ZTNA IP MAC based access control example
In this example, firewall policies are configured that use security posture tags to control access between on-net devices and an internal web server. This mode does not require the use of the access proxy, and only uses security posture tags for access control. Traffic is passed when the FortiClient endpoint meets two conditions.
-
It is tagged with the Domain-Users security posture tag, identifying the device as logged on to the Domain.
-
It has the High importance classification tag indicating the device is High importance and low risk.
Traffic is denied when the FortiClient endpoint is tagged with Malicious-File-Detected.
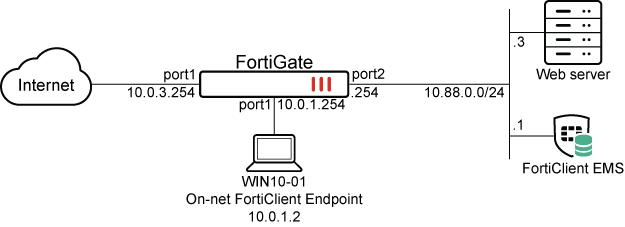
This example assumes that the FortiGate EMS fabric connector is already successfully connected, and a domain has been added to the FortiClient EMS. See Security Fabric connectors and Adding endpoints using an AD domain server
To configure ZTNA in the GUI, go to System > Feature Visibility and enable Zero Trust Network Access.
To configure Zero Trust tagging rules on the FortiClient EMS:
-
Log in to the FortiClient EMS.
-
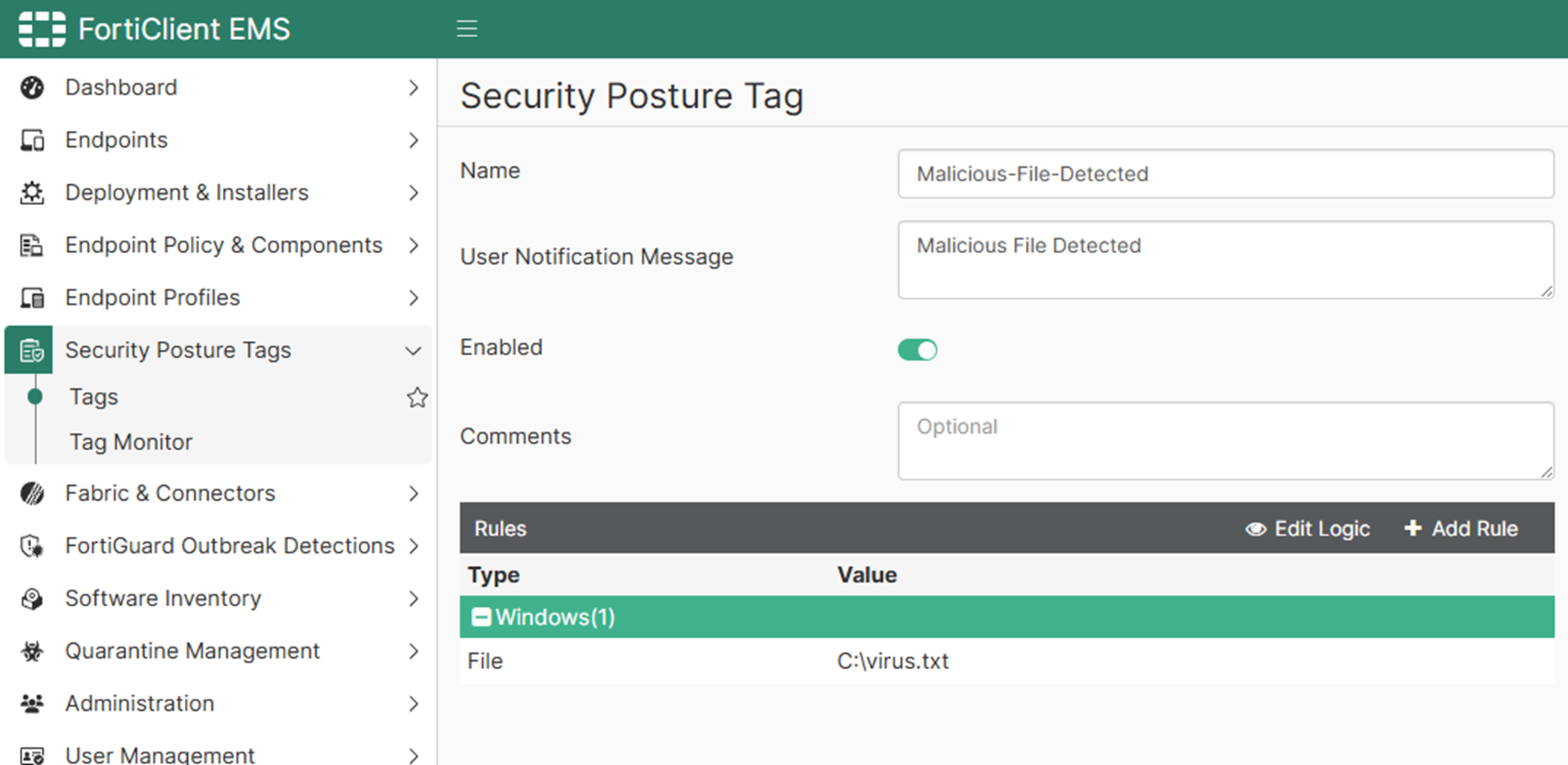
Go to Security Posture Tags > Tags, and click Create.
