Creating the Edge policy package
Complete the following tasks to configure the policy package for Edge devices:
- Create an policy package named Edge, and assign it to the Edge device group. See Creating an Edge policy package.
- Create firewall policy rules for the Edge policy package. See Creating firewall policy rules.
See also Notes about the Edge policy package.
Creating an Edge policy package
Create a policy package named Edge, and assign the policy package to the Edge device group.
To create an Edge policy package:
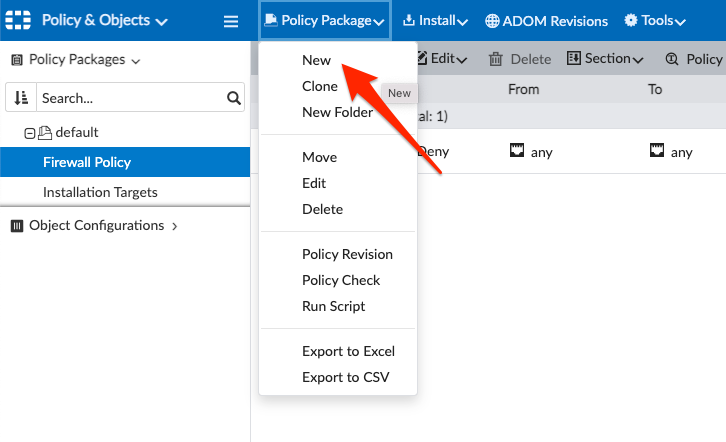
- In Policy & Objects, click Policy Package > New, and create a package named Edge:
- Select Policy Packages > Edge > Installation Targets, and click Edit to assign the package to the Edge device group:

Creating firewall policy rules
Create firewall policy rules for the Edge policy package.
To create firewall policy rules:
- Go to Select Policy Packages > Edge > Firewall Policy.
- Click Create New to create the following firewall policy rules. All the rules should have Action set to Accept:
Name
From
To
Src
Dst
Service
NAT
Corporate
lan_zone overlay
lan_zone overlay
CORP_LAN
CORP_LAN
ALL
No
Internet (DIA)
lan_zone
underlay
all
all
ALL
Yes
Internet (RIA)
lan_zone
overlay
all
all
ALL
No
Health-Check
overlay
Lo
all
all
PING
No

Notes about the Edge policy package
- The Normalized Interfaces for SD-WAN zones named underlay and overlay were automatically created when we configured SD-WAN templates.
- The Normalized Interface for the LAN Zone (lan_zone) was created by us manually, and our Jinja CLI Template (Edge-Underlay) will create the corresponding System Zone on the Edge devices.
- The Firewall Policies distinguish between Direct Internet Access (DIA, from the Edge itself) and Remote Internet Access (RIA, through the Hub), potentially applying different security features in each case. One common example is Source NAT which is only applied to the traffic using DIA.
- In the BGP on loopback design method, Edge devices will probe each other's loopback interfaces (for ADVPN Shortcut Monitoring feature). This must be explicitly permitted by Firewall Policies, as we do in the Health-Check rule.

In the BGP per overlay design method, this rule is not required.
- It is highly recommended enabling Application Control, especially on the Firewall Policy controlling Internet traffic. For accurate application identification, it is also highly recommended to enable SSL Inspection for security reasons, but also for the SD-WAN functionality. Remember that Application Control is required for SD-WAN application-aware traffic steering and is also used to populate SD-WAN widgets and reports.

