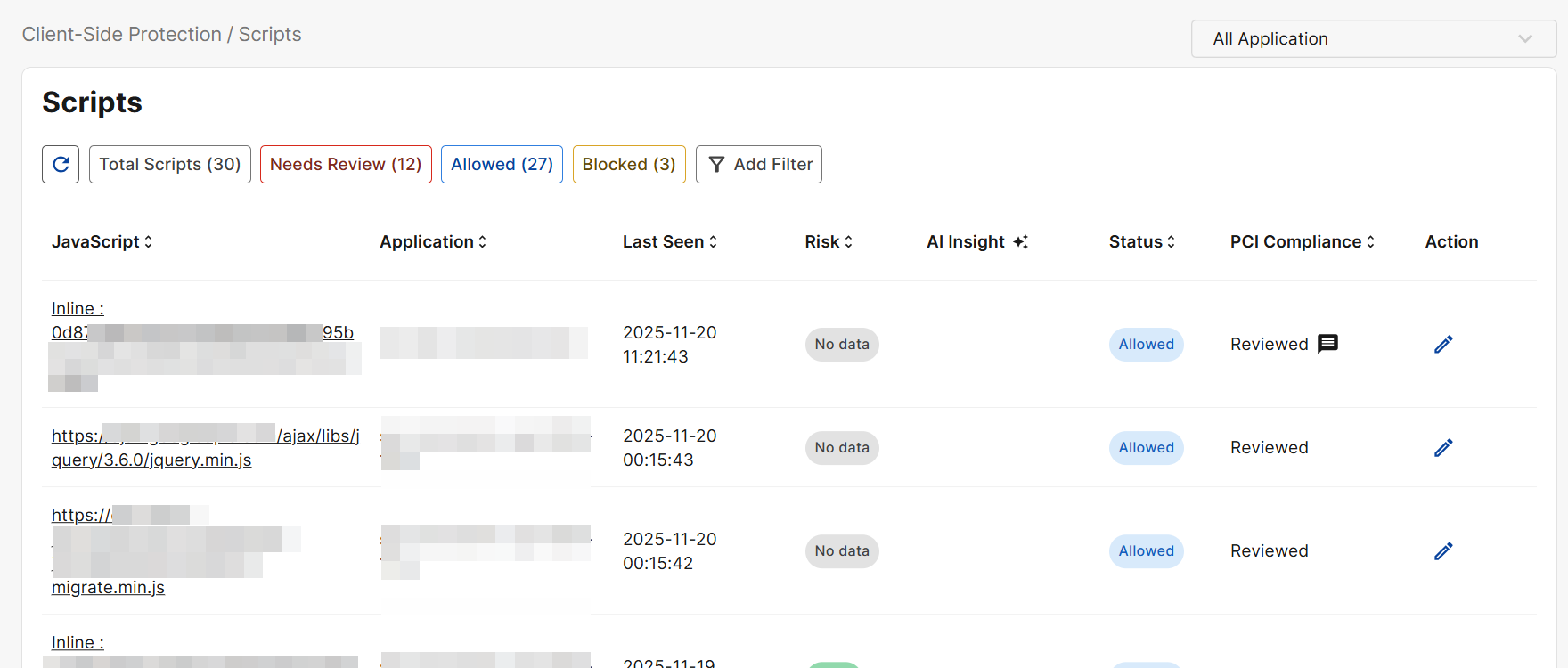
Scripts
Discover and manage browser-executed scripts, including all first- and third-party scripts, with risk levels, last-seen data, and one-click allow/block controls.
PCI DSS 4.0 requires an inventory and justification for every script that executes on the payment page. Tracking script additions, removals, and modifications ensures only approved, intentional scripts run in the customer’s browser.
|
|
Manually reviewing all payment-related scripts is required under PCI DSS. To check the status of the review, see the PCI Compliance column. |
|
Field |
Description |
|---|---|
|
Javascript |
The javascript detected on your application. Click on this value to see Script Details. |
|
Application |
The affected application on which the javascript was detected. |
|
Last Seen |
The most recent time this script was observed running on the application. |
|
Risk |
The Risk is determined by the Risk Score obtained from FortiGuard's web filtering service.
|
|
AI Insight |
The FortiAI Agent uses the collected telemetry data to provide insights on the script. Hover over this value to see all assigned malicious labels associated with the javascript. |
|
Status |
|
|
PCI Compliance |
Indicates whether the script has been reviewed for PCI DSS 4.0 compliance. Click the edit icon under Action to complete the review. Please note that reviewing all payment-related scripts is required under PCI DSS. |
|
Action |
Click the edit icon to review a script for PCI DSS compliance. Please note, the Block action is not yet supported. |
Script Details
Click on a Javascript value on the Scripts page to view its details.
|
Field |
Description |
|---|---|
|
Javascript |
The javascript detected on your application. |
|
Version |
When there are multiple varying iterations of the same script, click compare version to view the differences. |
|
Risk |
The Risk is determined by the Risk Score obtained from FortiGuard's web filtering service.
|
|
From Page |
The URL of the page on which the script was detected. |
|
Type |
|
|
Discovered On |
The date and time when this script was detected for the first time. |
|
Last Seen |
The most recent time this script was observed running on the application. |
|
AI Analysis |
A description of the script based on the telemetry data collected by FortiAI. |
|
Malicious Analysis |
A description of the malicious effects of the script, as analyzed by FortiAI. |
|
Malicious Indicator |
The specific behaviors or attributes that FortiAI determined to be malicious based on its analysis of the script. |
|
Latest Review |
Latest manual review of the script. Please note that reviewing all payment-related scripts is required under PCI DSS.
|