-
In the Name field, enter Malicious-File-Detected.
-
Specify a User Notification Message, such as Malicious File Detected.
-
Click Add Rule then configure the rule:
-
For OS, select Windows.
-
From the Rule Type dropdown list, select File.
-
Enter a file name, such as C:\virus.txt.
-
Click Save.
-
-
Click Save.
-
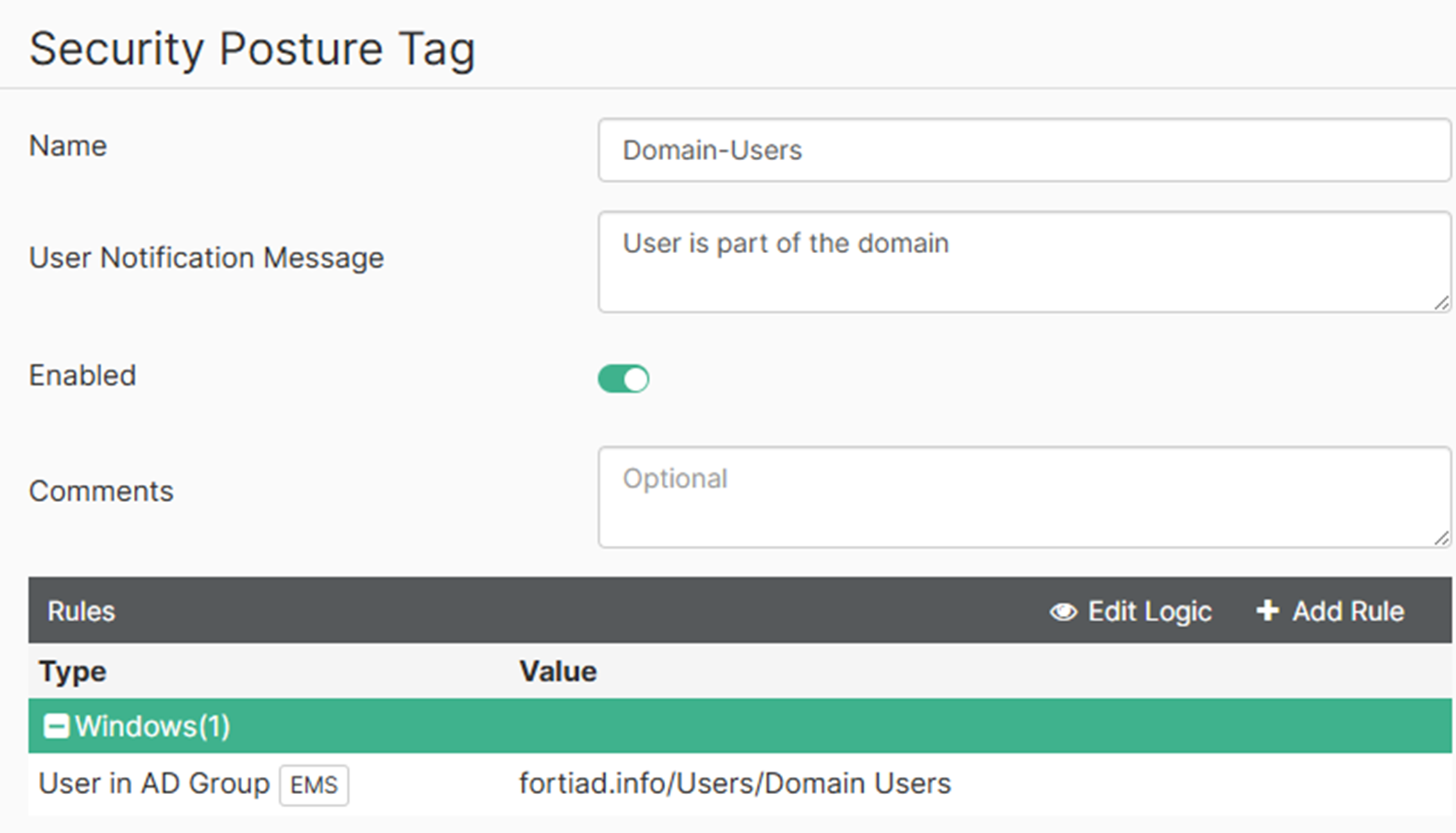
Click Create again.
-
In the Name field, enter Domain-Users.
-
Specify a User Notification Message, such as User is part of the domain.
-
Click Add Rule then configure the rule:
-
For OS, select Windows.
-
From the Rule Type dropdown list, select User in AD Group.
-
For AD Group, select the Domain-Users AD group.
-
Click Save.
-
-
Click Save.
