Configuring SAML IdP settings
To configure SAML IdP settings:
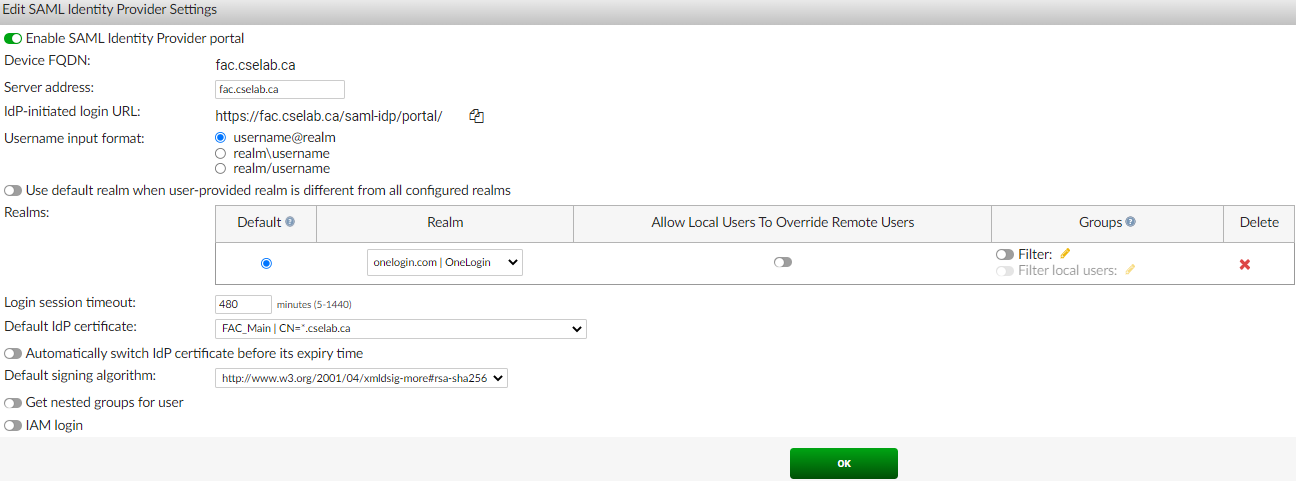
- Go to Authentication > SAML IdP > General, and select Enable SAML Identity Provider portal.
- In Server address, enter the FortiAuthenticator FQDN.

Device FQDN can be configured from the System Information widget in System > Dashboard > Status.
FQDN must be reachable via DNS for users using the service.
- Ensure that Username input format is set as username@realm.
- In the Realms dropdown, select the OneLogin realm configured in Configuring an OneLogin realm .
Optionally, for group filtering, enable Filter, click the pen icon to edit, select groups from the Available User Groups search box, and click OK. This restricts access to a subset of users, e.g., restrict SAML authentication only to a group of 3rd party contractors even though all users may have been imported to FortiAuthenticator.
- Optionally, in login session timeout, adjust the amount of time the user session is valid for, on successful authentication.
- In the Default IdP certificate dropdown, select the local FortiAuthenticator certificate to use to sign SAML requests to SP clients. The certificate is uploaded to the FortiGate SP. See Uploading SAML IdP certificate to the FortiGate SP.
To export the IdP certificate, see Exporting the IdP certificate.
- Ensure that Get nested groups for user is disabled.
- Click OK.
To export the IdP certificate:
- Go to Certificate Management > End Entities > Local Services.
- Select the certificate used in the SAML IdP and click Export Certificate.


As a best practice, the default certificate should not be used as it is less secure than a certificate issued by a trusted Certificate Authority (CA).

