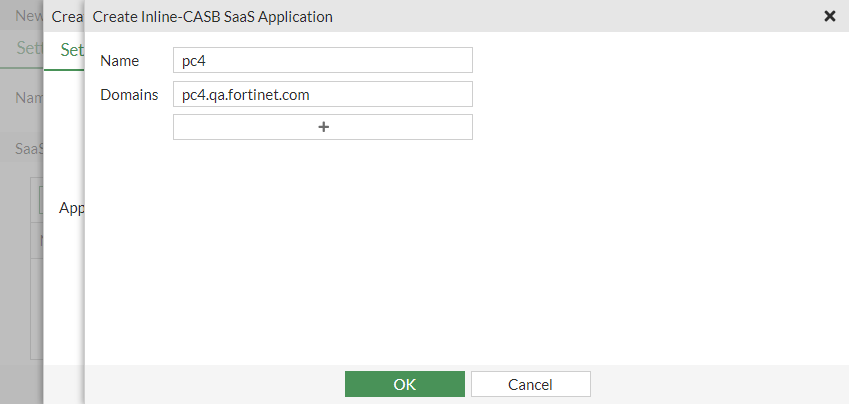
In the Application dropdown, click the + to create a custom entry. The Create Inline-CASB SaaS Application pane opens.
-
Enter the Name (pc4) and Domains (pc4.qa.fortinet.com), then click OK.
-
Select pc4 and click Next.
-
Configure the custom control and action:
-
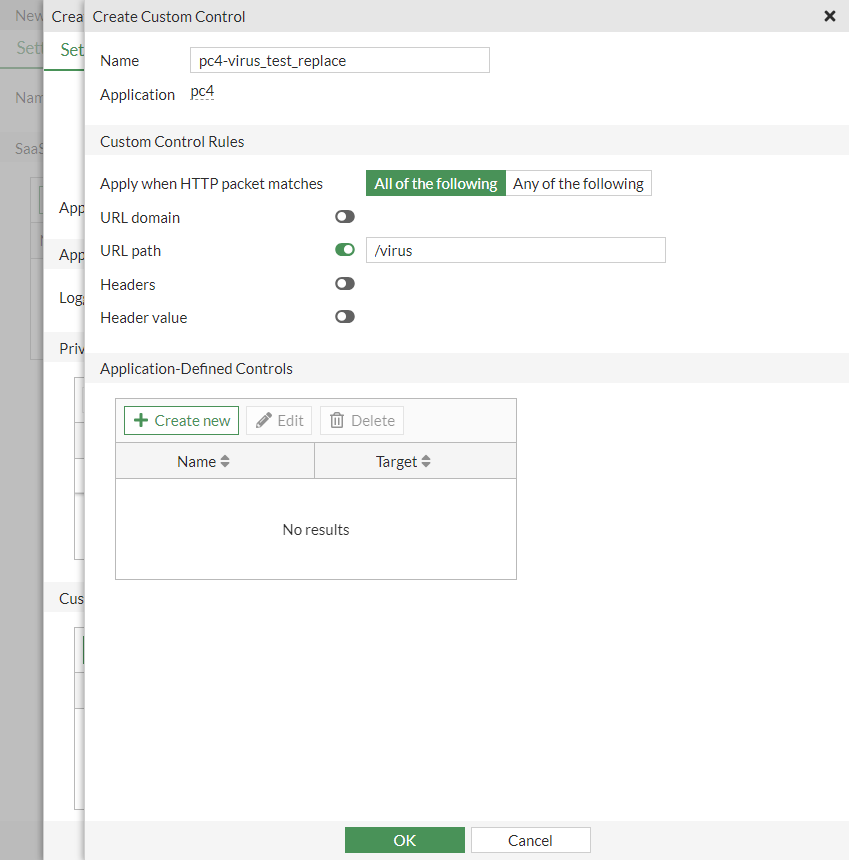
In the Custom Controls table, Create new. The Create Custom Control pane opens.
-
Enter a Name, such as pc4-virus_test_replace.
-
Set Apply when HTTP packet matches to All of the following.
-
Enable URL path and enter /virus.
-
In the Application-Defined Controls table, Create new. The Create Custom Control Action pane opens.