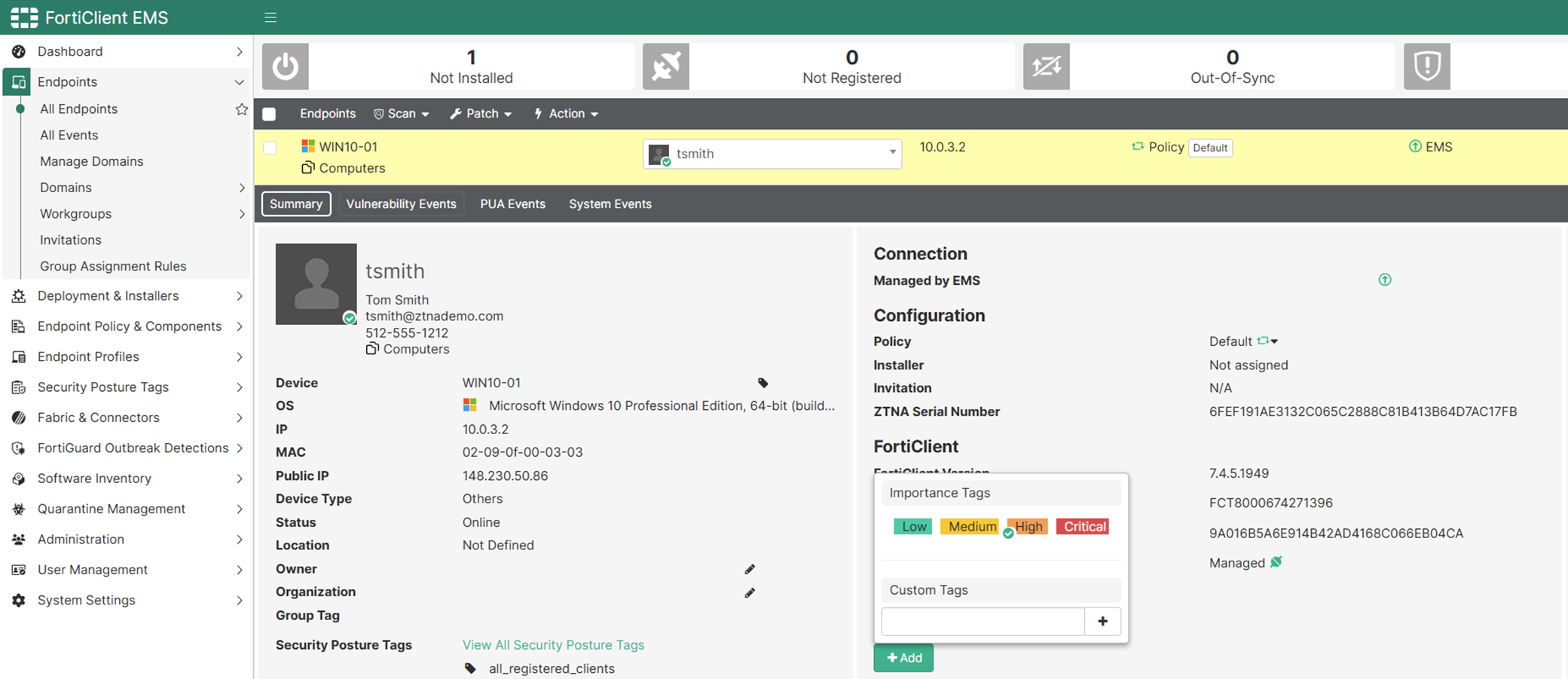
To configure a classification tag on the FortiClient EMS:
-
Go to Endpoint > All Endpoints.
-
Select the computer that will be granted access. This computer should be already registered to FortiClient EMS.
-
In the Summary tab, under Classification Tags, click Add and then set to High Importance.
-
Go to Fabric & Connectors > Fabric Devices.
-
Select the connecting FortiGate, then click the icon with the square and pencil to edit the FortiGate connector.
-
Under Tag Types Being Shared, add Classification Tags.
