Cookie Security
FortiAppSec Cloud can protect against cookie poisoning and other cookie-based attacks. When Cookie Security module is added FortiAppSec Cloud signs all cookies by default.
To create cookie security rules
- Go to SECURITY RULES > Cookie Security.
You must have already enabled this module in Add Modules. See Add and Remove Modules. - Configure these settings.
Cookie Replay Protection
Enable to select whether FortiAppSec Cloud uses the IP address of a request to determine the owner of the cookie and protect against replay attacks.
Set Max Cookie Age
Enter the maximum age (in minutes) permitted for cookies that do not have an “Expires” or “Max-Age” attribute.
To configure no expiry age for cookies, enter
0.Security Mode
- None—FortiAppSec Cloud does not apply cookie tampering protection or encrypt cookie values.
- Signed—Prevents tampering (cookie poisoning) by tracking the cookie value.
When FortiAppSec Cloud receives the first HTTP or HTTPS request from a client, it uses a cookie to track the session. When you select this option, the session-tracking cookie includes a hash value that FortiAppSec Cloud uses to detect tampering with the cookie from the backend server response. If FortiAppSec Cloud determines the cookie from the client has changed, it takes related action. Encrypted—Encrypts cookie values the back-end web server sends to clients. Clients see only encrypted cookies. FortiAppSec Cloud decrypts cookies submitted by clients before it sends them to the back-end server.
Set Secure Cookie
Enable to add the secure flag to cookies, which forces browsers to return the cookie only when the request is for an HTTPS page.
This function applies to the cookie from origin server. If you want to modify the cookie from browser, please refer to Secure flag for internal Cookie in Endpoints.
Set HTTP Only Cookie
Enable to add the "HTTP Only" flag to cookies, which prevents client-side scripts from accessing the cookie.
This function applies to the cookie from origin server. If you want to modify the cookie from browser, please refer to HTTP Only flag for internal Cookie in Endpoints.
Set Same Site Cookie
Enable to restrict cookies that fall outside of a first-party or same-site context.
Same Site Value
Strict — Cookies will not be included in any requests from third parties.
Lax — Cookies will not be included in third-party requests, except for GET requests that navigate to the destination URL.
None —Use this option if a cookie needs to be sent across different origins.
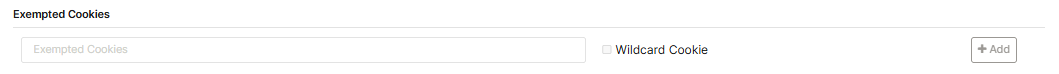
Exempted Cookies
To specify cookies that are exempt from the cookie security policy, click Add to add cookie names.
Matching by exact name and wildcard is supported.
To match cookies with a wildcard, the Wildcard Cookie box beside the Exempted Cookies text field must be checked. If unchecked, the asterisk (*) is treated as a literal character instead of a wildcard.
- Select the action that FortiAppSec Cloud takes when it detects a violation of the rule from the top right corner.
To configure the actions, you must first enable the Advanced Configuration in WAF > System Settings > Settings.Alert
Accept the request and generate a log message.
Alert & Deny
Block the request (or reset the connection) and generate a log message.
Deny(no log)
Block the request (or reset the connection) but do not generate log messages.
Remove Cookie
Accept the request, but remove the cookie from the datagram before it reaches the web server, and generate a log message.
- Click SAVE.

