Whatʼs new
The following sections describe new features and enhancements:
Policy based routing
Policy routing allows you to specify an interface to route traffic. This is useful when you need to route certain types of network traffic differently than you would if you were using the routing table. You can use the incoming traffic's protocol, source or destination address, source interface, or port number to determine where to send the traffic.
To configure a policy-based route in the CLI:
config router policy
edit <name>
set input-device <interface>
set src <ip_address/netmask>
set dst <ip_address/netmask>
set action {permit | deny}
set protocol <integer>
set start-port <port>
set end-port <port>
set start-source-port <port>
set end-source-port <port>
set gateway <address>
set output-device <interface>
set status {enable | disable}
set comments <string>
next
end
| input-device <interface> | Incoming interface name. |
| src <ip_address/netmask> | Source IP and mask (x.x.x.x/x). |
| dst <ip_address/netmask> | Destination IP and mask (x.x.x.x/x). |
| action {permit | deny} | Action of the policy route (default = permit). |
| protocol <integer> | Protocol number (0 - 255). |
| start-port <port> | Start destination port number (1 - 65534). |
| end-port <port> | End destination port number (1 - 65534). |
| start-source-port <port> | Start source port number (1 - 65534). |
| end-source-port <port> | End source port number (1 - 65534). |
| gateway <address> | IP address of the gateway. |
| output-device <interface> | Outgoing interface name. |
| status {enable | disable} | Enable/disable this policy route (default = enable). |
| comments <string> | Optional comments. |
Default certificate authority
Default certificate authorities (CA) can be configured and, by default, web-proxy and ssl-ssh-profile use the default CAs:
config firewall ssl default-certificate
set default-ca "Fortinet_CA_SSL"
set default-untrusted-ca "Fortinet_CA_Untrusted"
set default-server-cert "Fortinet_Factory"
endconfig web-proxy global
set ssl-cert "default-server-cert"
set ssl-ca-cert "default-ca"
end
confir firewall ssl-ssh-profile
edit 1
set caname "default-ca"
set untrusted-caname "default-untrusted-ca"
next
end
The CA can be changed by either changing the default, or by setting a specific default for the web-proxy or ssl-ssh-profile. For example, to change the web-proxy CAs, but not the defaults:
config web-proxy global
set ssl-cert "Personal_Server_CA"
set ssl-ca-cert "Personal_CA"
end
Reauthentication mode configuration
Configuring the proxy reauthentication mode has changed.
To configure when users must reauthenticate:
config system global
set proxy-keep-alive-mode {session* | traffic | re-authentication}
set proxy-re-authentication-time <integer>
end
|
proxy-keep-alive-mode {session* | traffic | re-authentication} |
Control if users must reauthenticate after a session is closed, traffic has been idle, or from the point that the user was first created (default = session):
|
|
proxy-re-authentication-time <integer> |
The time limit that users must reauthenticate if |
The following command is no longer available:
config system global
set proxy-re-authentication-mode {session | traffic | abs-time}
end
Embed images in replacement messages
By default, images are embedded in replacement messages instead of using a URL.
To enable/disable embedding images in replacement messages:
config webfilter fortiguard
set embed-image {enable | disable}
end
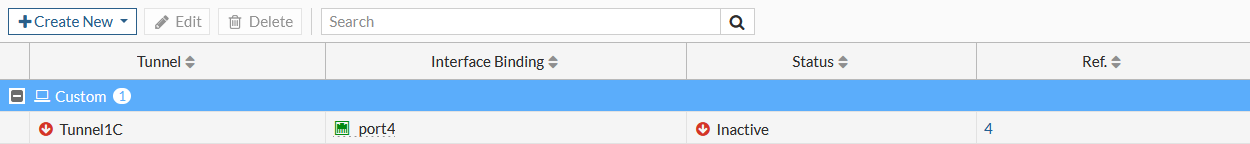
View the IPsec tunnel status in the GUI
Go to VPN > IPsec Tunnels to view the list of tunnels; the Status column shows the status of the tunnel.
Webcache prefetch settings
To download the prefetch log in the GUI, go to Web Cache > Prefetch Monitor and click Download Prefetch Log. To configure a prefetch file in the GUI, go to Web Cache > Prefetch URLs and click Create New. The Web Cache > Prefetch File tree menu item is removed.
The config webcache reverse-cache-prefetch-url command, and the prefetch-file variable under the config webcache reverse-cache-server command, are now in the config webcache prefetch command:
To configure webcache prefetch in the CLI:
config webcache prefetch
edit <name>
set url <url>
set crawl-depth <integer>
set ignore-robots {enable | disable}
set interval <integer>
set start-delay <integer>
set repeat <integer>
set user <string>
set password <password>
set user-agent {chrome edge firefox safari wget}
next
end
|
url <url> |
URL of the target. |
|
crawl-depth <integer> |
Depth to crawl the whole URL (0 - 16, default = 0). |
|
ignore-robots {enable | disable} |
Enable/disable ignoring robots.txt file specifications (default = disable). |
|
interval <integer> |
Time interval to fetch the URL, in seconds (0 - 608400, default = 43200). |
|
start-delay <integer> |
Delay period to start the fetching, in seconds (0 - 2422800, default = 0). |
|
repeat <integer> |
How many times repeat to fetch the URL (0 - 4200000000, default = 0). |
|
user <string> |
Username for the web resource. |
|
password <password> |
Password for the web resource. |
|
user-agent {chrome edge firefox safari wget} |
User agents can be used by this prefetch. |
ICAP server response extension headers
ICAP server responses can be configured to include X-Virus-ID, X-Infection-Found, and X-Violation-Found extension headers.
config icap local-server
edit 1
config icap-service
edit 1
set extension-headers {X-Virus-id X-Infection-Found X-Violation-Found}
next
end
next
end
|
X-Virus-id |
Enable X-Virus-ID ICAP extension header. |
|
X-Infection-Found |
Enable X-Infection-Found ICAP extension header. |
|
X-Violation-Found |
Enable X-Violation-Found ICAP extension header. |
Filter WAD log messages by process types or IDs
WAD log messages can be filtered by process types or IDs. Multiple process type filters can be configured, but only one process ID filter can be configured.
# diagnose wad filter process-type <integer> # diagnose wad filter process-id <integer>
|
diagnose wad filter process-type <integer> |
Select process type to filter by (0 - 17, 0 = disable):
|
|
diagnose wad filter process-id <integer> |
Select process id to filter by (0 = disable). |
To configure multiple filters:
# diagnose wad filter process-type 1 # diagnose wad filter process-type 3 # diagnose wad filter process-type 16 # diagnose wad filter process-id 1115
To view the configured filters:
# diagnose wad filter list
drop unknown sessions: disabled
process type:
manager
worker
traffic aggregator
process id: 1115