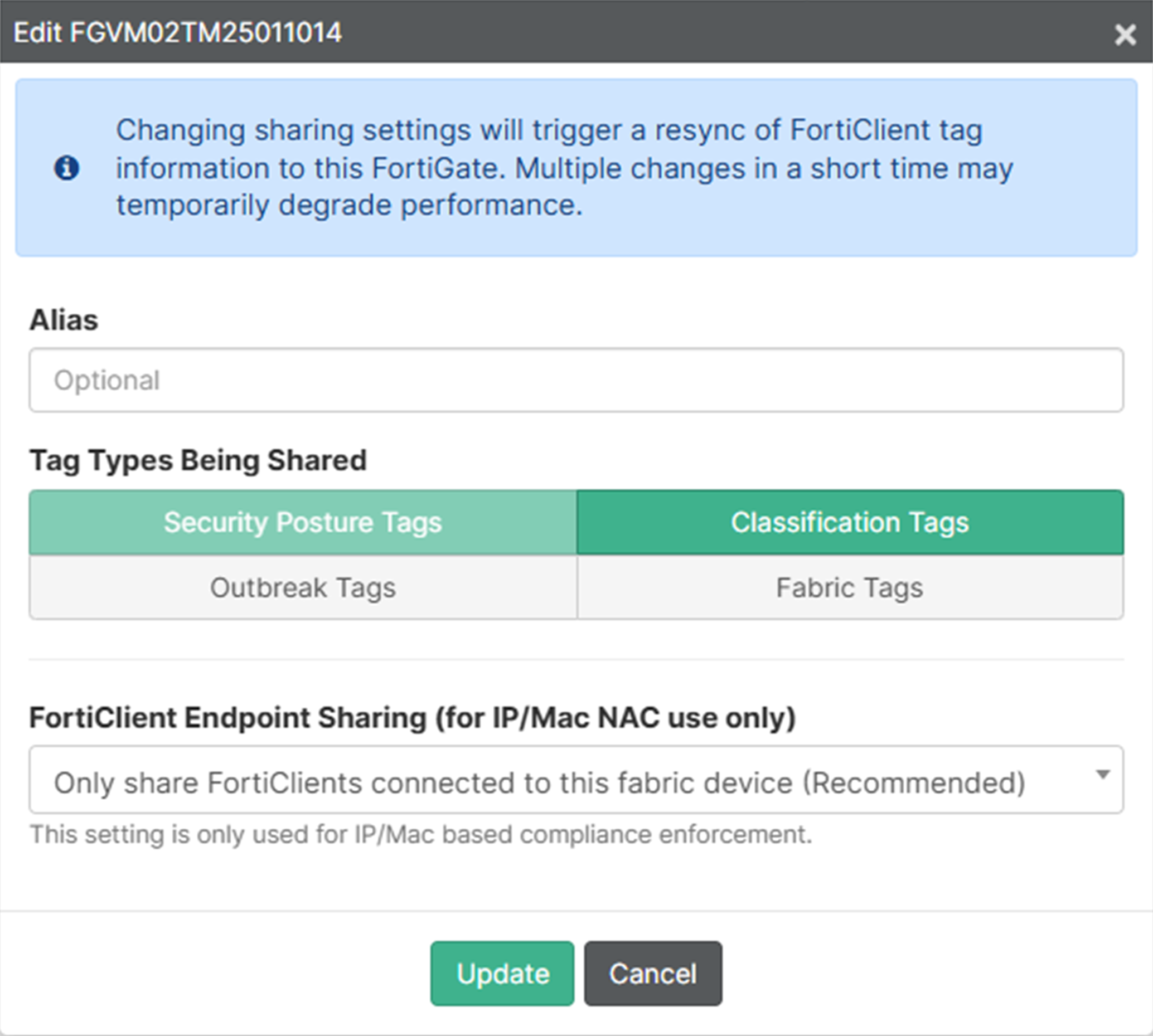
-
Click Update. The connector should reflect two black tags to indicate two tag types being shared.
To configure a firewall policy with IP/MAC based access control to deny traffic in the GUI:
-
Go to Policy & Objects > Firewall Policy and click Create New.
-
Set Name to block-internal-malicious-access.
-
Set Action to DENY.
-
Set Type to Standard.
-
Set Incoming Interface to port1.
-
Set Outgoing Interface to port2.
-
Set Source to all.
-
Enable Security posture tag and select [IP TAG] Malicious-File-Detected.
-
Set Destination to the address of the Web server. If no address is created, create a new address object for 10.88.0.3/32.
-
Set Service to ALL.
-
Enable Log Violation Traffic.
-
Configuring the remaining settings as needed.
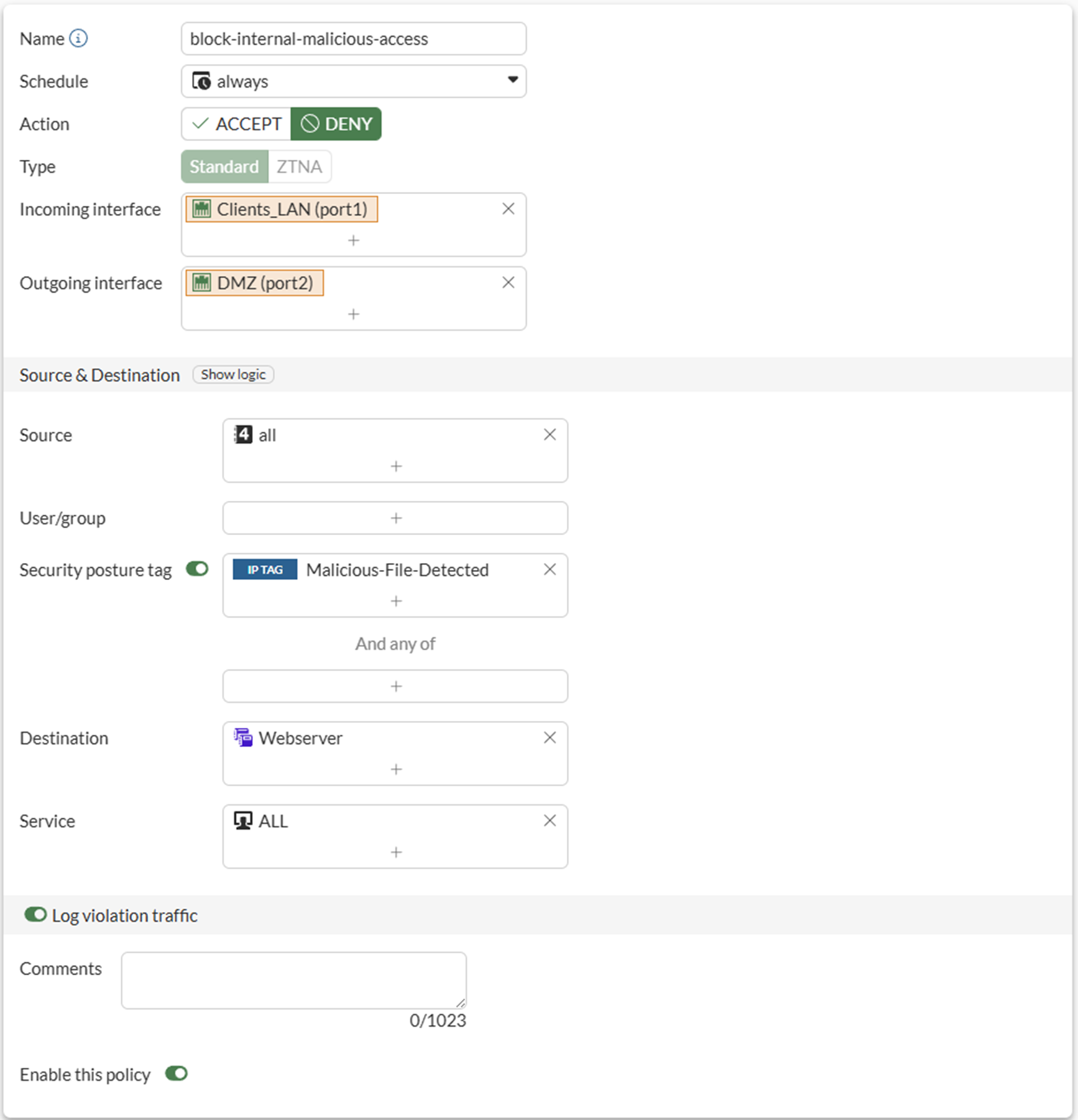
-
Click OK.
To configure a firewall policy with IP/MAC based access control to allow access in the GUI:
-
Go to Policy & Objects > Firewall Policy and click Create New.
-
Set Name to allow-internal-access.
-
Set Action to ACCEPT.
-
Set Type to Standard.
-
Set Incoming interface to port1.
-
Set Outgoing interface to port2.
-
Set Source to all.
-
Enable Security posture tag and select [MAC TAG] Domain-Users, and set the And any of field to [CLASS MAC] High.
The secondary group of tags is used with a logical And operator. The secondary group tags can be same or different types than the primary group.
-
Set Destination to the address of the Web server.
-
Set Service to ALL.
-
Enable Log allowed traffic and set it to All Sessions.
-
