Configuring RADIUS client on FortiAuthenticator
The FortiAuthenticator has to be configured to allow RADIUS clients to make authorization requests to it.
To create the RADIUS client:
- On the FortiAuthenticator, go to Authentication > RADIUS Service > Clients, and select Create New.
- Enter a Name, the IP address of the FortiGate, and set a Secret.
The secret is a pre-shared secure password that the FortiGate will use to authenticate to the FortiAuthenticator.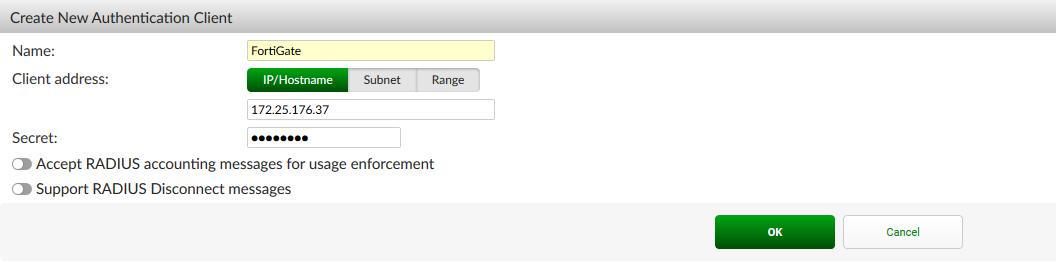
To create the RADIUS policy:
- Go to Authentication > RADIUS Service > Policies, and select Create New.
- Enter the RADIUS policy name, description, and select the FortiGate RADIUS client.
- Do not configure RADIUS attribute criteria.
- Set the authentication type as Password/OTP authentication, and enable Accept EAP with only EAP-TTLS selected.
EAP-TLS should be the only EAP type selected to prevent fallback to a less secure version of authentication if a certificate is not presented by the WiFi client.
- Choose a username format (in this example: username@realm), select the Local realm.
- Set the authentication method to Password only authentication.
- Review the RADIUS response, and click Save and Exit.