-
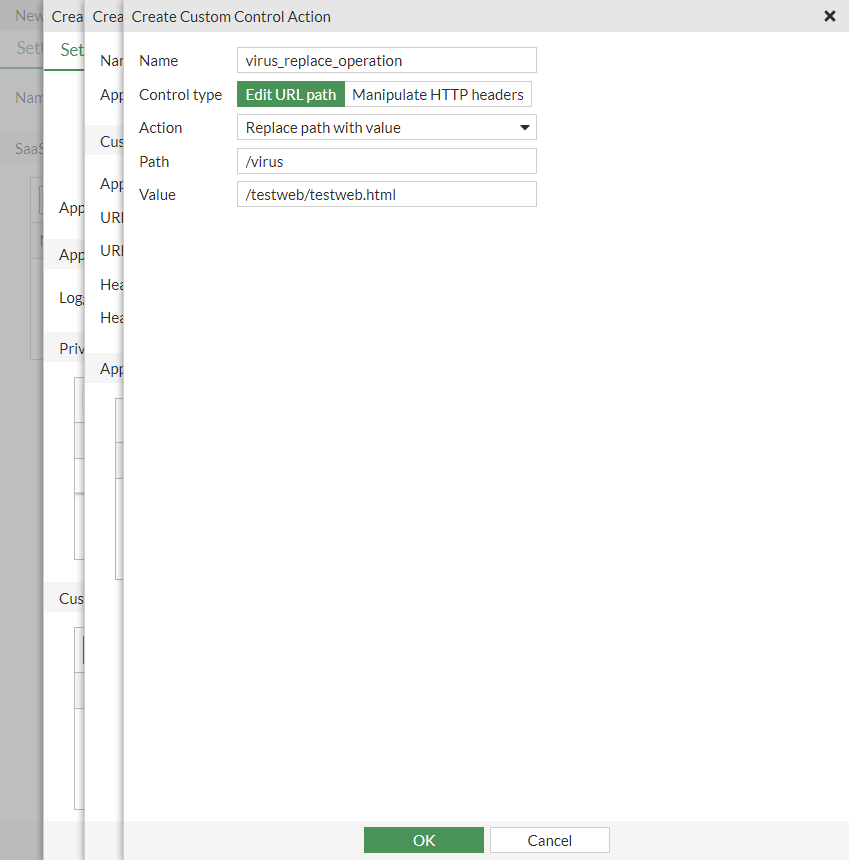
Enter a Name, such as virus_replace_operation.
-
Set the Control Type to Edit URL path.
-
Set the Action to Replace path with value.
-
Set the Path to /virus.
-
Set the Value to /testweb/testweb.html.
-
Click OK to save the custom action.
-
Click OK to save the custom control.
-
-
Click OK to save the application rule.
-
Click OK to save the inline CASB profile.
-
-
Configure the firewall policy:
-
Go to Policy & Objects > Firewall Policy. Edit an existing policy, or create a new one.
-
Set the Inspection Mode to Proxy-based.
-
In the Security Profiles section, enable Inline-CASB and select the custom_test profile.
-
Set the SSL Inspection profile to one that uses deep inspection.
-
Configure the other settings as needed.
-
Click OK.
-
To configure a customized inline CASB profile in the CLI:
-
Configure the CASB SaaS application:
config casb saas-application edit "pc4" set domains "pc4.qa.fortinet.com" next end -
Configure the CASB user activity:
config casb user-activity edit "pc4-virus_test_replace" set application "pc4" set category other config match edit 1 config rules edit 1 set type path set match-value "/virus" next end next end config control-options edit "virus_replace_operation" config operations edit "virus_replace_operation" set target path set action replace set search-key "/virus" set values "/testweb/testweb.html" next end next end next end -
Configure the inline CASB profile:
config casb profile edit "custom_test" config saas-application edit "pc4" config custom-control edit "pc4-virus_test_replace" config option edit "virus_replace_operation" next end next end next end next end -
Configure the firewall policy:
config firewall policy edit 10 set name "casb_test_custom" set srcintf "port1" set dstintf "port3" set action accept set srcaddr "all" set dstaddr "all" set schedule "always" set service "ALL" set utm-status enable set inspection-mode proxy set ssl-ssh-profile "ssl" set casb-profile "custom_test" set nat enable next end
To test the configuration:
-
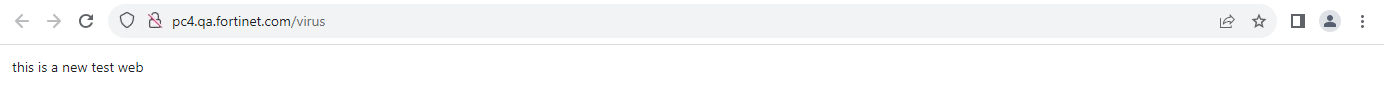
Open a browser and go to pc4.qa.fortinet.com/virus.
-
Access is redirected to pc4.qa.fortinet.com/testweb/testweb.htm.
Sample log:
1: date=2023-08-21 time=08:31:06 eventtime=1692631866382806917 tz="-0700" logid="2500010001" type="utm" subtype="casb" eventtype="casb" level="information" vd="vdom1" msg="CASB access was allowed although it contained activity." policyid=10 sessionid=3139 srcip=10.1.100.195 dstip=172.16.200.44 srcport=56774 dstport=80 srcintf="port1" srcintfrole="undefined" dstintf="port3" dstintfrole="undefined" proto=6 url="http://pc4.qa.fortinet.com/testweb/testweb.html" action="bypass" profile="custom_test" saasapp="pc4" useractivity="pc4-virus_test_replace" activitycategory="other"