Configuring the remaining settings as needed.
-
Click OK.
To configure firewall policies with IP/MAC based access control to block and allow access in the CLI:
config firewall policy
edit 17
set name "block-internal-malicious-access"
set srcintf "port1"
set dstintf "port2"
set ztna-status enable
set srcaddr "all"
set dstaddr "Webserver"
set ztna-ems-tag "EMS1_ZTNA_Malicious-File-Detected"
set schedule "always"
set service "ALL"
set logtraffic all
next
edit 19
set name "allow-internal-access"
set srcintf "port1"
set dstintf "port2"
set action accept
set ztna-status enable
set srcaddr "all"
set dstaddr "Webserver"
set ztna-ems-tag "MAC_EMS1_ZTNA_Domain-Users"
set ztna-ems-tag-secondary "MAC_EMS1_CLASS_High"
set schedule "always"
set service "ALL"
set logtraffic all
set nat enable
next
end
When multiple tags are selected with set ztna-ems-tag <tags>, matching occurs using a logical OR operator. Any single tag that matches will return true.
The set ztna-ems-tag-secondary <tags> command allows a second group of tags to be specified that is used with a logical And operator. The secondary group tags can be same or different types than the primary group.
The set ztna-tags-match-logic {and | or} command does not change the logical operator. It is applied by WAD to tags selected for ZTNA proxy-policy.
Testing the access to the web server from the on-net client endpoint
Access allowed:
-
On the internal PC, open FortiClient.
-
On the Zero Trust Telemetry tab, make sure that you are connected to the EMS server.
-
Open a browser and enter the address of the server.
-
The FortiGate matches your security posture by verifying your security posture tags and matching the corresponding
allow-internal-accessfirewall policy, and you are allowed access to the web server.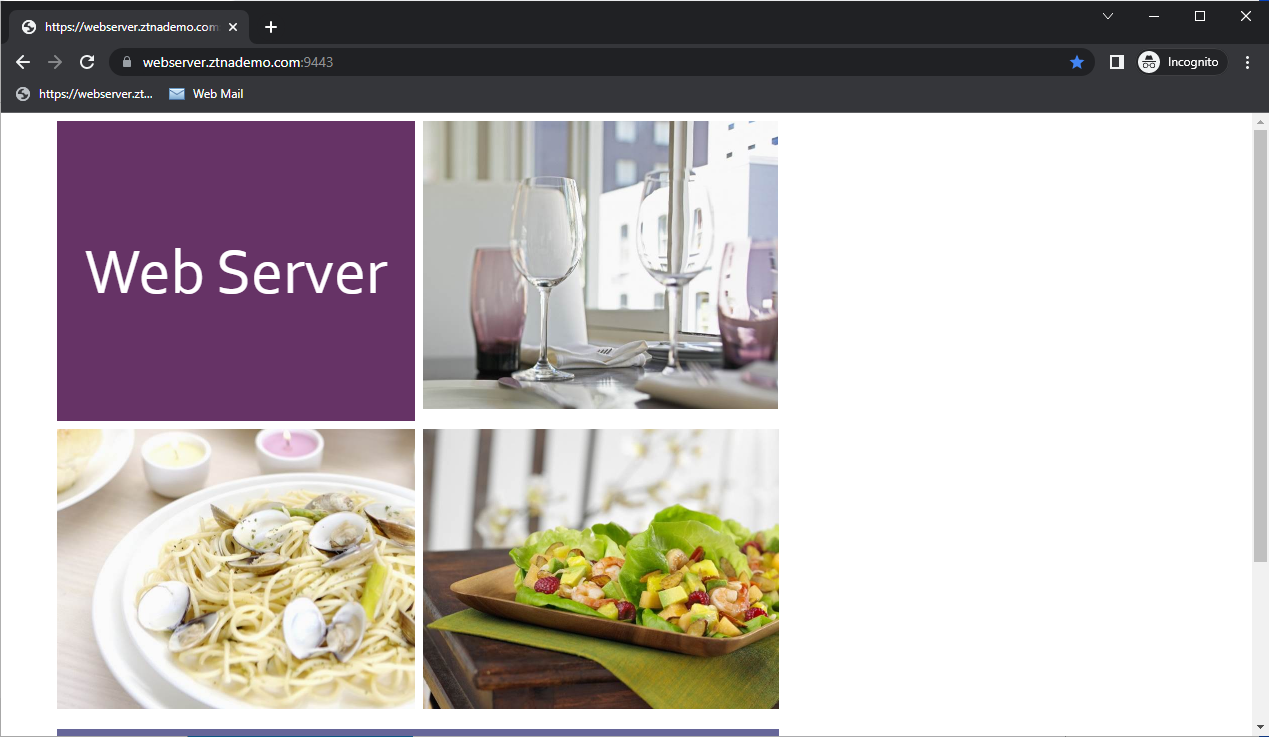
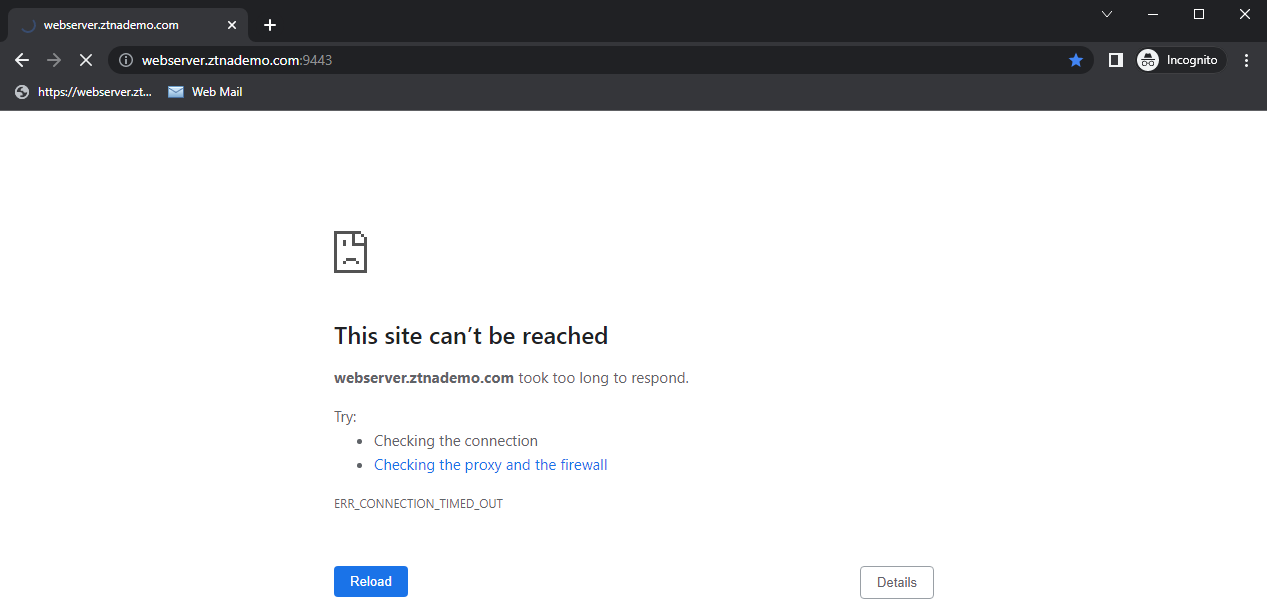
Access denied:
-
On the internal PC, trigger the Zero Trust Tagging Rule by creating the file in C:\virus.txt.
-
Open a browser and enter the address of the server.
-
FortiGate checks your security posture. Because EMS has tagged the PC with the Malicious-File-Detected tag, it matches the block-internal-malicious-access firewall policy.
-
You are denied access to the web server.
Logs and debugs
Access allowed:
# diagnose endpoint ec-shm list
Record #0:
IP Address = 10.0.1.2
MAC Address = 02:09:0f:00:01:02
MAC list =
VDOM = root (0)
EMS serial number: FCTEMS8825007166
EMS tenant id: 00000000000000000000000000000000
Client cert SN: 6FEF191AE3132C065C2888C81B413B64D7AC17FB
Public IP address: 148.230.50.86
Quarantined: no
Online status: online
Registration status: registered
On-net status: off-net
Gateway Interface: port1
FortiClient version: 7.4.5
AVDB version: 1.0
FortiClient app signature version: 35.189
FortiClient vulnerability scan engine version: 3.15
FortiClient UID: 9A016B5A6E914B42AD4168C066EB04CA
Host Name: WIN10-01
OS Type: WIN64
OS Version: Microsoft Windows 10 Professional Edition, 64-bit (build 19045)
Domain: fortiad.info
Last Login User: tsmith
Owner: @fortiad.info
Host Model: Standard PC (i440FX + PIIX, 1996)
Host Manufacturer: QEMU
CPU Model: Intel Xeon Processor (SapphireRapids)
Memory Size: 8095
AV Feature: 1
FW Feature: 1
WF Feature: 1
AS Feature: 0
VS Feature: 1
VN Feature: 1
Last vul message received time: Tue Mar 24 12:10:47 2026
Last vul scanned time: Sun Mar 22 07:00:03 2026
Last vul statistic: critical=0, high=0, medium=0, low=3, info=0
Avatar fingerprint:
Avatar source username: Tom Smith
Avatar source email:
Avatar source: OS
Phone number:
Issued time in seconds: 1774379409
JWT expiry time in seconds: 0 (Current time in seconds: 1774380150)
Subscribed only: false
Sendall: disabled
Number of Routes: (1)
Gateway Route #0:
- IP:10.0.1.2, MAC:02:09:0f:00:01:02, VPN: no
- Interface:port1, VDOM:root (0), SN: FGVM02TM25011014
- Gateway IP:0.0.0.0, MAC:02:09:0f:00:03:01
# diagnose wad dev query-by uid 9A016B5A6E914B42AD4168C066EB04CA FCTEMS8825007166 00000000000000000000000000000000 Attr of type=0, length=83, value(ascii)=9A016B5A6E914B42AD4168C066EB04CA Attr of type=7, length=8, value(ascii)=i Attr of type=4, length=13, value(ascii)=@fortiad.info Attr of type=6, length=1, value(ascii)=true Attr of type=9, length=1, value(ascii)=1 Attr of type=5, length=40, value(ascii)=6FEF191AE3132C065C2888C81B413B64D7AC17FB Attr of type=3, length=76, value(ascii)=ZTNA_all_registered_clients_FCTEMS882500716600000000000000000000000000000000 Attr of type=3, length=66, value(ascii)=ZTNA_Domain-Users_FCTEMS882500716600000000000000000000000000000000 Attr of type=3, length=59, value(ascii)=CLASS_High_FCTEMS882500716600000000000000000000000000000000 Response termination due to no more data
# diagnose firewall dynamic list
List all dynamic addresses:
...
MAC dynamic addresses in VDOM root(vfid: 0):
...
CMDB name: MAC_EMS1_ZTNA_Domain-Users
TAG name: Domain-Users
MAC_EMS1_ZTNA_Domain-Users: ID(153)
MAC(02:09:0f:00:01:02)
Total MAC dynamic addresses: 1.
...
CMDB name: MAC_EMS1_CLASS_High
TAG name: High
MAC_EMS1_CLASS_High: ID(52)
MAC(02:09:0f:00:01:02)
Total MAC dynamic addresses: 1.
...
CMDB name: MAC_EMS1_ZTNA_Domain-Users
TAG name: Domain-Users
MAC_EMS1_ZTNA_Domain-Users: ID(153)
MAC(02:09:0f:00:01:02)
Total MAC dynamic addresses: 1.# diagnose test application fcnacd 7 #ID:0 UID: 9A016B5A6E914B42AD4168C066EB04CA EMS: FCTEMS8825007166 00000000000000000000000000000000 State: sysinfo:1, tag:1, tagsz:1, out-of-sync:0, ref:1 Owner: @fortiad.info Cert SN: 6FEF191AE3132C065C2888C81B413B64D7AC17FB online: Yes Sub TS: 1774380310 Route IP:10.0.1.2, vdom:root(0) idx:0, ttdl:1 name:all_registered_clients idx:2, ttdl:1 name:Domain-Users idx:3, ttdl:2 name:High
# execute log filter field srcip 10.0.1.2 # execute log display 1: date=2026-03-24 time=12:15:29 eventtime=1774379729258821761 tz="-0700" logid="0000000013" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.0.1.2 srcport=8290 srcintf="port1" srcintfrole="undefined" dstip=10.88.0.3 dstport=9043 dstintf="port2" dstintfrole="dmz" srcuuid="b458a65a-f759-51ea-d7df-ef2e750026d1" dstuuid="592dfb72-0775-51ec-aa79-94bd9894388c" emstag="MAC_EMS1_ZTNA_Domain-Users" emstag2="MAC_EMS1_CLASS_High" srccountry="Reserved" dstcountry="Reserved" sessionid=41193 proto=6 action="close" policyid=19 policytype="policy" poluuid="6006181c-27b4-51f1-02e2-dbc9951e19dd" policyname="allow-internal-access" service="tcp/9043" trandisp="snat" transip=10.88.0.254 transport=8290 appcat="unscanned" duration=3 sentbyte=4095 rcvdbyte=311977 sentpkt=30 rcvdpkt=225 fctuid="9A016B5A6E914B42AD4168C066EB04CA" unauthuser="tsmith" unauthusersource="forticlient" srcdomain="fortiad.info" srcremote=148.230.50.86
Access denied:
# diagnose wad dev query-by uid 9A016B5A6E914B42AD4168C066EB04CA FCTEMS8825007166 00000000000000000000000000000000 Attr of type=0, length=83, value(ascii)=9A016B5A6E914B42AD4168C066EB04CA Attr of type=7, length=8, value(ascii)=i Attr of type=4, length=13, value(ascii)=@fortiad.info Attr of type=6, length=1, value(ascii)=true Attr of type=9, length=1, value(ascii)=1 Attr of type=5, length=40, value(ascii)=6FEF191AE3132C065C2888C81B413B64D7AC17FB Attr of type=3, length=76, value(ascii)=ZTNA_all_registered_clients_FCTEMS882500716600000000000000000000000000000000 Attr of type=3, length=76, value(ascii)=ZTNA_Critical-Vulnerability_FCTEMS882500716600000000000000000000000000000000 Attr of type=3, length=66, value(ascii)=ZTNA_Domain-Users_FCTEMS882500716600000000000000000000000000000000 Attr of type=3, length=59, value(ascii)=CLASS_High_FCTEMS882500716600000000000000000000000000000000 Attr of type=3, length=77, value(ascii)=ZTNA_Malicious-File-Detected_FCTEMS882500716600000000000000000000000000000000 Response termination due to no more data
# diagnose firewall dynamic list
List all dynamic addresses:
...
CMDB name: EMS1_ZTNA_Malicious-File-Detected
TAG name: Malicious-File-Detected
EMS1_ZTNA_Malicious-File-Detected: ID(205)
ADDR(10.0.1.2)
Total IP dynamic ipblocks: 1.
Total IP dynamic range blocks: 0.
Total IP dynamic addresses: 1.# diagnose test application fcnacd 7 #ID:0 UID: 9A016B5A6E914B42AD4168C066EB04CA EMS: FCTEMS8825007166 00000000000000000000000000000000 State: sysinfo:1, tag:1, tagsz:1, out-of-sync:0, ref:1 Owner: @fortiad.info Cert SN: 6FEF191AE3132C065C2888C81B413B64D7AC17FB online: Yes Sub TS: 1774380310 Route IP:10.0.1.2, vdom:root(0) idx:0, ttdl:1 name:all_registered_clients idx:2, ttdl:1 name:Domain-Users idx:3, ttdl:2 name:High idx:4, ttdl:1 name:Malicious-File-Detected
# execute log filter field srcip 10.0.1.2 # execute log filter field policyid 17 # execute log display 2: date=2026-03-25 time=06:10:27 eventtime=1774444227233285909 tz="-0700" logid="0000000013" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.0.1.2 srcport=10313 srcintf="port1" srcintfrole="undefined" dstip=10.88.0.3 dstport=9043 dstintf="port2" dstintfrole="dmz" srcuuid="b458a65a-f759-51ea-d7df-ef2e750026d1" dstuuid="592dfb72-0775-51ec-aa79-94bd9894388c" emstag="EMS1_ZTNA_Malicious-File-Detected" srccountry="Reserved" dstcountry="Reserved" sessionid=68514 proto=6 action="deny" policyid=17 policytype="policy" poluuid="551cbf70-27a3-51f1-619d-0258bb4090b8" policyname="block-internal-malicious-access" service="tcp/9043" trandisp="noop" appcat="unscanned" duration=0 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0 fctuid="9A016B5A6E914B42AD4168C066EB04CA" unauthuser="tsmith" unauthusersource="forticlient" srcdomain="fortiad.info" srcremote=148.230.50.86 crscore=30 craction=131072 crlevel="high"

